UFP Cyber Compromise, Marseille Ticket Breach, Google Phishing Campaign , Cybersecurity News [February 23, 2026]

Quick Answer
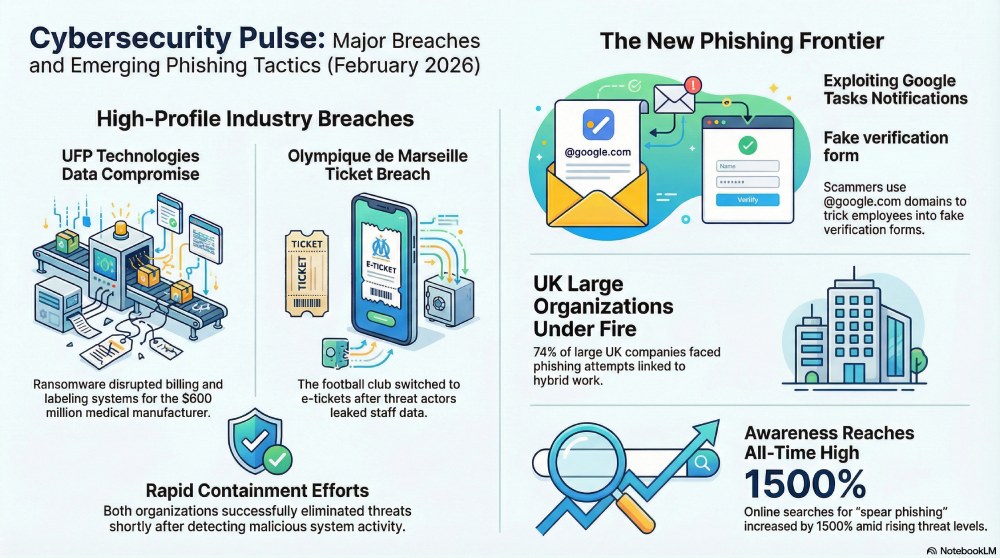
Week 9, 2026 cyber news: medical device maker UFP Technologies (4,300 staff, ~$600M revenue) discloses a Feb 14 cyber incident affecting label and billing systems with sensitive data exfiltrated (no group has claimed responsibility); 126-year-old Olympique de Marseille reissues all entry as e-tickets after attackers leak staff and supporter data; Kaspersky uncovers a phishing campaign abusing legitimate @google.com Google Tasks notifications to harvest corporate logins via fake employee verification pages; UK Cyber Security Breaches Survey 2025 finds 29% of firms hit by remote/hybrid-work phishing (74% of large, 67% of medium), with December 2025 attempts at an all-time high.
UFP Cyber Compromise, Marseille Ticket Breach, Google Phishing Campaign , Cybersecurity News [February 23, 2026]

Here are the top 4 recent cyber incidents that kept the security experts on their toes. The renowned medical equipment manufacturer UFP Technologies was targeted by threat actors. On Wednesday, Olympique de Marseille experienced a cyber mishap, after which the authorities decided to reissue e-tickets. Meanwhile, there has been a sudden spike in phishing attacks on UK organizations. Also, a group of cybercrooks is using @google.com to run a new phishing campaign.
Sensitive data belonging to UFP Technologies has been compromised in a recent cyber incident!
UFP Technologies is an American medical device manufacturing company. It deals in a wide range of medical equipment required for orthopedic applications, surgery, implants, and wound care, etc. With an employee base of 4,300 people, the medical equipment manufacturer generates annual revenue of $600 million.
On Tuesday, it filed with the US Securities and Exchange Commission. The manufacturer noticed malicious activities on its IT systems. This happened back on February 14. UFP Technologies wasted no time and deployed remediation strategies. It has also been taking advice from external cybersecurity advisors.
According to preliminary results of the investigation, UFP Tech believes the cyber threat has been successfully eliminated. However, the threat actors had already managed to wipe away sensitive data.
The cyber incident impacted those IT systems that take care of label making and billing for customers. Company-related data has also been compromised.
Experts believe that it was a ransomware attack, though no official confirmation has been made yet. Also, no threat group has claimed responsibility for the attack on UFP Technologies so far.
Authorities are also investigating whether or not the personal data of clients has been compromised.
Olympique de Marseille reissues e-tickets after cyberattack
OM, an almost 126-year-old professional football club, was targeted by a group of threat actors on Wednesday. The club believes that it was an attempt to break into the IT systems of the club. They managed to contain the attack soon. The authorities have assured that passwords and bank data have not been compromised.
Authorities have decided to take additional safety measures. So physical tickets for a particular match won’t be available. Instead of the physical ticket, the authorities have decided to issue e-tickets for the match. Without an e-ticket, getting an entry at the stadium is barred. So you need to download your e-ticket by logging in and entering your personal details.
A cybercrook has claimed responsibility for the cyberattack this Monday. They have also leaked a screenshot of the leaked data on the dark web. The threat actor has claimed that the stolen data contains sensitive data like staff and supporter information.
Technical teams and other associated service providers did not hesitate to jump into action as soon as they learned of the cyber mishap. The French football club also stated that all its operations are running smoothly without any interferences.
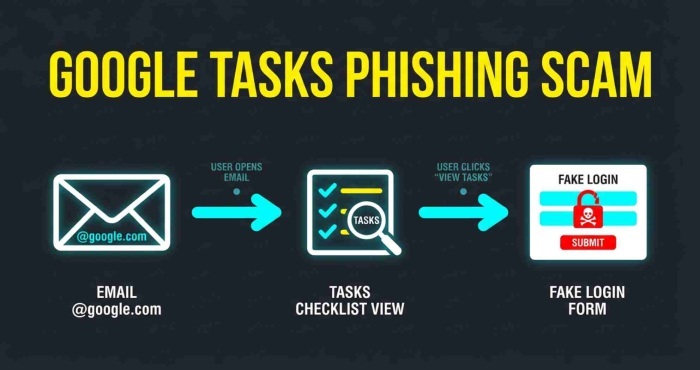
Threat actors are misusing Google to run a new phishing campaign, warns Kaspersky!
A new phishing campaign is doing the rounds, which involves legitimate Google Tasks. The actors have been abusing the @google.com email domain to go undetected through security mechanisms. Also, using popular names like Google increases credibility.
Kaspersky researchers have discovered this new phishing campaign, which involves cybercrooks misusing Google Tasks notifications in order to gain access to the login credentials of corporate employees.
Victims get tricked by a legitimate-looking Google Tasks notification. The subject line of the notification will look like this: “You have a new task.” The notification implies that the organization in which the employee works has started using Google Tasks to streamline internal workflows. In order to boost the success rate of the phishing campaign, threat actors often use proven tactics like short deadlines, urgency markers, and so on.
When the victim clicks on such a notification, they get redirected to a malicious webpage that looks like an employee verification form. Here, victims are required to enter their login details in order to verify their employment status. Cybercrooks can then misuse these login credentials to carry out data theft and similar other threat attacks.
Kaspersky has urged users to avoid clicking on any random notification. It is better to verify the details through official websites.
UK organizations are experiencing a sudden spike in phishing attacks
The remote and hybrid work culture has made employees’ lives a bit easier. But at the same time, it has also increased the risk of cyberattacks. UK enterprises are currently facing phishing attacks left, right, and center, especially those involving remote and hybrid work setups.
According to the Cyber Security Breaches Survey 2025, around 29% of UK enterprises have faced one or more phishing attacks over the last year. Each of these cyberattacks was related to hybrid or remote working systems.
It seems that the threat actors are now targeting organizations based on their size. For example, 74% large organizations experienced phishing attempts. The number was limited to 67% when it comes to medium-sized enterprises.
Nasstar findings also clearly show that phishing attacks were at an all-time high in December 2025.
The positive side of this is that employees are actually getting more aware of the cybersecurity situations. Searches around “what is spear phishing in cybersecurity” increased by a massive 1500%. Similarly, “phishing link checker” query increased by 600%.
Since remote and hybrid work setup uses collaboration software, cloud storage, file sharing, and similar other tools, threat actors use the vulnerabilities as entry points to exploit credentials and other personal data.
Cybersecurity experts suggest that remote workers be extra vigilant while operating online. From notifications to CAPTCHA, everything should be taken with a pinch of salt, as threat actors are becoming more sophisticated with every passing day. It is recommended to practice cyber hygiene regularly. Also, using MFA and double-checking every message, email, and notification can safeguard data from the prying eyes of phishing actors.
Topics

General Manager
General Manager at DuoCircle. Product strategy and commercial lead across the email security portfolio.
Secure your email infrastructure
Protect, authenticate, and deliver. Contact our team to find the right solution.