Zara Data Exposed, Medtronic Cyberattack Confirmed, Trellix Repository Breached – Cybersecurity News [May 04, 2026]

Quick Answer
Here’s your weekly roundup of the most important cybersecurity stories from the past week, covering major data breaches, critical vulnerabilities, new malware threats, and significant law enforcement developments shaping the global cybersecurity landscape. Hackers who gained access to the databases of Spanish fast-fashion retailer Zara stole data belonging to more than 197,000 customers, according to data breach notification service Have I Been Pwned.

Here’s your weekly roundup of the most important cybersecurity stories from the past week, covering major data breaches, critical vulnerabilities, new malware threats, and significant law enforcement developments shaping the global cybersecurity landscape.
Zara Data Breach Exposes Personal Data of Nearly 200,000 Customers
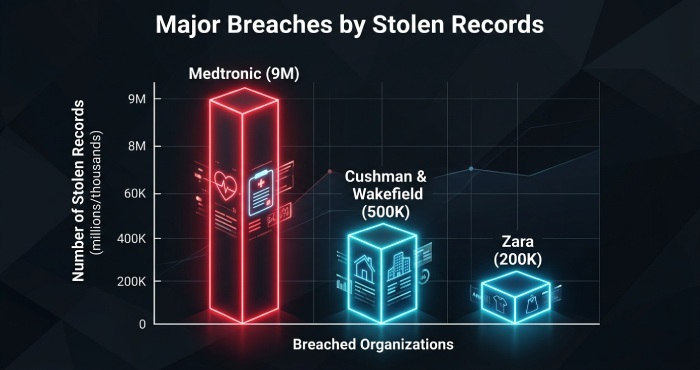
Hackers who gained access to the databases of Spanish fast-fashion retailer Zara stole data belonging to more than 197,000 customers, according to data breach notification service Have I Been Pwned.
Other breaches recently claimed by the same threat actors include Google, Cisco, PornHub, Match Group, Vimeo, Rockstar Games, ADT, the European Commission, edtech giant McGraw Hill, Medtronic, cruise line operator Carnival, convenience store chain 7-Eleven, and online training company Udemy. The Zara breach adds yet another major consumer brand to an already alarming list of compromised organisations.
Medtronic Confirms Cyberattack — ShinyHunters Claims 9 Million Patient Records Stolen
Medtronic confirmed that an unauthorized party accessed data in some of its corporate IT systems, becoming the latest major medical device manufacturer targeted by cybercriminals in 2026.
Prior to the official announcement, ShinyHunters claimed responsibility and stated it had exfiltrated terabytes of Medtronic data, including over 9 million records containing personally identifiable information. The group threatened to publish the stolen data unless a ransom was paid by April 21, 2026. Medtronic was subsequently removed from the leak site, suggesting the company either paid the ransom or entered into active negotiations.
Medtronic stated it found no impact on its products, patient safety, or manufacturing operations, and filed a Form 8-K with the SEC indicating the incident is not expected to have a material financial impact.
Trellix Source Code Repository Breached — RansomHouse Claims Responsibility
Cybersecurity vendor Trellix confirmed unauthorized access to a portion of its source code repository. On May 7, 2026, the ransomware group RansomHouse claimed responsibility for the hack, listing the company on its dark web data leak site.
Cybernews researchers who reviewed material published by the attackers suggest the breach may extend far deeper than source code alone, with screenshots appearing to show dashboards linked to enterprise infrastructure platforms commonly used to manage data storage, IT infrastructure, and virtual machines. This is particularly alarming given that Trellix protects more than 200 million endpoints and serves over 50,000 business and government customers worldwide.
Trellix stated it has found no evidence that its source code release or distribution process was affected or exploited, and has engaged forensic experts and notified law enforcement.
Ivanti EPMM Zero-Day Under Active Exploitation — CISA Orders Federal Agencies to Patch Immediately
A high-severity vulnerability in Ivanti Endpoint Manager Mobile (EPMM), tracked as CVE-2026-6973 with a CVSS score of 7.2, has been found under active exploitation. The flaw allows a remotely authenticated user with administrative access to achieve remote code execution.
CISA gave U.S. federal agencies four days to secure their networks against the vulnerability. The development prompted CISA to add the flaw to its Known Exploited Vulnerabilities catalog, requiring Federal Civilian Executive Branch agencies to apply fixes by May 10, 2026. Ivanti noted that organisations that had already followed earlier credential-rotation guidance significantly reduced their exposure to this new flaw.
TCLBANKER: Dangerous Brazilian Banking Trojan Targets 59 Financial Platforms via WhatsApp and Outlook
A new banking trojan known as TCLBANKER has been discovered by Elastic Security Labs, tracked under campaign REF3076. Attackers deliver it using a trojanized version of a legitimate, digitally signed Logitech installer, abusing a technique called DLL sideloading to load a malicious file without raising suspicion.
The malware targets users who visit any of 59 banking, fintech, and cryptocurrency platforms. To steal credentials, it displays fake full-screen overlays built with Windows Presentation Foundation that look exactly like real banking prompts or Windows Update screens, blocking keyboard shortcuts and screen-capture tools to prevent victims from detecting the fraud.
What makes TCLBANKER particularly dangerous is its self-propagating capability. One worm module hijacks the victim’s active WhatsApp Web session to silently message Brazilian contacts with a download link, while a second module abuses Microsoft Outlook to send convincing phishing emails from the victim’s own account.
Microsoft’s May Patch Tuesday: 165 Vulnerabilities Fixed Including an Exploited SharePoint Zero-Day
Microsoft’s latest Patch Tuesday updates addressed 165 vulnerabilities, including an actively exploited SharePoint Server zero-day tracked as CVE-2026-32201. The flaw has been described as a spoofing issue caused by improper input validation, potentially allowing an unauthorised attacker to access and alter sensitive information over a network.
The SharePoint zero-day is being actively exploited in the wild, and organisations are urged to prioritise patching and restrict internet exposure of SharePoint servers. The scale and breadth of this month’s Patch Tuesday release underscores the ongoing pressure on security teams to keep pace with the volume of critical fixes.
New Linux Zero-Day “Dirty Frag” Gives Local Attackers Root Privileges with a Single Command
A new Linux zero-day exploit named Dirty Frag allows local attackers to gain root privileges on most major Linux distributions with a single command.
Dirty Frag was discovered and reported by Hyunwoo Kim and is the second major local privilege escalation vulnerability disclosed in the Linux kernel within two weeks, following the earlier “Copy Fail” vulnerability (CVE-2026-31431). System administrators running Linux environments are strongly advised to monitor vendor advisories and apply kernel patches as soon as they become available.
NVIDIA GeForce NOW Alliance Partner Breached — User Data Exposed for Nearly Two Months
A data breach at GFN.AM, an authorised NVIDIA GeForce NOW Alliance partner in Armenia, was disclosed on May 5, 2026. The company revealed that unauthorised access to its backend database had occurred as far back as March 9, 2026 — approximately 54 days before discovery.
The breach exposed the user database, including first names, email addresses, nicknames, usernames, dates of birth, membership details, two-factor authentication status, and internal role information. NVIDIA confirmed the incident to BleepingComputer, stating that only users registered on or before March 9, 2026, are affected. Importantly, account passwords were reportedly not compromised.
Cushman & Wakefield Confirms Breach — ShinyHunters Leaks 500,000+ Salesforce Records
Cushman & Wakefield confirmed a vishing-related security breach after both ShinyHunters and Qilin listed the commercial real estate giant on their dark web leak sites, with ShinyHunters claiming it stole more than 500,000 Salesforce records.
The ransomware attack exposed a significant volume of personally identifiable information and internal corporate data. ShinyHunters published the data trove after claiming that ransom negotiations with the company had broken down, adding Cushman & Wakefield to a growing list of high-profile victims the group has targeted in 2026.
Virginia Man Convicted for Plotting to Destroy Dozens of Government Databases After Being Fired
A 34-year-old Virginia man was found guilty of conspiring to destroy dozens of government databases after being fired from his job as a federal contractor. The case highlights the persistent and serious risk posed by disgruntled insiders with privileged access to government systems. Security experts continue to urge organisations to implement strict access revocation procedures the moment an employee’s relationship with the organisation changes, with no delay in removing credentials or system permissions.
Ukrainian Police Dismantle Roblox Account Hijacking Ring That Stole 610,000 Accounts
Ukrainian police dismantled a hacking ring responsible for hijacking and selling over 610,000 Roblox accounts, generating roughly $225,000 in illicit profits. The operation demonstrates the growing monetisation of gaming-related cybercrime, where stolen accounts — even those associated with entertainment platforms — are packaged and sold through underground marketplaces.
The takedown serves as a reminder that young users are prime targets for credential theft, and that enabling two-factor authentication on gaming accounts is no longer optional.
Fake Call History Apps Racked Up 7.3 Million Downloads on Google Play While Defrauding Users
Cybersecurity researchers discovered fraudulent apps on the official Google Play Store that falsely claimed to offer access to call histories for any phone number, only to trick users into paid subscriptions that delivered completely fake data. The 28 apps collectively racked up more than 7.3 million downloads, with one app alone accounting for a significant share.
The incident raises fresh concerns about the effectiveness of app store vetting processes. Users are reminded to scrutinise permissions, check developer credibility, and read reviews carefully before downloading any app — even those hosted on official storefronts.
China-Linked APT Group Conducting Espionage Campaigns Across South America and Europe
A sophisticated China-linked advanced persistent threat group has been targeting government entities in South America since at least late 2024 and in Southeastern Europe since 2025, according to security researchers. The campaign reflects a continued pattern of state-sponsored actors expanding their operational scope beyond traditional targets, using government institutions as espionage stepping stones.
Researchers urge government bodies in the affected regions to audit third-party access, review network segmentation, and implement stronger monitoring of lateral movement within their environments.
Topics

General Manager
General Manager at DuoCircle. Product strategy and commercial lead across the email security portfolio.
Secure your email infrastructure
Protect, authenticate, and deliver. Contact our team to find the right solution.