Your Vendors Are Your Weakest Link: How Third-Party Email Compromise Doubled in One Year and What SMBs Can Do About It

Quick Answer
Your organization can have the most sophisticated cybersecurity stack on the market, and it might not matter. Because the breach is increasingly starting not inside your network, but inside your vendor’s. The Verizon 2025 Data Breach Investigations Report (DBIR), which analyzed over 22,000 security incidents and 12,195 confirmed breaches across 139 countries, documented one of the most dramatic shifts in.

A data-driven analysis with 20+ primary-source statistics from Verizon, IBM, SecurityScorecard, the FBI, the World Economic Forum, and others.
Introduction: The Breach That Starts Outside Your Walls
Your organization can have the most sophisticated cybersecurity stack on the market, and it might not matter. Because the breach is increasingly starting not inside your network, but inside your vendor’s.
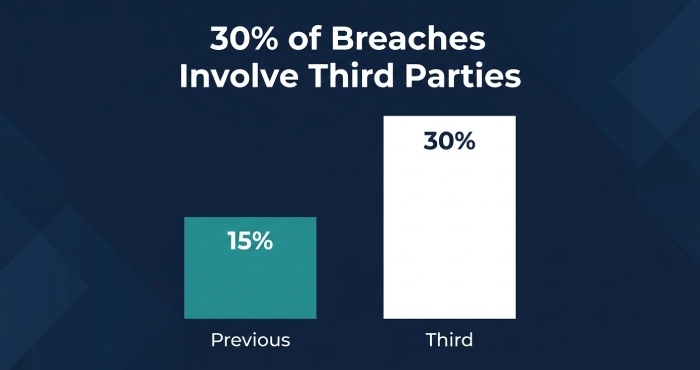
The Verizon 2025 Data Breach Investigations Report (DBIR), which analyzed over 22,000 security incidents and 12,195 confirmed breaches across 139 countries, documented one of the most dramatic shifts in recent breach history: 30 percent of all breaches now involve third-party partners or vendors. That is double the 15 percent reported just one year earlier. In a single year, the supply chain went from a secondary risk factor to a primary attack vector.
The SecurityScorecard 2025 Global Third-Party Breach Report, which analyzed 1,000 breaches across industries and regions, confirmed the trend from a different angle: 35.5 percent of all breaches in 2024 originated through third-party infrastructure, a 6.5 percentage point increase from 2023.
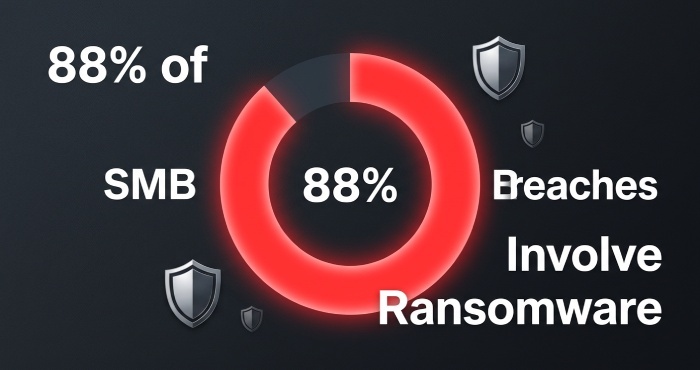
For small and medium-sized businesses, the picture is even more alarming. The Verizon DBIR found that ransomware appeared in 88 percent of SMB breaches, and SMBs are being targeted nearly four times more frequently than large organizations. When you combine the supply chain explosion with the disproportionate targeting of smaller organizations, the conclusion is stark: your vendors are not just a theoretical risk. They are the most likely path an attacker will use to reach you.
This article explains what is driving the third-party breach epidemic, how it works through email as the primary delivery mechanism, and what SMBs can do to protect themselves starting today.
1. The Data: Third-Party Breaches Have Doubled, and the Trend Is Accelerating
The Verizon DBIR: From 15% to 30% in One Year
The doubling of third-party involvement from 15 percent to 30 percent in the Verizon 2025 DBIR was not driven by a single type of incident. These breaches included credential exposures from partner environments, misconfigured SaaS platforms, software supply chain vulnerabilities, and compromised vendor email accounts. Among breaches with third-party involvement, 81 percent involved system intrusion, and several high-profile incidents involved credential reuse in a third-party environment. The median time to remediate leaked secrets discovered in a GitHub repository was 94 days, giving attackers nearly three months of undetected access.
Craig Robinson, Research Vice President for Security Services at IDC, put it bluntly in the DBIR commentary: organizations without proper IT and cybersecurity maturity, often the SMB-sized organizations, are paying the price for their size.
SecurityScorecard: 35.5% of Breaches Originate via Third Parties
The SecurityScorecard 2025 Global Third-Party Breach Report provides additional granularity. Analyzing 1,000 breaches using open-source intelligence, threat intelligence, and underground forum monitoring, SecurityScorecard found that 35.5 percent of breaches in 2024 originated through third-party infrastructure. Retail (52.4 percent), technology (46.75 percent), and energy (46.7 percent) experienced the highest third-party breach rates. Two exploited file transfer software vulnerabilities alone accounted for 63.5 percent of all third-party vulnerability-driven breaches, demonstrating how a single vendor’s flaw can cascade across thousands of downstream organizations.
SecurityScorecard also found that 98 percent of organizations globally have relationships with at least one breached third party. For every direct vendor in a supply chain, organizations typically have indirect relationships with 60 to 90 times that number of fourth-party relationships. Third-party vendors are five times more likely to exhibit poor security than the primary organization they serve.
IBM: Supply Chain Compromise Is Now the Second-Costliest Attack Vector
The IBM Cost of a Data Breach Report 2025 found that third-party vendor and supply chain compromise surged to become the second most prevalent attack vector at 15 percent of all breaches, and the second costliest at $4.91 million per breach, just behind malicious insider threats at $4.92 million. These breaches also took the longest to resolve: an average of 267 days from identification to containment, 26 days longer than the overall average.
30% of all breaches now involve third-party partners or vendors, double the 15% reported just one year earlier. Among SMBs, ransomware appeared in 88% of breaches., Verizon 2025 DBIR
2. How Third-Party Compromise Works Through Email
Email is the primary vehicle through which third-party compromises reach your organization. Understanding the mechanics is essential to defending against them.
The Compromised Vendor Account
The most common scenario is deceptively simple. An attacker compromises a vendor’s email account through credential theft, phishing, or infostealer malware. They then use that legitimate, trusted account to send emails to the vendor’s customers and partners. Because the email comes from a known, trusted sender with a valid email address, it sails through reputation-based email filters and often bypasses human suspicion as well.
The KnowBe4 Phishing Threat Trends Report (March 2025) confirms this: 57.9 percent of phishing emails were sent from compromised accounts. When your accounting department receives an invoice from a vendor they work with every month, sent from the vendor’s actual email address, with correct formatting and legitimate-looking details, no amount of typo-spotting training will help. The email is real. The sender is real. Only the intent is malicious.
Business Email Compromise: The $2.77 Billion Problem
The FBI’s 2024 IC3 Annual Report recorded 21,442 BEC complaints in 2024, totaling $2.77 billion in losses. BEC losses have totaled nearly $8.5 billion over the past three years. These are not sophisticated technical exploits. They are email-based social engineering attacks where an attacker impersonates a trusted party, usually a vendor, executive, or partner, to trick an employee into wiring money, changing payment details, or sharing credentials.
The APWG Phishing Activity Trends Report for Q1 2024 found that the average wire transfer amount requested in BEC attacks reached $84,059, up nearly 50 percent from the prior quarter. Gift card scams comprised 37.9 percent of BEC attacks, with Google being the most popular free webmail provider used by BEC scammers at 68 percent of webmail-based attacks.
The Credential Reuse Chain
The Verizon DBIR 2025 found that stolen credentials remain the most common initial access vector, used in 22 percent of all breaches. In basic web application attacks, stolen credentials were involved in 88 percent of cases. When a vendor’s credentials are compromised, either through phishing or infostealer malware, those credentials often provide access not just to the vendor’s systems but to shared platforms, cloud environments, and email systems that connect to your organization.
The Snowflake incident of 2024 illustrates this perfectly. Attackers identified that certain Snowflake customers were not enforcing multi-factor authentication, developed tooling to discover vulnerable accounts, and exfiltrated data from approximately 165 downstream organizations, all through a single vendor’s platform.
3. Why SMBs Are Disproportionately Vulnerable
The Verizon DBIR data reveals a stark asymmetry: ransomware appeared in 88 percent of SMB breaches compared to 39 percent of enterprise breaches. SMBs are targeted nearly four times more frequently than large organizations. The median ransom payment was $115,000, a sum that can be existential for a small business.
There are several structural reasons why SMBs face disproportionate third-party email risk:
- Smaller security teams with less vendor oversight. Most SMBs lack dedicated third-party risk management programs. Vendor security is assessed, if at all, during onboarding and rarely revisited.
- Greater reliance on email for business transactions. SMBs are more likely to process invoices, approve payments, and share sensitive data via email without the enterprise-grade workflow systems that enforce segregation of duties.
- Less mature email authentication. Many SMBs have not fully implemented SPF, DKIM, and DMARC, leaving their domains vulnerable to spoofing and making it harder to detect when vendors’ domains are being spoofed in attacks against them.
- Downstream position in supply chains. SMBs often serve as vendors to larger enterprises, making them attractive targets for attackers seeking to compromise the larger organization through the weakest link.
The Accenture State of Cybersecurity Resilience 2025 found that only 34 percent of organizations globally have a mature cyber strategy. For SMBs, that figure is likely significantly lower. The Cisco 2025 Cybersecurity Readiness Index found that only 4 to 6 percent of organizations worldwide qualify as ‘Mature’ in cybersecurity readiness, with 70 percent remaining in the bottom two categories.
4. Building a Third-Party Email Defense: Practical Steps for SMBs
You cannot control your vendors’ security. But you can control how much damage a vendor compromise can do to your organization. Here is a layered approach designed specifically for SMBs with limited security resources.
Layer 1: Enforce Email Authentication on Your Own Domain
If your domain does not have DMARC at enforcement level (p=quarantine or p=reject), anyone can send emails that appear to come from your organization. This makes it trivially easy for attackers to impersonate you in BEC attacks against your customers and partners. Implementing SPF, DKIM, and DMARC is the single most important step an SMB can take to prevent domain spoofing.
For organizations using multiple email services, SaaS platforms, and third-party senders, managing SPF records is particularly challenging because of the 10 DNS lookup limit. Exceeding this limit silently breaks email authentication, leaving your domain unprotected. SPF flattening tools solve this by converting nested lookups into direct IP addresses, keeping your record functional regardless of complexity.
The CISA phishing guidance specifically recommends DMARC implementation as a critical cybersecurity performance goal for all organizations.
Layer 2: Deploy Real-Time Link Scanning at the Email Gateway
When a phishing email arrives from a compromised vendor account, the sender address is legitimate. Your reputation filter will not block it. Your employees will not suspect it. The only technical defense that can intervene is real-time analysis of the content, links, and attachments within the email itself.
Cloud-based email security solutions that rewrite URLs and check them against threat intelligence databases at the moment of user click, not just at delivery, provide protection that static filters cannot. The KnowBe4 Phishing Threat Trends Report documented a 36.8 percent increase in phishing hyperlinks bypassing traditional SEG detection, reinforcing the need for click-time scanning rather than delivery-time-only inspection.
Layer 3: Require Multi-Channel Verification for Financial Transactions
The single most effective defense against BEC is also the simplest: never complete a financial transaction based solely on an email instruction. The FBI IC3 data shows that BEC costs organizations $2.77 billion annually, and these losses are almost entirely preventable. Establish a policy that all wire transfers, invoice payment changes, and credential resets must be confirmed through a separate communication channel, such as a phone call to a known number (not a number provided in the email) or an in-person verification.
Layer 4: Demand Email Authentication From Your Vendors
If your vendors have not implemented DMARC on their domains, their accounts are easier to spoof, and compromised vendor emails are harder to detect. Include email authentication requirements (SPF, DKIM, DMARC at enforcement) in your vendor security questionnaires and contractual requirements. Use DMARC reporting tools to monitor whether emails purporting to come from your vendors’ domains are actually authenticated. If they are not, that is a signal that either the vendor has poor email hygiene or someone is spoofing their domain.
Layer 5: Monitor for Compromised Credentials
The Verizon DBIR found that 54 percent of ransomware victims had prior credentials exposed in infostealer logs. Credential monitoring services can alert you when employee or vendor credentials appear in dark web dumps or infostealer databases, giving you the opportunity to force password resets and enable MFA before attackers exploit the stolen credentials.
The Microsoft Digital Defense Report 2025 confirms that phishing-resistant MFA blocks over 99 percent of unauthorized access attempts. If your vendors are not enforcing MFA on the accounts they use to interact with your systems, that is a critical gap in your supply chain security.
5. A Quarterly Action Checklist for SMBs
Here are six concrete steps an SMB can take this quarter to materially reduce third-party email risk:
- 1. Implement DMARC at enforcement on all your domains. If you have not done this yet, this is your highest-priority action item. Use SPF flattening to manage complex records without exceeding the 10-lookup limit.
- 2. Deploy a cloud email security layer with real-time link scanning. Do not rely solely on Microsoft 365 or Google Workspace native security. Add a layered solution that rewrites URLs and checks them at click time.
- 3. Establish a written policy for out-of-band verification of all financial transactions. Train every employee who handles payments, invoicing, or credential management on this policy. Test compliance quarterly.
- 4. Audit your vendor email authentication. Use DMARC reporting to check whether your critical vendors have DMARC at enforcement. If they do not, escalate to your procurement or account management team.
- 5. Review and restrict vendor access. Apply the principle of least privilege to every vendor connection. Audit which vendors have access to your systems, what level of access they hold, and whether they enforce MFA.
- 6. Set up a backup MX service. If your email server goes down during an incident, having a backup MX ensures you do not lose critical communications during recovery. Downtime during a supply chain incident can compound losses significantly.
Conclusion: You Cannot Outsource Trust
The doubling of third-party breaches documented in the 2025 Verizon DBIR is not a temporary spike. It is the natural consequence of an increasingly interconnected business environment where every organization’s attack surface extends far beyond its own network boundary. SecurityScorecard’s finding that 98 percent of organizations have relationships with at least one breached third party means that exposure is essentially universal.
For SMBs, the stakes are existential. With ransomware present in 88 percent of SMB breaches, a median ransom of $115,000, and average supply chain breach costs reaching $4.91 million, a single vendor compromise can threaten the viability of the business.
But the data also shows that effective defenses exist. Email authentication through SPF, DKIM, and DMARC prevents domain spoofing. Real-time link scanning catches malicious content from compromised trusted accounts. Multi-channel verification stops BEC before money moves. And MFA blocks 99 percent of unauthorized access attempts.
You cannot control your vendors’ security posture. But you can control the blast radius when their defenses fail. The organizations that survive the supply chain era will be the ones that treated vendor trust as something to verify, not assume.
References & Sources
All statistics cited in this article are drawn from primary-source institutional reports. Full URLs provided.
[1] Verizon, 2025 Data Breach Investigations Report (DBIR) [PDF]
https://www.verizon.com/business/resources/reports/dbir/
[2] Verizon, 2025 DBIR Press Release [Web]
https://www.verizon.com/about/news/2025-data-breach-investigations-report
[3] SecurityScorecard, 2025 Global Third-Party Breach Report [PDF]
https://securityscorecard.com/wp-content/uploads/2025/03/SSC-Third-Party-Breach-Report_031225_03.pdf
[4] SecurityScorecard, Third-Party Breach Report Press Release (March 2025) [Web]
[5] IBM / Ponemon Institute, Cost of a Data Breach Report 2025 [PDF]
https://www.bakerdonelson.com/webfiles/Publications/20250822_Cost-of-a-Data-Breach-Report-2025.pdf
[6] FBI Internet Crime Complaint Center (IC3), 2024 Annual Report [PDF]
https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf
[7] KnowBe4, Phishing Threat Trends Report Vol. 5 (March 2025) [PDF]
https://www.knowbe4.com/hubfs/Phishing-Threat-Trends-2025_Report.pdf
[8] APWG, Phishing Activity Trends Report Q1 2024 [PDF]
https://docs.apwg.org/reports/apwg_trends_report_q1_2024.pdf
[9] World Economic Forum, Global Cybersecurity Outlook 2026 [PDF]
https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2026.pdf
[10] Cisco, 2025 Cybersecurity Readiness Index [PDF]
[11] Accenture, State of Cybersecurity Resilience 2025 [PDF]
[12] Microsoft, Digital Defense Report 2025 [PDF]
[13] CISA, Phishing Infographic, Cybersecurity Performance Goals [PDF]
https://www.cisa.gov/sites/default/files/2023-02/phishing-infographic-508c.pdf
[14] SecurityScorecard, Third-Party Breach Report 2024 (covering 2023) [Web]
https://securityscorecard.com/company/press/global-third-party-risk-report/
[15] SecurityScorecard, Fintech Vendor Breach Report (May 2025) [Web]
Topics

General Manager
General Manager at DuoCircle. Product strategy and commercial lead across the email security portfolio.
Secure your email infrastructure
Protect, authenticate, and deliver. Contact our team to find the right solution.