How The Best Anti-Phishing Software Prevents Email-Based Attacks

Quick Answer
Effective anti-phishing software combines layered detection across the message lifecycle. Detection engines blend signatures, heuristics, NLP for tone and urgency cues, and brand impersonation models that match logos and display names. Relationship graphs map normal sender-recipient patterns so impersonation attempts score higher. URL rewriting routes link clicks through real-time scanners that block malicious destinations after delivery, and remote browser isolation contains risky sessions. Attachment defenses use sandbox detonation, content disarm and reconstruction (CDR), and macro/script inspection to neutralize weaponized files. Email authentication (SPF, DKIM, DMARC, BIMI, ARC) sets the trust baseline; the platform enforces alignment and flags header anomalies. For BEC, behavioral AI baselines approval patterns and surfaces anomalies in payment requests, supplier domain changes, and thread hijacks. Deploy a secure email gateway plus an API-based post-delivery tool for layered coverage, integrate with SIEM/SOAR for response, and pair with phishing simulation and user training.

Email-centric threats continue to be a prevalent and expensive cybersecurity challenge for both companies and individuals. With phishing methods evolving in complexity, businesses are turning to advanced security solutions to spot and prevent harmful emails from landing in their mailboxes.
The most effective anti-phishing software employs smart filtering, threat identification, and continuous monitoring to uncover dubious communications and avert data breaches, account hijacking, and financial scams.
Why phishing works and what “best” anti-phishing really means
Phishing is effective because cybercriminals leverage people’s trust, sense of urgency, and curiosity to deceive them into providing personal data. Rather than focusing solely on technical flaws, phishing schemes prey on human tendencies through persuasive emails, messages, and fraudulent websites. The most effective strategy against phishing blends user education, robust security measures, and active surveillance to identify and prevent threats before harm can be done.
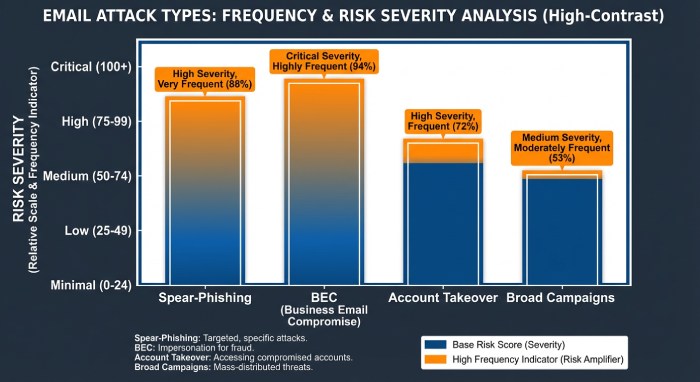
Common email attack types and why users still click
Even the most mature organizations face relentless phishing attacks because adversaries exploit trust and timing. Typical phishing email types include broad campaigns delivering malicious emails at scale, targeted spear-phishing designed around executives or finance teams, and business-email-compromise that hijacks real conversations to request urgent wire transfers. Attackers also stage account takeover to send convincing messages from legitimate mailboxes across Google Workspace and Microsoft 365, and they seed malicious URLs and weaponized attachments that evade basic spam filtering.
The best anti-phishing software approaches these email-based threats as a continuum rather than a single event. A top-tier prevention platform must detect phishing in the mail flow and continue to protect users at time of click. It should combine email protection controls for spoofing prevention, domain lookalikes, and brand imposters with post-delivery inbox protection that flags late-emerging signals. Leaders like Proofpoint, Mimecast, IRONSCALES, and Cofense have matured their cybersecurity tool stacks to blend threat intelligence, machine learning, and pattern recognition into multi-layer protection capable of stopping zero-day attacks and reducing risk of payment fraud and financial fraud.
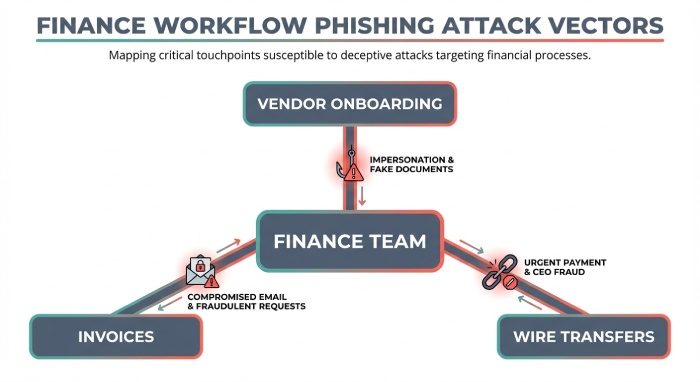
Human factors: approvals, vendors, and finance workflows
Phishing works because it mirrors business context. Finance teams manage vendor onboarding, vendor management, and sensitive approval patterns that adversaries study to commit payment fraud. They weaponize purchase orders, invoices, and integration with ERP processes to reroute funds, pressuring staff during quarter-end crunch. That is why organizations from Deloitte to Colgate-Palmolive, CNA, Blue California, United Rentals, Chipotle, Baxter, monday.com, and BeOne emphasize security awareness, user training, and ongoing employee training alongside technology.
Best-in-class anti-phishing software reinforces people and processes with behavioral AI, anomaly detection, and risk scoring that highlight unusual sender relationships, unexpected bank detail changes, and spoofed domains. Pairing these capabilities with payment workflow security from providers like Trustmi strengthens fraud detection across financial systems security without slowing operations.
Capabilities that separate leaders
Market leaders deliver a prevention platform that:
- Applies real-time monitoring and continuous monitoring from delivery through user engagement.
- Uses machine learning, artificial intelligence, and pattern recognition to detect phishing tactics that signatures miss.
- Leverages rich threat intelligence, brand and domain telemetry, and relationship graphs for impersonation prevention.
- Enables customizable policies aligned to security policies, with dashboard reporting, alerting and response, and incident remediation.
- Supports SIEM integration and broader system integrations with SOAR, enabling security automation and SOC automation.
- Covers cloud apps via API for post-delivery control, plus phishing simulation to uplift resilience.
To round out strategy, align technology with governance and the right email security program so defenders can operate a coherent cybersecurity tool stack.
Layered detection engines and signals
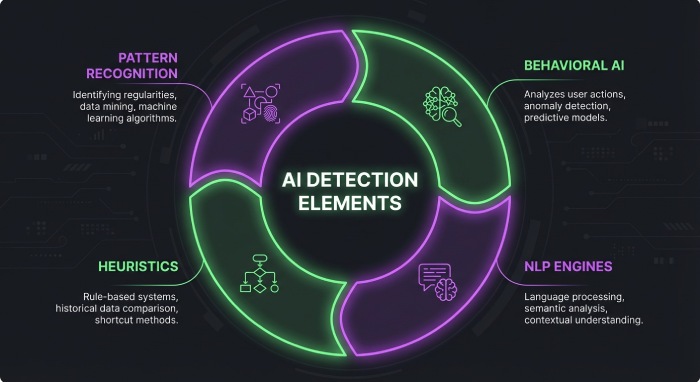
From signatures to heuristics and NLP
Core engines still start with signatures and heuristics for rapid threat detection and spam protection. However, modern anti-phishing software augments these with NLP models that analyze message tone, urgency cues, and payment language patterns indicative of financial fraud. Pattern recognition across message bodies and headers, plus behavioral AI trained on historical communications, helps detect phishing attempts without relying solely on known indicators.
Brand and identity models
- Brand impersonation models match logos, display names, and look-and-feel elements; Fortra Brand Protection can enrich these signals by tracking newly registered domains and fake login kits.
- Header anomalies, alignment checks, and sending infrastructure heuristics reveal staged infrastructure used for malicious emails.
Relationship and graph intelligence
- Relationship graphs map who normally communicates with whom, which empowers impersonation prevention by scoring deviations.
- Risk scoring and anomaly detection consider factors like time-of-day anomalies, first-contact attempts, and unusual approval patterns to elevate potential payment fraud.
Vendors such as Proofpoint, Mimecast, IRONSCALES, and Cofense fuse these detectors into a single prevention platform that can detect phishing reliably before a user clicks.
Link and website protection at time of click
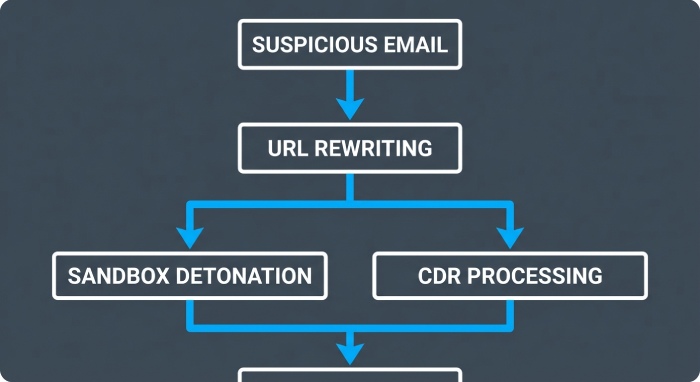
URL rewriting and intelligent decisioning
Attackers often weaponize links after delivery. URL rewriting allows anti-phishing software to route clicks through a secure decision engine that performs URL scanning in real time. If a destination morphs into malicious URLs, the system can block access or isolate the session, preserving email protection beyond initial delivery.
Domain intelligence and page analysis
- Analyze domain age, registrar reputation, typosquats and homographs, and other domain lookalikes.
- Page analysis inspects forms, JavaScript, visual similarity to known brands, and credential harvesting elements across cloud apps.
Browser isolation and post-click controls
Remote browser isolation confines risky sessions, safeguarding users in Google Workspace and Microsoft 365 environments. Combined with continuous monitoring and alerting and response, these controls reduce exposure to account takeover and spear-phishing sites without hampering productivity.
Attachment and payload defenses
Sandbox and static/dynamic inspection
Modern malware detection relies on a sandbox environment with sandbox detonation of suspicious files. Static analysis flags obfuscation, packers, and abnormal metadata, while dynamic analysis executes samples to observe network calls, process injection, and exfiltration.
CDR and macro/script inspection
- Content disarm and reconstruction (CDR) removes active content and rebuilds safe files.
- Macro/script inspection and attachment scanning neutralize weaponized Office docs, PDFs, archives, and scripts used in zero-day attacks.
Advanced techniques and resilience
Multi-layer protection extends to archive recursion, heuristic unpacking, and policy-driven quarantine flows. Customizable policies tied to security policies let teams tune sensitivity for finance and executive users who face elevated payment fraud risk.
Email authentication and trust enforcement
Protocols that set the trust baseline
SPF, DKIM, and DMARC establish sender authenticity and alignment. BIMI provides brand indicators that reinforce visual trust, while ARC preserves authentication results through forwarding. TLS and MTA-STS improve transport-layer security, making downgrade and interception attempts harder.
How software enforces alignment and detects anomalies
Anti-phishing software enforces DMARC alignment and monitors deviations in real time. Header anomalies, unexpected sources, failed SPF/DKIM, or misaligned subdomains, raise scores for spoofing prevention and impersonation prevention. Domain lookalikes detected via threat intelligence further reduce risk that malicious emails reach users. Enforcement can be staged with quarantine policies, then tightened to reject as confidence improves.
Operationalizing trust with integrations
- SIEM integration correlates email events with network and endpoint data, boosting threat detection and incident remediation.
- SOAR playbooks automate takedowns, system integrations, and user notifications, enabling efficient security automation and SOC automation.
- Dashboard reporting consolidates risk scoring, phishing attacks trends, and fraud detection outcomes across business units.
Bringing it together: technology, people, and process
From mail flow to finance outcomes
The objective is not simply to detect phishing but to stop business losses. With strong impersonation prevention, pattern recognition tuned to finance lures, and a prevention platform that spans delivery to click, organizations cut exposure to payment fraud and financial fraud. Integrations that watch integration with ERP workflows tie email security signals to vendor onboarding, vendor management, and payment workflow security, preventing attackers from abusing approval patterns.
Operational excellence and readiness
- Spam filtering plus inbox protection curb noise so analysts focus on high-fidelity signals.
- Phishing simulation, user training, and security awareness harden human defenses where social engineering thrives.
- Customizable policies adapt to departments, while system integrations, SIEM, and SOAR drive rapid alerting and response.
When combined, anti-phishing software, a modern cybersecurity tool stack, and disciplined processes create durable email protection against evolving email-based threats. With layered threat intelligence, machine learning, and pattern recognition, organizations can confidently prevent, detect, and remediate malicious emails long before they become costly payment fraud or broader financial fraud events.
Stopping BEC and Social Engineering
Intent Detection and Context Signals
Payment and Urgency Cues
Modern anti-phishing software uses machine learning and pattern recognition to infer intent from language and workflow context. Signals such as sudden payment requests, atypical bank detail changes, or high-urgency phrasing map to payment fraud and financial fraud risk. A strong prevention platform correlates email-based threats with finance system data to detect phishing attempts tied to invoice changes and wire transfers.
Modeling approval patterns
Behavioral AI can baseline approval patterns who usually approve which suppliers, amounts, and timelines and surface anomalies linked to business-email-compromise. This pairing of a cybersecurity tool with finance telemetry elevates detection accuracy without overwhelming teams with false positives.
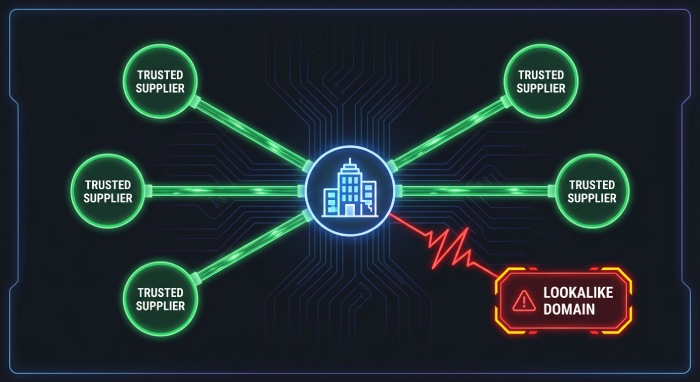
Supplier Impersonation and Domain Lookalikes
Impersonation prevention hinges on discovering domain lookalikes, display-name abuse, and newly registered senders. Threat intelligence enriched by external brand monitoring (e.g., Fortra Brand Protection) flags spoofing infrastructure before it is weaponized. Anti-phishing software that blends URL scanning for malicious URLs with relationship graphs will detect phishing signals when a “supplier” deviates from historic messaging patterns.
Supplier graph enrichment
Link supplier records from vendor management systems to known-good sender histories; add risk scoring if bank-account metadata or remittance addresses shift between messages.
Thread Hijacking and Conversation Analysis
Thread hijacking is especially dangerous because replies borrow trust from prior correspondence. Robust email protection inspects quoted content, time gaps, and MIME anomalies. Pattern recognition identifies inserts like “new payment instructions” that deviate from earlier email bodies, while sandbox environment analysis and attachment scanning prevent malware-laced replies.
Account Takeover Signals
Account takeover detection combines impossible travel, OAuth grant spikes to cloud apps, and post-login email rule creation. Real-time monitoring of forwarding rules, hidden inbox rules, and anomalous authentication contributes to early containment, reducing dwell time and halting internal phishing attacks before they cascade into payment fraud.
Behavioral signals to flag risk
- Unexpected sharing to external domains
- Sudden export of contact lists
- Creation of auto-delete rules for finance keywords
Impersonation Prevention Controls
Spoofing Prevention and Authentication
Strong spoofing prevention enforces DMARC, DKIM, and SPF with policy-based reject, complemented by BIMI for visual trust. Anti-phishing software should apply customizable policies to downgrade or quarantine messages that fail alignment, particularly when approval patterns or supplier context make a request sensitive.
Executive and Supplier Relationship Mapping
Graph models that track executive-to-vendor threads bolster impersonation prevention against spear-phishing aimed at the CFO, AP manager, or procurement leads. Risk scoring rises when an unfamiliar domain requests urgent payment workflow changes.
AI-driven pattern recognition
Combining machine learning, behavioral AI, and artificial intelligence enhances threat detection of low-volume, high-impact phishing email types. These methods help detect phishing indicators that rules miss, enabling a multi-layer protection approach.
User-Facing Safeguards and Education
Contextual Warning Banners
Context-aware banners translate complex threat intelligence into plain-language prompts. Indicators like “new sender,” “reply-to mismatch,” “bank account change,” or “external thread hijack” guide users to pause.
Consistent experience across devices
Deliver uniform banners in desktop clients, mobile apps, and webmail to ensure inbox protection wherever users work. For readers researching best-practice guidance on controls, see email security.
Just-in-Time Coaching
Inline prompts at click time provide coaching when users try to open malicious URLs or reply to suspicious requests. URL scanning and attachment scanning workflows can route items to a sandbox environment
Sandbox detonation and unknown threats
Sandbox detonation reduces risk from zero-day attacks by executing payloads safely. Coupled with multi-engine malware detection, this closes gaps left by signature-only tools.
Integrated Phishing Simulations
Phishing simulation programs embedded into the same prevention platform reinforce security awareness and user training. Solutions from providers such as Cofense and IRONSCALES pair simulations with adaptive employee training, aligning difficulty to each user’s behavior and improving fraud detection rates over time.
One-Click Reporting and Abuse Mailbox
A report button streamlines alerting and response while furnishing labeled samples that enrich threat intelligence. Abuse mailbox triage can be automated to cluster duplicates, prioritize BEC, and feed SOC automation for rapid incident remediation.
Deployment Models and Integrations
Secure Email Gateways vs API-based Post-Delivery
SEG architectures from vendors like Proofpoint and Mimecast filter at the perimeter with spam filtering and spam protection, while API-based tools perform post-delivery analysis inside Microsoft 365 and Google Workspace. Many enterprises deploy both for multi-layer protection: the SEG screens bulk malicious emails; API engines apply anomaly detection to detect phishing inside user mailboxes.
Cloud, mobile, and endpoint coverage
API approaches align with cloud apps and natively support mobile clients, while endpoint plug-ins extend one-click reporting and banners across devices. Ensure continuous monitoring regardless of client type.
System Integrations
SIEM/SOAR and workflow orchestration
Look for deep SIEM integration and SOAR playbooks that automate quarantine, retroactive purge, and case enrichment. Standardized system integrations with ITSM, chat tools, and identity providers streamline security automation and approval flows.
Finance stack and ERP alignment
Integration with ERP platforms enables payment workflow security, validating vendor records, bank accounts, and invoice changes. Trustmi can harden payment flows and vendor onboarding checks, while email-layer signals gate risky requests. This improves financial systems security and reduces business-email-compromise exposure.
Example integration patterns
- Connect monday.com or BeOne as process hubs for vendor management exceptions.
- Use Deloitte-style control assessments to map security policies to finance risks.
- Trigger secondary approval when risk scoring exceeds thresholds.
Multi-Layer Protection Architecture
Filter, inspect, and correlate
Combine spam filtering, URL scanning, and malware detection with relationship analytics. Correlating malicious URLs, domain lookalikes, and workflow anomalies improves threat detection across email-based threats.
AI engines at the core
Machine learning and behavioral AI augment pattern recognition to detect phishing with higher precision. These AI layers transform anti-phishing software into an adaptive cybersecurity tool that learns from each attack.
External intelligence and brand safeguards
Blend internal telemetry with external threat intelligence feeds and Fortra Brand Protection for impersonation prevention at scale.
Automated Response and SOC Workflows
Auto-Quarantine and Retroactive Purge
When high-confidence indicators surface, auto-quarantine reduces blast radius, and retroactive purge removes malicious emails from all affected inboxes. Real-time monitoring plus continuous monitoring ensures newly discovered indicators trigger immediate cleanup.
Abuse mailbox and prioritization
Abuse mailbox triage clusters similar reports, suppresses noise, and routes the riskiest BEC to analysts, speeding alerting and response.
Playbooks and Threat Intel Sharing
Codified SIEM/SOAR playbooks automate incident remediation, while dashboard reporting and risk scoring provide leadership transparency. Sharing indicators with peer groups and ISACs improves community defense and feeds prevention platforms to stop related phishing attacks.
Collaboration with Finance and IT
SOC runbooks should notify Finance on suspected payment fraud, pause pending ACH changes, and verify via out-of-band channels. Mapping approval patterns and integration with ERP ensures end-to-end controls from email protection to payment release.
Evaluating Vendors and Measuring Success
Test Design and KPIs
Design A/B pilots that pit candidate prevention platforms against seeded spear-phishing, BEC, and malware-lure scenarios. Track detection versus false positives, dwell time, coverage of malicious URLs, and attachment scanning efficacy. Include phishing email types that mimic supplier impersonation, thread hijacking, and account takeover.
Privacy, compliance, and policy control
Assess data handling in cloud apps, retention, and encryption. Ensure customizable policies align with security policies, and verify safeguards against account takeover, domain lookalikes, and spoofing prevention.
Support, ROI/TCO, and Pilot Tips
Evaluate vendor customer success, threat research, and playbook libraries from providers such as Proofpoint, Mimecast, IRONSCALES, Cofense, and Fortra Brand Protection. Confirm SOC automation maturity, SIEM/SOAR readiness, and clear SLAs.
Running a credible pilot
- Start with a small cohort, baseline KPIs, and expand progressively.
- Use red team campaigns and controlled payment-change requests.
- Compare dashboard reporting across tools; require export for SIEM integration.
Business value and references
Model ROI from averted payment fraud, reduced incident hours, and minimized reputational risk from phishing attacks. Seek peer references from enterprises like CNA, Baxter, United Rentals, Blue California, Chipotle, and Colgate-Palmolive to gauge operational fit and long-term TCO. Include vendor onboarding checks and Trustmi-style payment controls to close gaps beyond the inbox.
FAQs
How does AI improve BEC detection without increasing false positives?
Combining machine learning with behavioral AI and pattern recognition captures subtle intent cues while correlating them with relationship graphs and approval patterns. This multi-layer approach improves precision and reduces alert fatigue.
Do I need both a secure email gateway and an API-based tool?
Many organizations use both: a SEG for perimeter filtering and an API-based prevention platform for post-delivery anomaly detection and user-facing safeguards. The layered model enhances email protection across diverse clients and cloud apps.
What signals indicate account takeover in email?
Look for impossible travel, sudden forwarding/auto-delete rules, OAuth consent changes, and mass access to contact lists. Pairing these with real-time monitoring and SIEM/SOAR playbooks enables rapid incident remediation.
How should finance and security collaborate on payment fraud?
Integrate email-layer risk scoring with ERP approval patterns and vendor management workflows. Pause high-risk changes, verify via out-of-band channels, and automate holds when impersonation prevention flags anomalies.
What KPIs matter most in vendor evaluations?
Focus on detection rate versus false positives, dwell time, number of malicious emails prevented, and user-report-to-removal time. Also evaluate dashboard reporting quality, SIEM integration, and support responsiveness.
Are warning banners enough to stop sophisticated phishing attacks?
Banners help, but they must be paired with URL scanning, sandbox detonation, and automated quarantine. User training and phishing simulation further reduce risk from advanced email-based threats.
How do I ensure privacy and compliance in API-based deployments?
Verify data residency, encryption, retention, and least-privilege scopes. Ensure customizable policies and security policies align with regulatory needs and support audit-ready reporting.
Key Takeaways
- Layer anti-phishing software with AI-driven anomaly detection to detect phishing tied to BEC, supplier impersonation, and thread hijacking.
- Integrate email protection with ERP and vendor management to block payment fraud and financial fraud across approval patterns.
- Combine SEG and API-based post-delivery controls for multi-layer protection, mobile coverage, and continuous monitoring.
- Automate response with SIEM/SOAR playbooks, auto-quarantine, retroactive purge, and abuse mailbox triage to reduce dwell time.
- Measure success with rigorous pilots, precise KPIs, strong privacy controls, and threat intelligence that continuously strengthens the prevention platform.

General Manager
General Manager at DuoCircle. Product strategy and commercial lead across the email security portfolio.
Secure your email infrastructure
Protect, authenticate, and deliver. Contact our team to find the right solution.