Email is still the most exploited initial vector of attacks in cybersecurity. Phishing is still considered the number one initial access vector in breach investigations, and at the core of all phishing attacks is domain spoofing.
Attackers register domains similar to legitimate ones, pretend to be legitimate companies, and send convincing emails to users to steal credentials, conduct unauthorized transactions, and spread malware. To defend against these types of attacks, it is necessary to have more than just spam filters; it is necessary to have insight into who is really behind those domains sending those emails to you.
One of the first things security professionals do when trying to understand an email they suspect is malicious is to do a whois domain lookup. A whois domain lookup will provide essential details about a domain, including registration details, registrant contact details, name servers, registrar details, and expiration details. For security teams, this can mean the difference between a well-thought-out response and missing a threat.
This article explores how domain verification fits into a broader email security strategy, why it matters for phishing detection, and what security teams should look for when investigating suspicious domains.
Why Attackers Rely on Domain Spoofing
Domain spoofing is an effective method as it plays on the trust that users have in familiar sender names. For example, an email from payroll@companyname-hr.com or support@micros0ft.com may pass a superficial level of inspection, especially on mobile devices where sender names rather than actual sending domains are used.
Typical phishing attacks use one of the following methods of abusing domains:
- Typosquatting: registering domains with common typos or misspellings of popular domains (e.g., gooogle.com, amaz0n.com)
- Homoglyphs: using Unicode characters to replace common Latin alphabet letters
- Subdomain abuse: using valid subdomains on an attacker’s domain
- Newly registered domains: registering new domains specifically to be used for phishing attacks
All of these methods may bypass superficial checks if not accompanied by checks on domain reputation and verification.
What Domain Verification Reveals About Suspicious Senders
When security analysts investigate a suspicious email, domain verification involves pulling several layers of data. WHOIS records are the starting point.
Registration Age and History
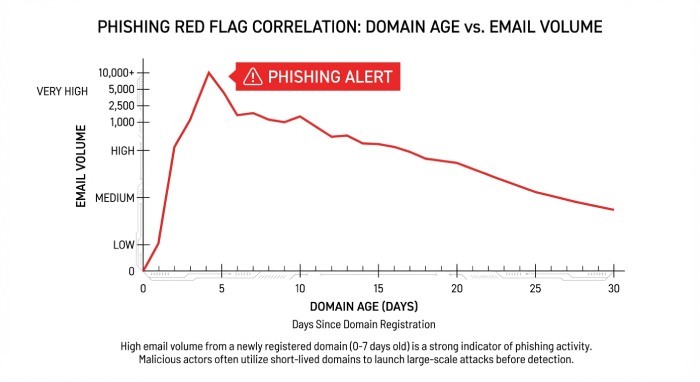
A domain registered within the past 30 days sending bulk email is a significant red flag. Legitimate businesses rarely send high-volume transactional or marketing email from newly minted domains. Phishing operators, by contrast, frequently rotate through freshly registered domains to avoid blocklists. WHOIS records expose this pattern immediately.
Registrant Identity and Privacy Masking
Privacy protection services, while legitimate for personal use, are heavily exploited by phishing operators. When a domain impersonating a known brand has its registrant information entirely redacted behind a privacy proxy, that inconsistency warrants scrutiny. Established organizations almost always have verifiable, consistent domain registration profiles. Mismatches between claimed sender identity and WHOIS records can immediately surface impersonation attempts.
Name Server and Hosting Patterns
Malicious domains often share name server infrastructure across multiple phishing campaigns. Security analysts who identify one suspicious domain can pivot through shared hosting and DNS configurations to uncover related domains operated by the same threat actor. This network mapping is only possible when domain verification is part of the investigation workflow.
The Role of Email Authentication Standards
Domain verification does not operate in isolation. It works in conjunction with three core email authentication standards that every organization should have deployed:
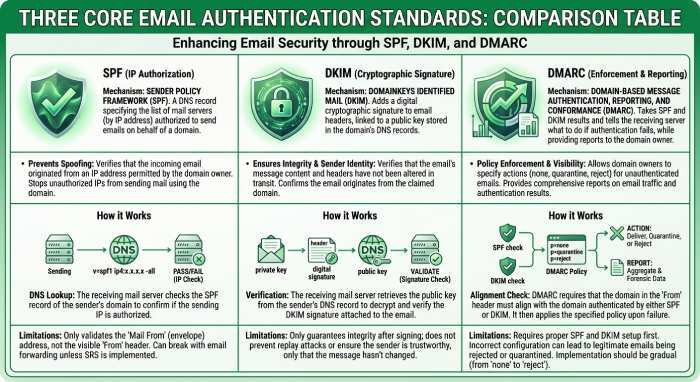
- SPF (Sender Policy Framework): Defines which IP addresses are authorized to send email on behalf of a domain by publishing a DNS TXT record. Receiving mail servers validate the sending IP against the SPF record.
- DKIM (DomainKeys Identified Mail): Attaches a cryptographic signature to outgoing emails, allowing receiving servers to verify that the message was not tampered with in transit and that it genuinely originates from an authorized source.
- DMARC (Domain-based Message Authentication, Reporting & Conformance): Builds on SPF and DKIM by specifying how receiving servers should handle messages that fail authentication, and provides domain owners with aggregate and forensic reports about abuse.
Checking a suspicious domain’s DNS records for SPF, DKIM alignment, and DMARC policy is a fast way to assess its email infrastructure maturity. Legitimate high-volume senders have properly configured authentication records. Phishing domains frequently do not — or if they do, the configurations reveal mismatches with the organization they are impersonating.
It is equally important to verify that your own organization’s domains have strict DMARC policies in place (p=quarantine or p=reject). Without enforcement, attackers can freely spoof your domain in the From header of phishing emails targeting your customers, partners, or employees.
How IT Teams Can Operationalize Domain Verification
Domain verification is best performed as part of a repeatable and systematic process rather than as part of an investigation. The following are some methods to help an organization do this:
- Triage Process: If an email is reported as suspicious, then it should be part of the initial investigation, similar to header analysis and URL scanning.
- Monitoring lookalike domains: Organizations can monitor domains similar to their own using various threat intelligence tools. These tools can automatically monitor lookalike domains.
- Correlation of age and volume of emails: The age of domains can be correlated with the volume of emails being sent from them. If domains are less than 30 days old, they should be considered suspect.
- Auditing your own domains: Organizations should keep track of all domains they own and should have null MX records and strong DMARC policies on unused domains. All domains should have valid SPF and DKIM configurations.
- User education on verifying domains: Users are still an important part of this system. Users should understand how to view full email headers and should be wary of senders who do not have a valid domain matching their company.
Conclusion
Domain verification is a powerful tool, but it is most effective in conjunction with a number of other tools. WHOIS privacy services are often used to hide registrant information, and sophisticated attackers have been known to hijack old legitimate domains to get around age-based filtering. Verification should always be done in conjunction with behavioral analysis, URL scanning, content filtering, and strict SPF, DKIM, and DMARC practices.
Security teams that treat domain intelligence as a real-time control, rather than a static test, are much more likely to catch impersonation attacks in time to prevent domain-based email fraud from reaching users.