Amazon AI Cyberattack, Odido Data Breach, German Rail Targeted – Cybersecurity News [February 16, 2026]
Last week witnessed some of the biggest cyberattacks of recent times. From the German railway to the Odido cyberattack, the threat actors managed to penetrate into the systems of some of the biggest global names. An investigation is already underway to determine the intensity of the recent Amazon AI attack.
Meanwhile, a group of cybercrooks is seen leveraging a viral MMS controversy to extract sensitive data from Indian social media users.
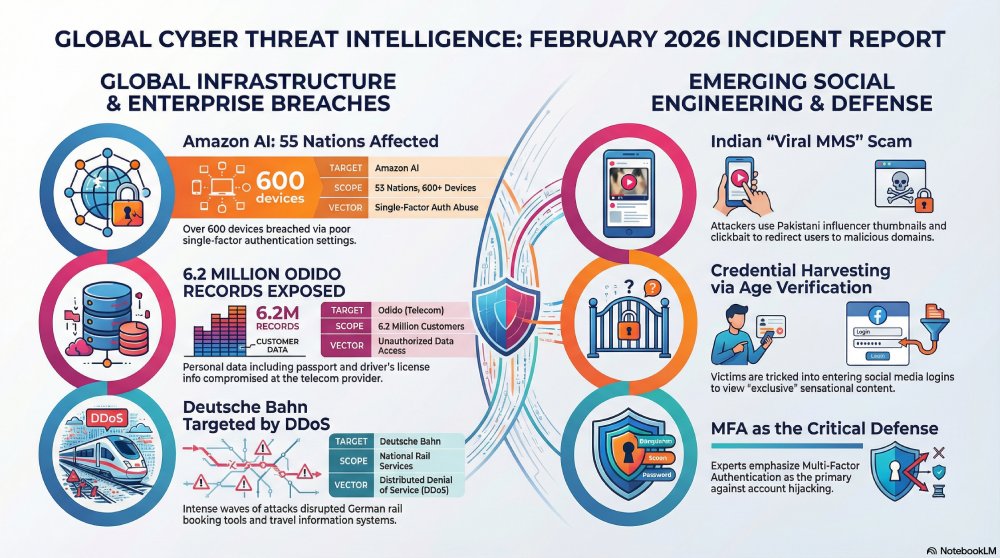
Amazon AI cyberattack affected more than 55 nations!
An investigation is underway for the recent Amazon AI cyberattack. The threat attack managed to gain access to over 600 devices and affected almost 55 nations. Experts believe the campaign was active from January 11 to February 18. Instead of exploiting the vulnerabilities, the cybercrooks abused poor single-factor authentication settings.
The Amazon CISO, Moses, shared that the cyberattackers were not able to exploit the FortiGate software. Once the firewalls were breached, the cybercrooks managed to extract the configurations of the complete device, ranging from administrative passwords to SSL-VPN credentials. It is these stolen credentials that helped the threat actors to penetrate deeper into the internal systems, such as the backup infrastructure.
The researchers at Amazon believe that the cyber incident resembles pre-ransomware staging activities. Such attacks are designed to do the preparations for upcoming cyber campaigns rather than carrying out immediate cyber disruptions.
This attack ushers in a much-needed reminder that with the help of AI, threat actors can easily exploit existing cybersecurity and email security hygiene gaps. Experts believe that organizations must get proactive and start working on their security mechanisms as swiftly as AI is penetrating into every business operation.
A whopping 6.2 million people’s data got compromised in the Odido cyber mishap!
Odido, the renowned telecom services provider, was targeted by a group of threat actors. They managed to gain access to the personal data of a staggering 6.2 million people. The compromised data includes details like dates of birth, customer numbers, addresses, names, phone numbers, driver’s license data, and passport information. However, details like billing information, passwords, and call logs are safe.
A spokesperson for Odido has claimed that the cyber mishap will not affect Odido’s services. Customers are still able to use the internet, watch television, and make necessary calls.
As per the law, Odido has reported the data breach incident to the Dutch Data Protection Authority (AP). The telecom provider is also planning to notify all the affected customers by sharing official emails.
Germany’s national rail operator targeted by threat actors!
Deutsche Bahn, Germany’s national rail operator, fell prey to a cyber mishap recently. On Wednesday, they shared the unfortunate news with everyone. The cyberattack managed to impact the digital services of Deutsche Bahn.
The alleged DDoS attack messed up the IT system of the German rail operator on Tuesday. Because of the attack, booking tools and travel information were affected.
This is not the first time that Deutsche Bahn has been targeted by cyber crooks. But the recent attack was more intense and took place in waves.
The cyber incident took place on Tuesday afternoon. However, Deutsche Bahn managed to contain the situation before it escalated. Most of the systems were up and running by Tuesday evening. However, some disruptions took place again the next morning.
Deutsche Bahn had proper systems in place, and they proactively responded to limit the extent of the damage.
Experts have already warned the German transport infrastructure against potential cyberattacks. Deutsche Bahn experienced a string of “nearly daily attacks” in 2025 summer. The attacks were designed to affect major lines between Berlin and Hamburg, and between Düsseldorf and Cologne.
Cybercrooks are using sensationalization tactics to steal sensitive data in India
A group of threat actors in India is misusing a “viral MMS” controversy to break into the systems of Indian social media users. The threat actors are using misleading and sensational posts to grab the attention of users. Experts have urged people to avoid clicking on any suspicious link that is connected to any sensationalized news.
The threat actors are clever enough to use localisation tactics to gain the attention of the public. They also use clickbait hooks to increase the click-through rate of these malicious posts.
The cyber scam unfolds at multiple levels. First of all, the users receive a blurred or over-hyped thumbnail featuring a popular influencer from the neighboring country, Pakistan. The thumbnail comes with a malicious link that redirects the user to a suspicious domain. Next, the victims are asked to “verify age.” This can be done only when a victim enters their social media credentials. Or, in some cases, the scammers also install spyware or adware in the background. The login details are abused for carrying out financial fraud or hijacking accounts with weak security setups.
Experts have shared multiple guidelines to prevent such cyber scams. If you receive a link that asks you to share the same link with a fixed number of people in order to access the content, then it is highly likely to be a malicious link.
Besides, one must not click on any link that looks shortened or does not come from a verified domain.
Lastly, if the news you are seeing seems out of place or there is a context mismatch, then it is better to avoid such social media posts.
If someone clicks on such malicious links, they must immediately delete the message. Next, they should clear the browser cache and cookies, but only after closing the suspicious tab.
You can also revoke unnecessary access granted to unknown applications on your phone. Enabling multi-factor authentication can significantly prevent cybercriminals from accessing your banking apps, social media profiles, or email IDs.
Digital awareness serves as the very first line of defence against such cyber scams that use social engineering tactics to catch victims off guard.