A data-driven analysis of 26 primary-source statistics from institutional reports by the World Economic Forum, IBM, Verizon, Cisco, Accenture, ISC2, NIST, and others.
Introduction: A Year of Paradoxes
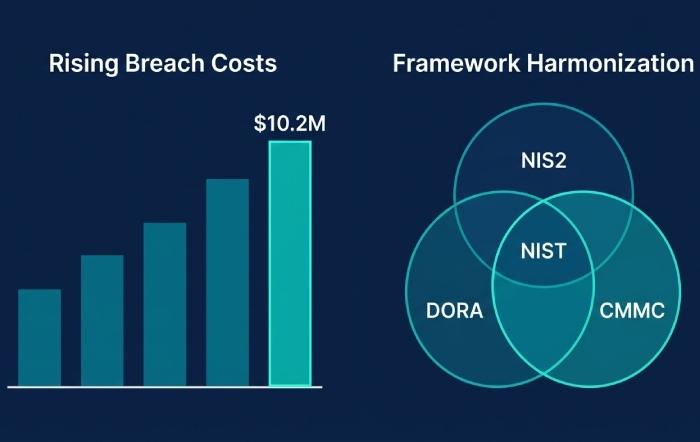
Cybersecurity in 2026 is a story of contradictions. For the first time in half a decade, the global average cost of a data breach has actually fallen, dropping nine percent to $4.44 million according to the IBM/Ponemon Cost of a Data Breach Report 2025. That sounds like progress. But zoom into the United States, and the picture inverts: American breach costs surged nine percent to an all-time record of $10.22 million, driven by escalating regulatory fines and the sheer complexity of containing breaches in AI-saturated environments.
Meanwhile, the World Economic Forum’s Global Cybersecurity Outlook 2026, surveying 804 leaders across 92 countries, found that 94 percent of respondents now identify artificial intelligence as the single most significant driver of cybersecurity change. That same AI is simultaneously the most powerful defensive tool organizations have ever wielded and the most dangerous accelerant of offensive capabilities adversaries have ever exploited.
This blog post goes beyond the headlines. Drawing on 26 statistics sourced from government agencies, international institutions, and industry research reports, it places the raw data into context, explains what each finding means for real organizations, and provides concrete, actionable next steps. Whether you are a CISO building a board presentation, a security analyst justifying budget, or a journalist covering the industry, these are the numbers and narratives that matter most right now.
1. The AI Double Edge: Both Sword and Shield
No single force is reshaping cybersecurity faster than artificial intelligence. The data on this point is unambiguous.
What the Data Says
According to the WEF Global Cybersecurity Outlook 2026, 94 percent of survey respondents identify AI as the most significant driver of cybersecurity change in 2026. Even more telling, 87 percent flagged AI-related vulnerabilities as the fastest-growing cyber risk throughout 2025. These are not projections from futurists. These are assessments from 316 CISOs, 105 CEOs, and 123 C-suite executives actively managing cybersecurity programs today.
On the offensive side, the IBM Cost of a Data Breach Report 2025 found that 16 percent of breaches now involve attacker use of AI, primarily concentrated in phishing (37 percent of AI-assisted breaches) and deepfake impersonation (35 percent). Shadow AI, the unsanctioned use of AI tools by employees, was a contributing factor in 20 percent of breaches, adding an average of $670,000 to breach costs.
On the defensive side, the same IBM report revealed that organizations using AI-powered security tools extensively cut their breach lifecycle by 80 days and saved nearly $1.9 million on average compared to organizations that did not deploy such tools.
97% of breached organizations that experienced an AI-related security incident lacked proper AI access controls. 63% had no AI governance policies at all. — IBM/Ponemon, Cost of a Data Breach Report 2025
What This Means
The data reveals a dangerous governance vacuum. Organizations are racing to adopt AI for competitive advantage, but the security infrastructure has not kept pace with the deployment velocity. The Cisco 2025 Cybersecurity Readiness Index underscores this gap: 60 percent of IT teams report they cannot see specific prompts or requests made by employees using GenAI tools, and 60 percent lack confidence in their ability to detect unapproved AI tool usage.
The Accenture State of Cybersecurity Resilience 2025 report deepens this concern: 77 percent of organizations lack the ability to defend against AI-enabled threats, and 83 percent have not established a secure cloud foundation with integrated monitoring for AI workloads. Only 34 percent of organizations globally have what Accenture considers a mature cyber strategy.
Put simply: AI is being deployed faster than it is being governed, and the cost of that oversight gap is already measurable in breach data. The organizations that are winning are not the ones avoiding AI. They are the ones deploying it with governance guardrails from day one.
What to Do Next
- Establish an AI governance policy before expanding AI deployments. The IBM data shows that the absence of governance is the single most correlated factor in AI-related breach costs. A governance policy does not need to be perfect on day one, but it needs to exist and cover, at minimum, approved tools, data classification for AI inputs, access controls, and audit schedules.
- Conduct a shadow AI audit. Use endpoint monitoring tools to identify which AI services employees are accessing, with what credentials, and what data they are feeding into those tools. The Cisco data suggests most organizations are flying blind here.
- Invest in AI-powered defense. The $1.9 million in savings and 80-day reduction in breach lifecycles documented by IBM are compelling ROI metrics. Prioritize AI deployment in threat detection, automated triage, and incident response workflows.
- Red-team your AI. The WEF report notes that the percentage of organizations assessing the security of AI tools nearly doubled from 37 percent in 2025 to 64 percent in 2026. Join that growing majority. Test your AI systems against prompt injection, data poisoning, and model theft scenarios.
2. Ransomware: The Economics Are Shifting, But the Threat Is Not Shrinking
What the Data Says
The Verizon 2025 Data Breach Investigations Report (DBIR), which analyzed over 22,000 security incidents and 12,195 confirmed breaches, found that ransomware is now present in 44 percent of all breaches, up from 32 percent the prior year, a 37 percent year-over-year increase. For small and medium-sized businesses, the picture is even more stark: ransomware appeared in 88 percent of SMB breaches.
The IBM Cost of a Data Breach Report 2025 pegs the average cost of a ransomware breach at $5.08 million. The KnowBe4 Global Cost of Ransomware infographic, drawing on Cybersecurity Ventures data, projects global ransomware damages at $71.5 billion in 2026 and a staggering $265 billion by 2031.
But here is the counternarrative: victims are fighting back. According to the Verizon DBIR 2025, 64 percent of ransomware victims now refuse to pay, up from 50 percent just two years prior. The Chainalysis 2025 Crypto Crime Ransomware Report confirmed that total cryptocurrency ransom payments fell 35 percent to $813 million in 2024, even as the number of attacks surged. This means more attacks are generating roughly the same aggregate revenue, because a shrinking share of victims are actually paying.
What This Means
The ransomware economy is undergoing a structural shift. The attackers are not going away. In fact, the number of ransomware groups and affiliates is proliferating, with over 55 new groups appearing in 2024 alone according to industry tracking. But the financial incentives are being eroded from multiple directions simultaneously: better backup strategies, law enforcement disruptions such as Operation Cronos against LockBit, increasing government guidance against payments, and cyber insurance providers tightening coverage requirements.
The IBM data adds an important financial insight: organizations that involved law enforcement in ransomware incidents saved an average of $990,000 per breach ($4.38 million versus $5.37 million without law enforcement). That is an 18 percent cost reduction for an action that costs nothing. Yet paradoxically, fewer victims reported involving law enforcement in 2025 (40 percent) compared to 2024 (53 percent).
For SMBs, the situation remains critical. The Verizon finding that ransomware appears in 88 percent of SMB breaches reflects a deliberate tactical shift by ransomware operators. As large enterprises harden their defenses, criminals are moving downstream to smaller targets with less mature security postures but enough revenue to generate meaningful ransom payments.
What to Do Next
- Treat ransomware as a primary, not secondary, threat. With ransomware present in 44 percent of all breaches and climbing, every organization, regardless of size, needs a ransomware-specific incident response plan that is tested at least quarterly.
- Invest in immutable, air-gapped backups. Industry data from Veeam shows that 96 percent of ransomware attacks target backup systems, and 76 percent succeed in compromising them. The single highest-ROI investment in ransomware resilience is backup infrastructure that attackers cannot reach or modify.
- Always involve law enforcement. The $990,000 average savings documented by IBM is a compelling argument. The FBI, CISA, and equivalent agencies in other countries can provide decryption tools, intelligence on the threat actor, and coordination that materially improves outcomes.
- Do not pay the ransom unless there is truly no alternative. Eighty percent of organizations that pay are re-attacked within 12 months according to Fortinet, and only four percent recover all their data. The economics strongly favor investing in prevention and recovery over ransom payment.
3. The Evolving Breach Landscape: Third Parties, Edge Devices, and the Shrinking Detection Window
What the Data Says
The Verizon 2025 DBIR documented one of the most dramatic shifts in recent breach history: 30 percent of all breaches now involve third-party partners or vendors, double the 15 percent reported the prior year. This is not a marginal change. This is a structural reconfiguration of how breaches happen.
Simultaneously, vulnerability exploitation as an initial access vector saw a 34 percent increase, now accounting for 20 percent of all breaches. Within that category, exploitation of edge devices like VPNs surged from 3 percent to 22 percent of vulnerability-based breaches, an eight-fold increase. For these critical edge device vulnerabilities, the median time between a flaw’s public disclosure and mass exploitation by attackers was zero days, rendering traditional patch-cycle-based defenses entirely insufficient.
There is, however, a genuine bright spot in detection speed. The IBM Cost of a Data Breach Report 2025 found that the mean time to identify and contain a breach fell to 241 days, the lowest in nine years, down from 258 days in 2024. Organizations leveraging AI and automation in their security operations were the primary drivers of this improvement.
What This Means
The doubling of third-party breaches represents a fundamental challenge to traditional perimeter-based security models. Organizations can no longer assess their own risk in isolation. The security posture of every vendor, partner, and service provider in the supply chain is now directly material to an organization’s own breach exposure. The Snowflake breaches of 2024, where threat actors exploited the fact that certain customers were not enforcing multi-factor authentication, are a cautionary example: a single vendor’s security gap affected approximately 165 downstream organizations.
The edge device explosion is equally consequential. VPNs, firewalls, and network routers are, by design, internet-facing. They typically lack the endpoint detection and response (EDR) tooling that protects user devices, creating a blind spot that attackers are aggressively exploiting. The Verizon data shows that even among organizations aware of the problem, only 54 percent of edge device vulnerabilities were fully remediated during the reporting period, with a median remediation time of 32 days, an eternity when exploitation begins on day zero.
What to Do Next
- Implement formal third-party cyber risk assessments. Require vendors to demonstrate security maturity through certifications like SOC 2 Type II or ISO 27001, mandate MFA for all partner access, and establish contractual accountability for security failures. Review your vendor risk quarterly, not annually.
- Prioritize edge device patching above all other vulnerability management. Given the zero-day exploitation timeline, calendar-based patching cycles are insufficient for internet-facing infrastructure. Implement automated patch deployment for edge devices and consider segmenting VPN and firewall management networks from general enterprise infrastructure.
- Deploy continuous monitoring on network devices. These assets need the same level of security instrumentation as endpoints. If your EDR vendor does not support network infrastructure devices, explore dedicated firmware integrity monitoring solutions.
- Reduce your third-party attack surface. Audit which vendors have access to your environment, what level of access they hold, and whether that access is genuinely necessary. Apply the principle of least privilege aggressively to all partner and vendor connections.
4. The Workforce Crisis: It Is Not Just About Headcount
What the Data Says
The cybersecurity workforce gap remains one of the most persistent structural challenges in the industry. According to the ISC2 2024 Cybersecurity Workforce Study, the global shortage stands at 4.7 million cybersecurity professionals. In the United States alone, the NIST NICE Workforce Demand report (July 2025) shows 457,398 unfilled cybersecurity job openings against an existing workforce of 1.25 million, a supply-to-demand ratio of roughly 2.7 employed workers for every open position.
But the ISC2 data reveals something more nuanced than a simple headcount problem: 90 percent of cybersecurity professionals report having one or more skills gaps on their teams, and 64 percent believe these skills gaps have a more significant negative impact on organizational security than staffing shortages alone. The problem is not merely that there are not enough people. It is that the people who are available do not have the right skills for the threats they face.
The WEF Global Cybersecurity Outlook 2026 reinforces this finding: 54 percent of respondents identified limited knowledge and skills as the key obstacle to adopting AI-driven cybersecurity solutions, ranking it above concerns about risk or cost. The skills gap is not just making organizations vulnerable to yesterday’s threats. It is preventing them from deploying tomorrow’s defenses.
What This Means
The workforce crisis is self-reinforcing. Organizations that cannot hire enough skilled professionals fall behind on security maturity. That immaturity increases breach risk, which increases costs, which constrains the budget available for hiring and training. The OECD’s analysis of the cybersecurity workforce across five countries found that the workforce gap has grown more than twice as fast as the workforce itself, meaning the problem is accelerating, not stabilizing.
There is also a critical diversity dimension. Women represent only about 24 percent of the global cybersecurity workforce according to ISC2 data. This is not only an equity issue; it is a talent pipeline issue. The industry is attempting to fill 4.7 million positions while effectively recruiting from roughly three-quarters of the available labor pool.
What to Do Next
- Invest in upskilling your existing team, not just hiring. Given that 90 percent of teams have skills gaps, the fastest path to improved security is often training the people you already have, especially in AI, cloud security, and threat detection.
- Broaden your hiring criteria. The NIST and ISC2 data consistently shows that the most effective workforce strategies prioritize demonstrable technical capability and certifications over four-year degree requirements. Candidates from adjacent fields like systems administration, network engineering, and software development can often transition into cybersecurity roles with targeted training.
- Use AI to extend your team’s capacity. If you cannot hire enough analysts, deploy AI-powered security tools to handle alert triage, log analysis, and threat intelligence correlation. The IBM data shows this approach delivers measurable cost savings while reducing the burden on overstretched human teams.
- Invest in diversity initiatives. Organizations that actively recruit from underrepresented groups are not just doing the right thing ethically; they are accessing a larger talent pool in a market where every additional qualified candidate matters.
5. The Readiness Gap: Most Organizations Are Not Prepared for What Is Coming
What the Data Says
The Cisco 2025 Cybersecurity Readiness Index delivers perhaps the most sobering readiness assessment in the industry: only four to six percent of organizations globally are classified as ‘Mature’ in their cybersecurity readiness. Seventy percent remain in the bottom two categories (Formative or Beginner), with little change from the prior year.
The Accenture State of Cybersecurity Resilience 2025 reaches a similar conclusion from a different angle: only 34 percent of organizations have a mature cyber strategy, and a mere 13 percent are positioned to defend against AI-powered attacks. Accenture’s economic analysis projects 80 percent industry-wide growth in AI adoption over the next decade, which means the gap between AI deployment velocity and AI security readiness is likely to widen before it narrows.
The WEF report adds a geopolitical dimension: 65 percent of organizations now factor geopolitically motivated cyberattacks into their risk strategies, and 91 percent of the largest enterprises have adjusted their cybersecurity posture accordingly. However, less than 45 percent of private-sector CEOs are confident in their country’s ability to respond to major cyber incidents targeting critical infrastructure.
What This Means
There is a widening chasm between the small minority of organizations that are genuinely cyber-resilient and the vast majority that are not. This is not merely an organizational problem. It is a systemic one. Because modern economies are deeply interconnected through digital supply chains, cloud services, and shared infrastructure, the vulnerabilities of the least-prepared organizations create risk for everyone. A single under-protected vendor can be the entry point that cascades into a breach affecting dozens of downstream organizations, as the doubling of third-party breaches demonstrates.
The CEO confidence gap is particularly concerning. If national leaders are not confident their countries can respond to critical infrastructure attacks, and if fewer than half of CEOs share that confidence, then the threat of systemic, cascading cyber events remains very real. The Colonial Pipeline incident of 2021 and the Change Healthcare breach of 2024 (which cost approximately $3 billion) are not anomalies. They are harbingers of what under-investment in readiness produces.
What to Do Next
- Benchmark your maturity. Use frameworks like the NIST Cybersecurity Framework 2.0 or the Cisco Readiness Index methodology to honestly assess where your organization stands. Knowing you are in the ‘Formative’ category is the prerequisite for building a credible roadmap to ‘Mature.’
- Tie cybersecurity investment to business risk, not IT budget. The data consistently shows that organizations treating cybersecurity as a strategic business risk, with board-level oversight and C-suite accountability, achieve measurably better outcomes than those treating it as an IT operational expense.
- Plan for geopolitical disruption. With 65 percent of organizations now factoring geopolitics into their risk strategies, this is no longer a niche concern. Assess your exposure to state-sponsored threats based on your industry, geography, and supply chain, and develop playbooks for scenarios involving critical infrastructure targeting.
- Test your resilience, not just your prevention. Mature cybersecurity is not about preventing every attack. It is about absorbing shocks and recovering quickly. Conduct regular tabletop exercises, test backup restoration, practice incident communication, and ensure your insurance coverage reflects your actual risk profile.
6. Regulatory & Compliance Trends: The Era of Cybersecurity Regulation Is Here
The regulatory landscape has undergone a dramatic expansion. The European Union’s NIS2 Directive broadens mandatory cybersecurity requirements to 18 sectors, including banking, energy, healthcare, and digital infrastructure. The Digital Operational Resilience Act (DORA) imposes specific ICT risk management and incident reporting requirements on the EU’s 22,000 financial entities. According to the ENISA Technical Implementation Guidance on NIS2, the regulation consists of 13 titles with granular technical and methodological requirements for risk management.
In the United States, the surge in U.S. breach costs to $10.22 million is directly linked to higher regulatory fines and escalating compliance requirements. The ECSO White Paper on NIS2 Implementation Challenges notes that organizations with previous regulatory experience demonstrate more mature implementation strategies, while newly regulated sectors face steeper adaptation curves, and SMEs face disproportionate resource allocation challenges.
The WEF Global Cybersecurity Outlook 2026 identifies regulatory proliferation as one of the compounding factors increasing cybersecurity complexity. The fragmentation of certifications across geographies (EU CRA, ISMAP, ACN, ENS) and verticals (DORA, TISAX, CMMC) creates duplicative compliance burdens that hinder rather than help security improvement.
What to Do Next
- Map your regulatory exposure now. If you operate in or serve customers in the EU, NIS2 and DORA compliance is not optional. Conduct a gap assessment against these frameworks before enforcement actions begin.
- Harmonize compliance efforts. Rather than treating each regulation as a separate initiative, map your existing controls to multiple frameworks simultaneously. A well-implemented NIST CSF program will satisfy significant portions of NIS2, DORA, CMMC, and ISO 27001 requirements.
- Factor regulatory fines into your risk calculus. The IBM data showing U.S. breach costs rising while global costs fell is directly attributable to regulatory penalties. Under-investing in compliance is now more expensive than investing in it.
7. The Fraud Epidemic: When Cybersecurity Becomes a Consumer Problem
One of the most striking findings in the WEF Global Cybersecurity Outlook 2026 is the sheer prevalence of cyber-enabled fraud. Seventy-three percent of respondents reported that they or someone in their professional or personal network had been personally affected by cyber-enabled fraud over the course of 2025. Phishing, vishing, and smishing attacks were the most common vector at 62 percent, followed by invoice and payment fraud at 37 percent.
Cyber-enabled fraud has overtaken ransomware as the top cybersecurity concern of business leaders. CEOs now rate it as their number one concern, with data leaks (30 percent) and the advancement of adversarial capabilities through generative AI (28 percent) identified as their primary security worries related to AI specifically.
The WEF Global Cybersecurity Outlook 2025 provided additional context: the Global Anti-Scam Alliance estimated that scammers siphoned more than $1 trillion globally in the past year, costing certain countries losses exceeding three percent of GDP. The entry of traditional organized crime groups into the cybercrime arena, including the trafficking of over 220,000 people to work in online scam farms in Southeast Asia, illustrates how cybercrime has become intertwined with broader criminal enterprises.
What to Do Next
- Deploy AI-powered fraud detection. If AI is making phishing and social engineering more convincing, the defensive response must also be AI-powered. Invest in email security platforms with real-time AI analysis, voice authentication for high-value transactions, and behavioral analytics for payment processing.
- Train employees specifically on AI-generated threats. Traditional security awareness training focused on spotting grammatical errors or suspicious formatting is no longer sufficient. AI-generated phishing is grammatically flawless and contextually convincing. Training programs need to evolve to teach verification behaviors rather than pattern recognition.
- Implement multi-channel verification for all financial transactions. No wire transfer, vendor payment change, or credential reset should proceed based solely on a single communication channel. Require out-of-band confirmation for any action involving money or access.
Conclusion: Cybersecurity in 2026 Is a Leadership Problem, Not Just a Technology Problem
The data across all of these reports converges on a single, inescapable conclusion: the organizations that are winning at cybersecurity in 2026 are not the ones with the biggest budgets or the most advanced tools. They are the ones with the strongest governance, the clearest accountability, and the most disciplined approach to fundamentals.
The global average breach cost fell because organizations got faster at detecting and containing incidents, primarily through AI-powered tools. U.S. breach costs rose because regulatory environments penalized organizations that had not invested adequately in prevention and governance. Ransomware payments declined because victims invested in backup infrastructure and refused to fund criminal enterprises. Third-party breaches doubled because organizations failed to extend their security posture to their supply chains.
Every one of these outcomes traces back to a leadership decision made months or years before the breach occurred. Cybersecurity in 2026 is not a technology problem waiting for a technology solution. It is a governance problem, a resource allocation problem, a talent development problem, and a supply chain management problem that happens to manifest through technology.
The data is clear. The path forward is clear. The question is whether organizations will act on both before the next breach makes the decision for them.