Medtronic Cyberattack Confirmed, cPanel Ransomware Wave, Root Access Granted – Cybersecurity News [April 27, 2026]
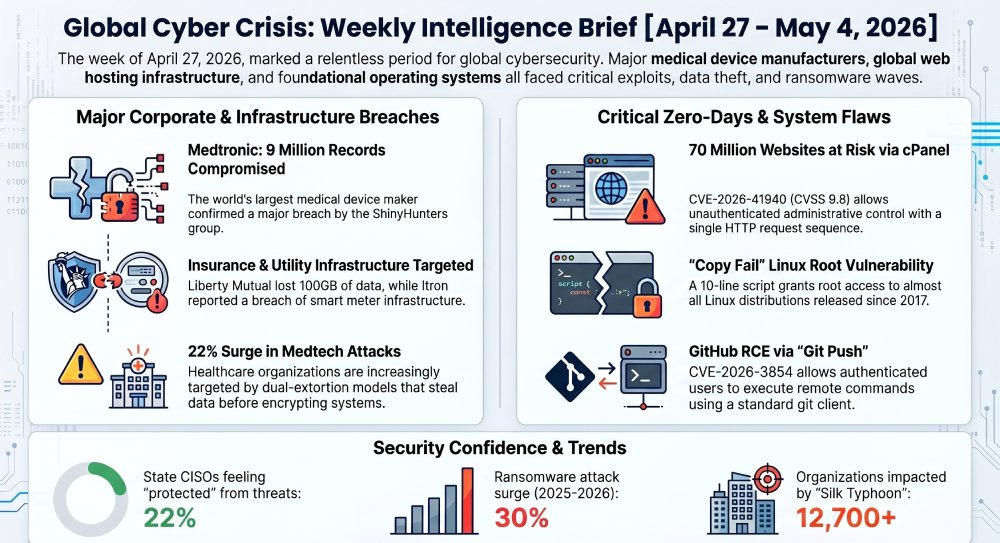
Here’s your weekly roundup of the most significant cybersecurity stories from the past week, covering major data breaches, critical vulnerabilities, law enforcement actions, and the evolving threat landscape. It’s been an exceptionally busy week, with the medical device sector under siege, a devastating cPanel zero-day wreaking havoc across millions of websites, and a landmark extradition of a Chinese state-linked hacker making headlines.
Medtronic, world’s largest medical device maker, confirms major cyberattack
Medical device giant Medtronic confirmed over the weekend that its systems had been hacked by an unauthorized party. The ShinyHunters cybercrime group listed Medtronic on its leak website on April 17, claiming to have compromised more than 9 million records containing personal information, along with terabytes of corporate information. The hackers set an April 21 ransom deadline, and Medtronic has since been removed from ShinyHunters’ website, indicating that the organization may have paid a ransom.
The incident highlights growing cybersecurity risks in the medtech sector, with cybergangs increasingly using phishing and other social engineering tactics to gain access to data. Medtronic stated manufacturing, distribution, and patient care were not disrupted, but the medical device maker is already facing at least a half-dozen proposed federal class action lawsuits just days after confirming the breach.
Critical cPanel zero-day CVE-2026-41940 hits 70 million websites in “Sorry” ransomware wave
A critical vulnerability in cPanel and WHM — the control panels that quietly run a large share of the world’s small business websites, mail servers, and DNS records — lets an unauthenticated attacker take full administrative control of the host with a single sequence of HTTP requests. No password. No phishing. No malware on the user’s side.
CVE-2026-41940 carries a CVSS score of 9.8 (Critical), is pre-authentication, and is network-reachable. Approximately 1.5 million internet-exposed cPanel instances were at risk. Exploitation was observed since approximately February 23, 2026, meaning this was a true zero-day for roughly two months before cPanel’s emergency patch on April 28.
The flaw was being mass-exploited to breach websites and encrypt data in “Sorry” ransomware attacks. At least 44,000 IP addresses running cPanel have since been compromised in ongoing attacks. On April 30, 2026, CISA added CVE-2026-41940 to its Known Exploited Vulnerabilities catalog, mandating federal agencies to patch by May 3, 2026. Bleeping Computer I Am Tzar
“Copy Fail” Linux kernel flaw gives root access to virtually every Linux system since 2017
Cybersecurity researchers have disclosed details of a Linux local privilege escalation flaw that could allow an unprivileged local user to obtain root. The high-severity vulnerability tracked as CVE-2026-31431 has been codenamed Copy Fail. “An unprivileged local user can write four controlled bytes into the page cache of any readable file on a Linux system, and use that to gain root.”
The proof of concept exploit is a 10-line, 732-byte Python script capable of editing a setuid binary to gain root on almost all Linux distributions released since 2017. What makes this especially alarming is that the exploit requires no race conditions, retries, or crash-prone timing windows — the same exact script works on every tested distribution and architecture, including Ubuntu, Amazon Linux, RHEL, and SUSE. Cloud and Kubernetes environments are particularly at risk, as the flaw can also serve as a container escape primitive.
GitHub critical RCE flaw (CVE-2026-3854) exploitable with a single git push
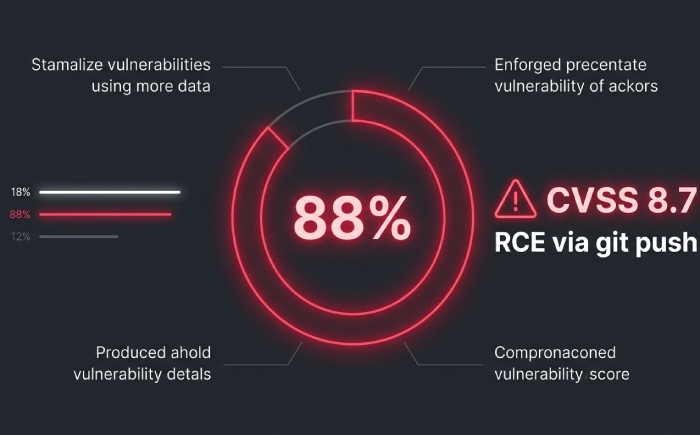
Cybersecurity researchers disclosed a critical security vulnerability impacting GitHub.com and GitHub Enterprise Server that could allow an authenticated user to obtain remote code execution with a single “git push” command. The flaw, tracked as CVE-2026-3854 (CVSS score: 8.7), is a case of command injection that could allow an attacker with push access to a repository to achieve remote code execution on the instance.
Any authenticated user could execute arbitrary commands on GitHub’s backend servers with a single git push command — using nothing but a standard git client. This is one of the first critical vulnerabilities discovered in closed-source binaries using AI. Wiz reports that 88% of self-hosted GitHub Enterprise Server instances are still vulnerable as of public disclosure. GitHub Enterprise Server users are urged to upgrade immediately.
Silk Typhoon hacker extradited from Italy to face US charges over pandemic-era cyberattacks
A Chinese national accused of carrying out cyberespionage operations for China’s intelligence services has been extradited from Italy to the United States to face criminal charges. Xu Zewei was heavily involved in cyberattacks conducted by HAFNIUM, also known as Silk Typhoon, which targeted over 60,000 U.S. entities and successfully victimized more than 12,700 in order to steal sensitive information.
Those organizations impacted by the spate of attacks varied from defence contractors and law firms to think tanks and infectious disease researchers. If convicted on all charges — which include wire fraud, conspiracy to damage protected computers, and aggravated identity theft — Xu could spend decades in prison. China has denied involvement and opposed the extradition.
Liberty Mutual claimed by Everest ransomware group — 100+ GB of policyholder data allegedly stolen
US insurance giant Liberty Mutual has been claimed by the Everest ransomware group, allegedly exposing over 100 GB of data, including the personal and financial information of thousands of individual policyholders. Liberty Mutual appeared on the ransomware gang’s dark leak site with a three-day deadline to make contact with the group. Everest runs a double-extortion model — stealing data, encrypting systems, and threatening to publish files if victims don’t pay.
In recent months, Everest has claimed attacks on BMW, Collins Aerospace, and Coca-Cola’s Middle East division, making Liberty Mutual the latest in an alarming string of high-profile corporate victims.
PyTorch Lightning Python package poisoned in supply chain attack
In yet another software supply chain attack, threat actors compromised the popular Python package Lightning to push two malicious versions to conduct credential theft. The two malicious versions are 2.6.2 and 2.6.3, both of which were published on April 30, 2026. The campaign is assessed to be an extension of the Mini Shai-Hulud supply chain incident that targeted SAP-related npm packages.
The malicious package includes a hidden _runtime directory containing a downloader and an obfuscated JavaScript payload. The PyPI repository has since quarantined the project. PyTorch Lightning is a widely used open-source framework with over 31,100 GitHub stars, meaning this attack had the potential to reach a significant number of developers globally.
Two cybersecurity professionals sentenced to prison for BlackCat ransomware attacks
In a stark reminder that insiders pose serious threats, the U.S. Department of Justice announced the sentencing of two cybersecurity professionals to four years each in prison for their role in facilitating BlackCat ransomware attacks. Ryan Goldberg, 40, of Georgia, and Kevin Martin, 36, of Texas, were accused of deploying ransomware against multiple victims located throughout the U.S. between April and December 2023.
The three men agreed to pay the ALPHV BlackCat administrators a 20% share of any ransoms received in exchange for access to the ransomware and extortion platform. One of the conspirators abused his role as a negotiator to extract higher payouts from victims by sharing confidential information about their insurance policy limits with the BlackCat operators.
Medtronic attack part of wave targeting medical device manufacturers in 2026
The Medtronic breach was not an isolated event. Medtronic becomes the latest major medical device manufacturer targeted by cybercriminals in 2026, joining Stryker, Intuitive Surgical, and UFP Technologies in a wave of attacks that highlights the industry’s growing vulnerability to sophisticated threat actors. Ransomware attacks surged 30% in 2025, and 22% of healthcare organizations have experienced at least one cyberattack targeting medical devices.
The attack on Stryker left the company scrambling for weeks, wiped data from employee electronic devices, and caused some surgeries to be temporarily postponed due to delivery delays. Security experts warn that dual-extortion models — where hackers steal sensitive data before encrypting systems — have fundamentally changed the threat landscape for healthcare.
Itron, the $4B utility technology firm, also hacked — smart meter infrastructure at risk
Flying somewhat under the radar, digital intruders recently broke into utility-technology firm Itron, according to a filing with federal regulators. Itron, in a late Friday SEC filing, said it was notified about an unauthorized third-party break-in on April 13. The company provides smart meters, sensors, and software for energy, water, and city management. The firm stated it alerted law enforcement and worked with external cybersecurity advisors to investigate, and has not observed any subsequent unauthorized activity. The breach raises fresh concerns about the security of critical infrastructure that manages power and water delivery to millions.
DEEP#DOOR Python backdoor discovered — silently targeting enterprise administrators
Cybersecurity researchers disclosed details of a stealthy Python-based backdoor framework called DEEP#DOOR that comes with capabilities to establish persistent access and harvest a wide range of sensitive information from compromised hosts. The intrusion chain begins with execution of a batch script that disables Windows security controls, dynamically extracts an embedded Python payload, and establishes persistence through multiple mechanisms including Startup folder scripts, registry Run keys, scheduled tasks, and optional WMI subscriptions.
The campaign specifically targets high-privilege accounts belonging to enterprise administrators, DevOps engineers, and security analysts by impersonating administrative utilities, and employs SEO poisoning, a dual-stage GitHub distribution architecture, and blockchain-based command-and-control resolving to maintain a highly resilient delivery mechanism.
US state CISOs sound alarm — only 22% say their data is protected from cyberthreats
State CISO confidence has collapsed, with just 22% saying their data is protected from cyberthreats. The 2026 NASCIO-Deloitte study points to AI-enabled attacks, third-party vendor risk, and the worst budget picture in years as states rethink how they defend public data.
The findings paint a troubling picture of public sector cybersecurity, where budget constraints, expanding AI-driven attack surfaces, and reliance on third-party vendors are leaving government systems dangerously exposed. Experts are calling on state governments to elevate cyber resilience to a board-level priority.
FBI alerts freight industry — criminal networks hacking trucking brokers and carriers to steal cargo
A new alert from the FBI says criminal enterprises are hacking both brokers and carriers to steal cargo for resale. The alert highlights a growing trend of cybercriminals infiltrating logistics systems not for data, but for physical goods — a convergence of digital and physical crime that is particularly difficult to defend against. Stolen cargo is then resold, making these attacks financially lucrative with minimal technical sophistication required after initial access.
Pre-Stuxnet malware “fast16” discovered — dates back to 2005, predates known cyber weapons
Cybersecurity researchers discovered a new Lua-based malware created years before the notorious Stuxnet worm that aimed to sabotage Iran’s nuclear program. The previously undocumented cyber sabotage framework dates back to 2005 and primarily targeted high-precision calculation software to tamper with results. It has been codenamed fast16.
Fast16 is estimated to predate Stuxnet — the world’s first known digital weapon designed for disruptive actions — by at least five years, and also precedes the earliest known samples of Flame, another sophisticated malware. The discovery rewrites the known history of state-sponsored cyberweapons and suggests that sophisticated nation-state cyber operations began far earlier than previously understood. The Hacker News
15. Europol and international partners dismantle massive online investment fraud network
Europol, Eurojust, and law enforcement authorities from Austria and Albania have put a stop to a criminal network running a massive online investment fraud scam. The takedown involved coordinated raids across multiple countries and targeted infrastructure used to deceive victims into making fraudulent investment deposits. Online investment fraud has become one of the fastest-growing forms of cybercrime in Europe, with criminal networks increasingly leveraging spoofed websites, deepfake video, and AI-generated content to lend credibility to fake schemes. Cybernews
16. Microsoft Entra ID flaw patched — could have allowed service principal takeover
Microsoft patched an Entra ID role flaw that enabled service principal takeover. The vulnerability exposed cloud environments running Microsoft’s identity and access management platform to privilege escalation attacks. Attackers could have potentially exploited the flaw to assume the permissions of service principals — automated accounts used to manage cloud resources — effectively granting them elevated access to entire Azure environments. Organizations running Entra ID are urged to apply the latest updates immediately and review their service principal permission models.
17. April 2026 Patch Tuesday — 67 flaws fixed, including 2 actively exploited zero-days
April 2026 Patch Tuesday addressed 67 flaws, including 2 zero-day vulnerabilities. Organizations are recommended to immediately patch systems to prevent threat exposure. The release was one of the more substantial monthly patch drops in recent memory and, combined with the cPanel zero-day and Copy Fail Linux vulnerability disclosed in the same week, put IT security teams under enormous pressure to triage and apply critical patches simultaneously across multiple platforms and operating systems. SharkStriker
That’s a wrap on this week’s cybersecurity roundup! From the continuing medtech siege and a cPanel flaw affecting 70 million websites, to a landmark extradition and a Linux kernel vulnerability hiding since 2017, the week of April 27–May 4 was relentless for the cybersecurity community. Stay vigilant, patch early, and keep your incident response plans sharp.