Deploying DMARC the right way: Here’s what MSPs and enterprises should know
On the surface, DMARC deployment is simple. In theory, all it requires you to do is publish a DNS record and enable monitoring—that’s all. But in reality, this approach does not really work for MSPs and enterprises. The entire purpose of implementing DMARC is negated if the authentication protocol is stuck at “p=none” for your email-sending domain.
For MSPs and enterprises, DMARC cannot be seen as a protocol that you set and forget; it requires a strategic approach to move beyond mere monitoring and into true enforcement. The problem with most DMARC deployment guides is that they don’t go beyond the basics of DMARC implementation and address the operational challenges that you might face along the way, especially if you have multiple email senders, third-party platforms, legacy systems sending mail on your behalf, or manage multiple clients at the same time.
In this guide, we will take you through the practical steps that you must follow to ensure that your outbound emails securely reach their recipients without a hitch.
Why does DMARC fail after implementation?
Technically, DMARC deployment is simple. All you have to do is publish a DNS record with an appropriate DMARC policy. But when you get into the operational aspect of it, you face real challenges.
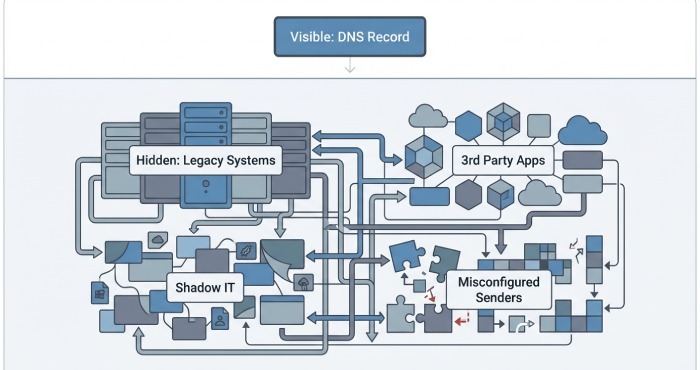
When you implement DMARC, the scope of management goes beyond DNS. The real problem begins when you have multiple systems, applications, and third-party tools sending email on behalf of your domain. Not all of these domains would be active or well-documented; some might be legacy systems that are no longer operational or under anyone’s purview.
These hidden or forgotten senders often remain unnoticed until DMARC monitoring exposes them. At that point, enforcing a stricter policy becomes risky. If even one legitimate sender is missed or misconfigured, important emails can fail, leading to user complaints and loss of confidence in the project.
Add to this the human error factor. While implementing DMARC with a strict policy like “p=reject”, you might successfully block many phishing emails, but you might also end up blocking important legitimate emails, which can quickly outweigh the security gains.
Because of this, many organizations stop at monitoring. Having a v=DMARC1 record feels like the job is done, even though a policy of p=none offers no real protection. DMARC is technically present, but it is not actually doing what it is meant to do.
What most DMARC deployment guides miss out on?
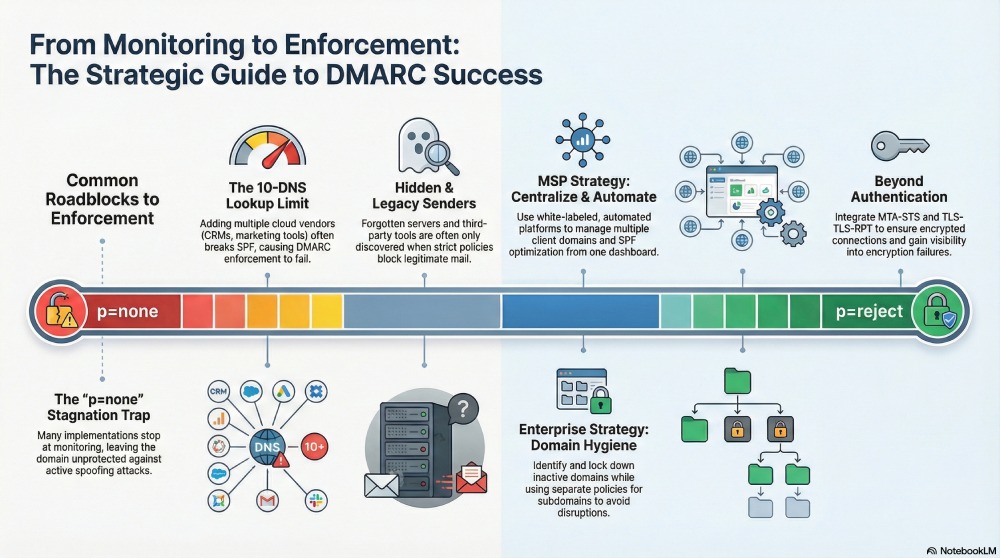
Most DMARC implementation guides take you through the theoretical and technical aspects, but skimp on what actually causes deployments to fail in the real world. Here are a few things that most guides for enterprises and MSPs don’t cover:
Hidden and misconfigured third-party senders
You might have implemented DKIM and SPF properly for your domain, but many third-party senders that send emails on your behalf fail to do so. These issues usually remain hidden until you start DMARC monitoring.
Legacy systems with no clear ownership
You or your client might have older servers, scripts, or internal tools that still send critical emails but aren’t properly authenticated. Since no one actively manages them, they become a major risk when moving to stricter DMARC policies.
The 10-lookup limit of SPF
When you add multiple cloud vendors, like marketing tools, CRMs, and support platforms, you can quickly hit SPF’s 10 DNS-lookup limit. When that happens, SPF fails completely. Since DMARC depends on SPF or DKIM passing, this makes enforcement risky unless you fix the problem.
How should you deploy DMARC as an MSP?
As an MSP, you should not treat DMARC as a one-time security configuration that you implement for your clients. Your clients’ email ecosystem evolves constantly, which means new sending tools are added, old systems remain active, and email authentication can break over time if it is not actively managed.
Opt for centralized oversight
If you have multiple clients, you cannot manage DMARC individually for every domain. You need a centralized operational approach that allows you to monitor all client domains in one place, track sender health and alignment issues, and quickly identify spoofing activity before it becomes a problem.
Reinforce your brand’s authority
DMARC works best when it is offered as a managed service, not something that runs quietly in the background. A white-labeled platform lets you present DMARC under your own brand, share clear, professional reports, and easily demonstrate its value to your clients during reviews.
Automate SPF management
There’s only so much you can do manually, especially if you have multiple domains to monitor. So, automating tasks like SPF optimization, sender validation, and policy progression can help you enforce DMARC safely and efficiently.
How should you deploy DMARC as an enterprise?
If your organization has a complex email ecosystem, DMARC deployment becomes more challenging.
Here’s how you can do it effectively:
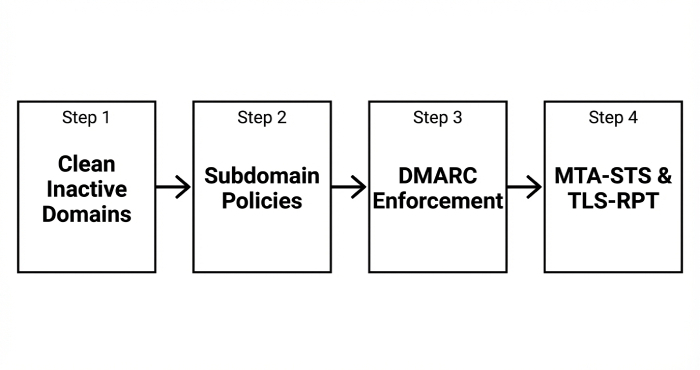
Clean up inactive domains
You might have many unused or inactive domains, especially from past projects or acquisitions, that are no longer used to send emails. Yet they are a lucrative target for attackers. So, make sure you identify such domains and apply strict DMARC policies to block all unauthorized email from them.
Manage subdomains properly
Not every subdomain is ready for strict enforcement at the same time. Some may still rely on marketing or application tools. Use separate subdomain policies so you can protect your main domain without disrupting legitimate email from subdomains.
Go beyond DMARC
DMARC is only one aspect of email security. For comprehensive protection for your email ecosystem, make sure you integrate other email security protocols that strengthen protection beyond authentication alone. These include MTA-STS, which forces encrypted connections for inbound email and prevents downgrade attacks, and TLS-RPT, which gives you visibility into encryption failures so they can be fixed.
Whether you are an organization managing its own email ecosystem or an MSP handling multiple clients at once, DMARC should not be treated as a one-time setup. It is an ongoing process that requires visibility, coordination, and gradual enforcement. If you need help implementing DMARC the right way for your organization or your clients, get in touch with us today!
A progress bar visualization showing the stagnation at p=none versus the goal of p=reject.