Enterprise email security: Here’s what you should know about it
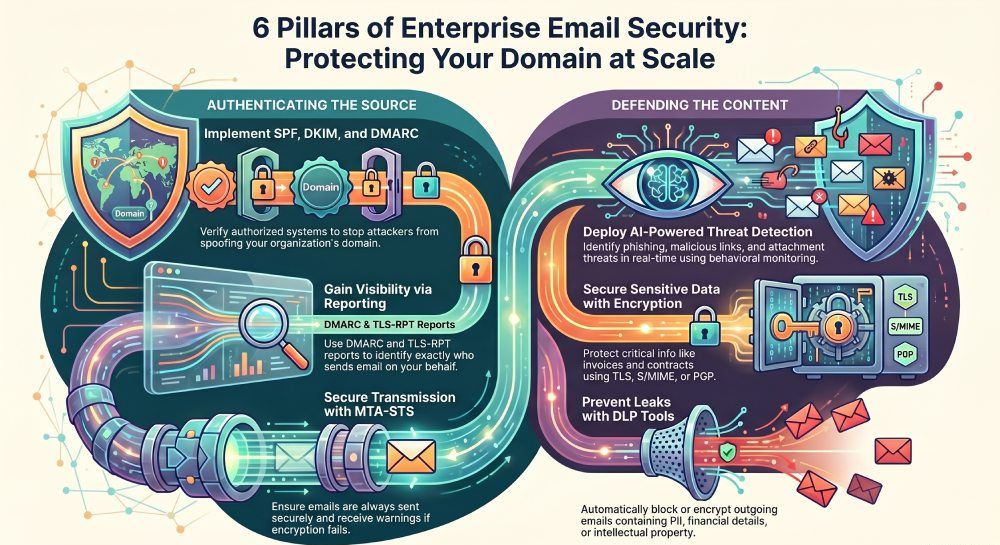
When your organization operates at scale, emails don’t go out from one domain; they are sent from marketing platforms, HR systems, finance tools, third-party vendors, and dozens of individual teams.
With so many systems and tools, it is harder to keep track of who is sending emails on your behalf, whether they are even authorized to do so, and most importantly, whether someone is trying to misuse your domain.
Basic spam filters don’t give you enough visibility into who is sending emails from your domain, which systems are involved, and where the real risks are coming from. For this, you need stronger controls that let you see exactly which platforms are sending emails on your behalf, flag anything unusual, and stop unauthorized senders from using your domain.
Here’s how you can strengthen your enterprise email security and protect your organization from evolving email-based threats.
Build the first line of defence with email authentication
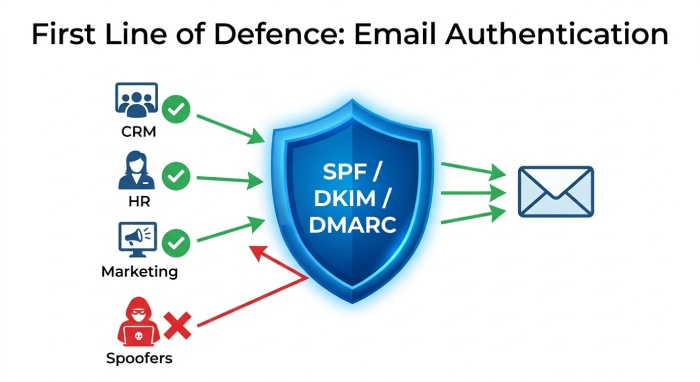
The first step to protecting your enterprise’s email ecosystem is implementing email authentication protocols for your sending domain. These protocols help you verify which systems are allowed to send emails on your behalf and make it harder for attackers to impersonate your organization.
At the enterprise level, it matters more than it seems, because you’re not sending emails from a single system. Your emails are going out from marketing tools, CRM platforms, HR software, finance systems, customer support platforms, and third-party vendors, all using your domain. So, if you don’t authenticate all of these sending sources with SPF, DKIM, and DMARC, you can end up with legitimate emails failing delivery, unauthorized platforms sending emails under your name, or attackers spoofing your domain without you even realizing it.
This is why email authentication protocols should be the first thing you implement. They help you understand who is sending emails on your behalf, block unauthorized senders, and build trust in every email that leaves your domain.
Keep malicious emails out with threat detection
When you have so many people, systems, and vendors sending emails under your name, it becomes very difficult to manually identify which of those emails are actually legitimate and which ones aren’t.
Cybercriminals often exploit complex email ecosystems by sending spoofed or phishing emails that contain fake invoices, malicious links, infected attachments, urgent payment requests, or messages that appear to come from someone in your organization.
This is why you need robust threat detection tools that identify any suspicious behavior, any unusual sending activity, impersonation attempts, and harmful content before those emails reach your recipients.
By robust tools, we mean AI-powered phishing detection, behavioral monitoring, malicious link scanning, attachment sandboxing, and business email compromise detection capabilities that can help you identify suspicious activity in real time.
Secure your content with encryption
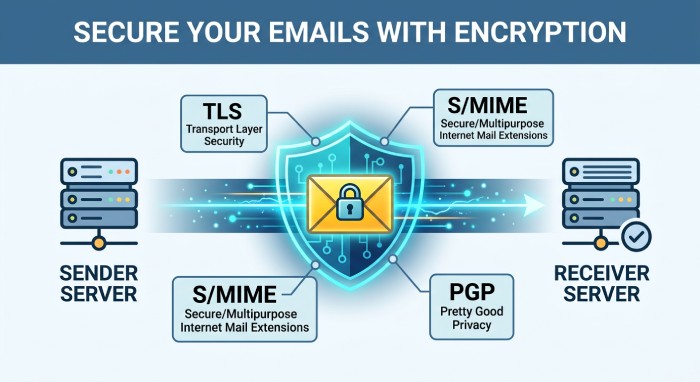
Your emails can be intercepted by attackers while they are being transmitted between mail servers. This becomes problematic when those emails contain critical information such as contracts, invoices, and financial details.
But by encrypting your emails, you can ensure that even if someone intercepts them, they cannot read or change what is inside. Enterprises should protect emails both while they are being sent and while they are stored. TLS helps secure emails during transmission, while S/MIME or PGP can be used for added protection of sensitive emails. MTA-STS and TLS-RPT can also help make sure emails are always sent securely and warn you if something goes wrong.
Prevent sensitive data from leaving your organization
Sometimes, the biggest risk isn’t an external attacker, but your sensitive information being sent through email without the right controls in place. To prevent this from happening, you need Data Loss Prevention (DLP) tools that can monitor outgoing emails and identify when sensitive information is being shared.
These tools can detect personally identifiable information (PII), health records, financial details, intellectual property, etc. They use pattern matching, contextual analysis, and machine learning to identify sensitive content. If something risky is found, they can block the email, automatically encrypt it, alert the security team, or request additional approval before sending it.
Monitor email activity and security reports
You might be putting all the effort into securing your email ecosystem, but if you don’t keep track of what is happening across your domain, all your efforts might go to waste.
As an enterprise, you need visibility into who is sending emails on your behalf, which are failing authentication checks, and whether there is any suspicious activity across the organization.
You can get this information through DMARC reports, audit logs, TLS-RPT reports, and other monitoring tools that show where your emails are coming from, which systems are failing authentication, and whether anyone is trying to misuse your domain.
Although these measures might seem excessive at first, without them, your enterprise might be left dealing with security incidents only after the damage has already been done, which is far more expensive and difficult than preventing them in the first place.
To ensure that your enterprise stays protected against phishing and spoofing attacks while maintaining trust in every email you send, you need a strong security strategy in place. To learn more, contact us today!