A data-driven analysis for security leaders, IT teams, and MSPs — with 20+ primary-source statistics from Microsoft, IBM, FBI IC3, KnowBe4, Verizon, Cisco, and the World Economic Forum.
Introduction: The Typo Was Your Last Line of Defense. It’s Gone.
For years, cybersecurity awareness training taught employees to spot phishing emails by looking for grammatical errors, awkward phrasing, and suspicious formatting. That advice was sound when phishing campaigns were mass-produced by human operators working in a second language. But that era is over.
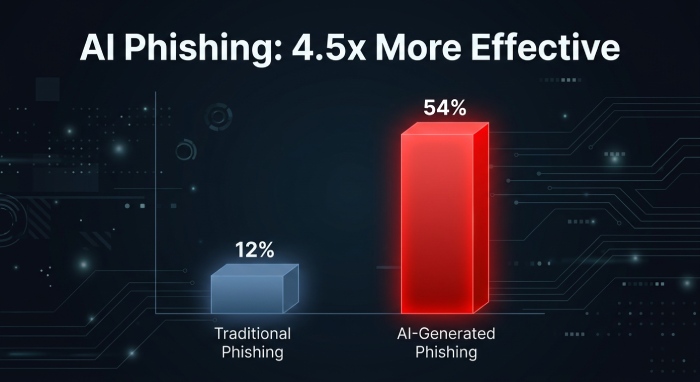
According to the Microsoft Digital Defense Report 2025, AI-generated phishing emails now achieve a 54 percent click-through rate, compared to just 12 percent for manually crafted phishing messages. That means AI-powered phishing is 4.5 times more effective than traditional phishing. Microsoft describes this as the most significant change in phishing in the past year, and estimates that AI can make phishing campaigns up to 50 times more profitable due to higher engagement and automation efficiency.
The KnowBe4 Phishing Threat Trends Report (March 2025) confirms the scale of the transformation: 82.6 percent of all phishing emails analyzed exhibited some use of AI. At least one polymorphic feature was present in 76.4 percent of all phishing campaigns. And 92 percent of polymorphic attacks specifically utilized AI to achieve unprecedented scale.
Meanwhile, the FBI’s 2024 IC3 Annual Report recorded $16.6 billion in total cybercrime losses, a 33 percent increase over 2023. Phishing and spoofing remained the most reported crime type with 193,407 complaints, and business email compromise (BEC) alone cost organizations $2.77 billion.
This article explains what has changed, why traditional email filters are failing, what the data shows, and what organizations should do about it.
1. The Scale of the AI Phishing Explosion
Phishing Volume Is Surging
Between September 2024 and February 2025, the KnowBe4 Phishing Threat Trends Report documented a 17.3 percent increase in phishing emails compared to the previous six months. Ransomware payloads in phishing attacks surged 22.6 percent over the same period, with an accelerating 57.5 percent spike in just the final three months of that window.
The APWG Phishing Activity Trends Report for Q4 2024 recorded between 290,000 and 358,000 unique phishing attacks per month in Q4 2024, with phishing generally declining in the first half of the year before trending sharply upward in the second half.
The Verizon 2025 DBIR found that phishing overtook stolen credentials as the most common initial attack vector, responsible for 16 percent of breaches at an average cost of $4.8 million per breach. Critically, the report also found that employee click rates on phishing simulations were unaffected by training, suggesting that awareness programs alone cannot solve this problem.
AI Is Weaponizing Every Stage of Phishing
The IBM Cost of a Data Breach Report 2025 found that 16 percent of all breaches now involve attacker use of AI, primarily concentrated in phishing (37 percent of AI-assisted breaches) and deepfake impersonation (35 percent). AI-driven phishing is not just about better text. Attackers are using AI to generate personalized messages in the target’s native language, mimic specific writing styles, create multi-variant polymorphic campaigns that evade signature-based detection, and automate the entire attack lifecycle from reconnaissance to payload delivery.
AI-generated phishing emails achieve a 54% click-through rate vs. 12% for manually written ones — making AI phishing 4.5x more effective and up to 50x more profitable. — Microsoft Digital Defense Report 2025
2. Why Traditional Email Filters Are Failing
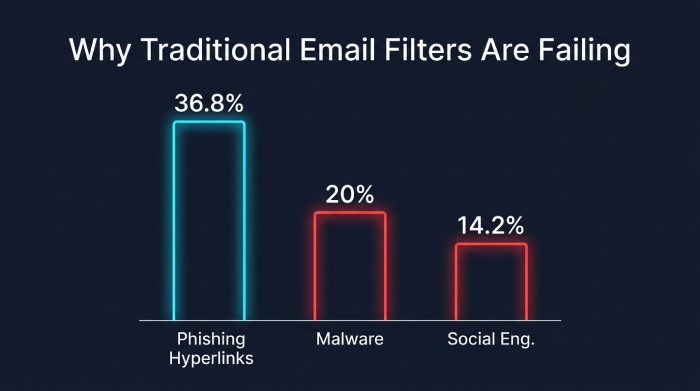
The data on email gateway bypass rates is alarming. The KnowBe4 report found a 47 percent increase in phishing emails evading Microsoft’s native security and secure email gateways (SEGs) in 2024. Three specific payload types experienced significant increases in bypassing detection: phishing hyperlinks (36.8 percent increase), malware (20 percent increase), and social engineering-only attacks (14.2 percent increase).
The Cofense 2024 Annual State of Email Security Report was even more direct: malicious email threats bypassing secure email gateways increased by more than 100 percent in 2023. The report noted that spam filters have evolved into malware detectors but still consistently fail to catch conversational-based phishing attacks like BEC, which rely on social engineering rather than malicious payloads.
Why Legacy Filters Fail Against AI-Crafted Phishing
Traditional email security relies on three core detection methods, all of which AI-generated phishing is designed to defeat:
- Signature-based detection: Compares incoming emails against known malicious patterns. Polymorphic phishing, now present in 76.4 percent of campaigns according to KnowBe4, generates subtle variations in every email that break pattern matching. KnowBe4 estimates that by 2027, the traditional method of grouping phishing emails for pattern-based detection will become virtually impossible.
- Reputation-based filtering: Blocks emails from known bad senders or domains. Attackers now hijack legitimate, trusted domains to send phishing emails. KnowBe4 found that three of the top seven domains used to bypass detection were google.com, sharepoint.com, and dropbox.com. When phishing arrives from a trusted domain, reputation filtering is useless.
- Keyword and heuristic rules: Scans for suspicious language like ‘urgent’ or ‘click here.’ AI-generated phishing uses natural, contextually appropriate language that avoids trigger words. KnowBe4 reported a 22.7 percent increase in the use of technical obfuscation measures including image-based payloads, invisible characters, and left-to-right override techniques to further evade heuristic scanning.
The Microsoft Digital Defense Report 2025 identified a new social engineering technique called ClickFix that has seen widespread adoption. This method tricks users into executing malicious code themselves, completely bypassing traditional phishing protections because the user initiates the action rather than clicking a link or opening an attachment. Microsoft reports that 28 percent of all breaches now begin with phishing or social engineering.
3. The Financial Cost of Getting This Wrong
The financial consequences of phishing failures are staggering and accelerating. The FBI’s 2024 IC3 Report documented $16.6 billion in total cybercrime losses, with cyber-enabled fraud, including phishing, spoofing, BEC, and tech support scams, accounting for nearly 83 percent of all losses at $13.7 billion. BEC alone generated $2.77 billion in losses across 21,442 reported incidents, and BEC losses have totaled nearly $8.5 billion over the past three years.
The IBM Cost of a Data Breach Report 2025 found that phishing-initiated breaches cost an average of $4.8 million each. Shadow AI, the unsanctioned use of AI tools by employees that can expose sensitive data to phishing and social engineering, added $670,000 to average breach costs and was a contributing factor in 20 percent of breaches.
The WEF Global Cybersecurity Outlook 2026 underscores the human scale of the problem: 73 percent of respondents reported that they or someone in their network had been personally affected by cyber-enabled fraud in 2025. Phishing, vishing, and smishing were the most common vector at 62 percent. CEOs now rate cyber-enabled fraud as their number one concern, surpassing ransomware for the first time.
4. What Actually Works: Building a Multi-Layered Email Defense
If traditional filters are insufficient on their own, what does an effective defense look like in 2026? The data points to a multi-layered approach that combines gateway-level protection, real-time link analysis, email authentication protocols, and AI-powered behavioral detection.
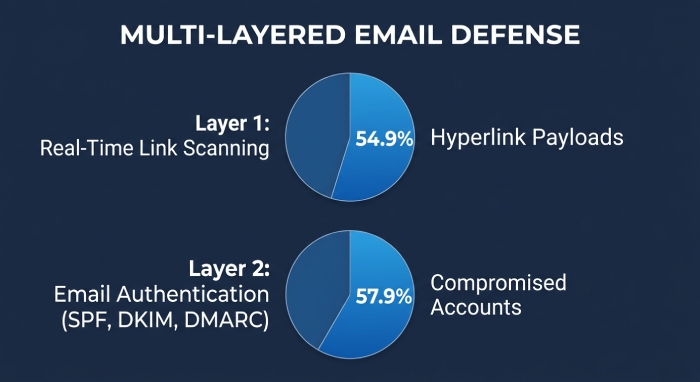
Layer 1: Advanced Gateway Filtering with Real-Time Link Scanning
Static URL blocklists are failing because attackers use legitimate domains and time-delayed redirects to bypass them. KnowBe4 found that 54.9 percent of phishing emails contained a hyperlink payload, making real-time link scanning at the moment of click, not just at delivery, essential. Cloud-based email security solutions that rewrite URLs and check them against reputation databases in real time at the moment of user interaction provide protection that static filters cannot. This is exactly the approach used by advanced threat defense platforms that inspect links both at delivery and at click time.
Layer 2: Email Authentication — SPF, DKIM, and DMARC
The APWG Phishing Activity Trends Report found that 57.9 percent of phishing emails were sent from compromised accounts. The CISA phishing guidance specifically recommends implementing DMARC as a critical control for reducing phishing susceptibility. Email authentication protocols like SPF, DKIM, and DMARC prevent attackers from spoofing your domain to send phishing emails to your customers and partners. Without DMARC enforcement, anyone can send emails that appear to come from your domain, damaging your brand and enabling fraud. SPF record management is particularly important for organizations using multiple email services, where exceeding the 10-lookup limit can silently break authentication and leave domains vulnerable.
Layer 3: AI-Powered Behavioral Detection
Since AI-generated phishing defeats pattern matching, the defense must also be AI-powered. The Microsoft Digital Defense Report 2025 found that phishing-resistant multi-factor authentication blocks over 99 percent of unauthorized access attempts. Behavioral detection systems analyze sender patterns, communication context, tone anomalies, and login behavior to identify suspicious activity that signature-based systems miss entirely. The Cisco 2025 Cybersecurity Readiness Index reinforces the urgency: 60 percent of IT teams cannot see what employees are doing with GenAI tools, creating shadow AI blind spots that behavioral detection can help close.
Layer 4: Human Risk Management
The Verizon DBIR 2025 found that employee phishing click rates remain stubbornly unaffected by training. But this does not mean training is useless; it means training must evolve. Instead of teaching employees to spot typos that no longer exist, modern security awareness programs should focus on verification behaviors: confirming requests through a second channel, questioning urgency, and reporting anything suspicious. The Accenture State of Cybersecurity Resilience 2025 found that only 34 percent of organizations have a mature cyber strategy, and 77 percent lack the ability to defend against AI-enabled threats. Closing that maturity gap starts with people.
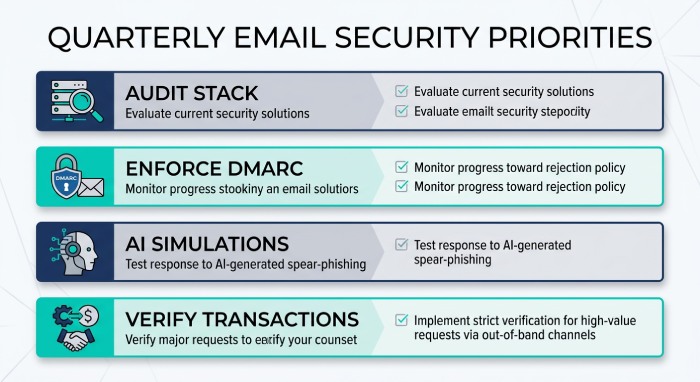
5. Practical Next Steps: What to Do This Quarter
- Audit your current email security stack. If your organization relies solely on Microsoft’s native protection or a standalone SEG, you are exposed. The KnowBe4 data shows a 47 percent increase in attacks bypassing these tools. Add a layered cloud email security solution that provides real-time link checking and behavioral analysis.
- Implement DMARC at enforcement (p=quarantine or p=reject). If your domain does not have a DMARC policy at enforcement level, attackers can impersonate your organization to phish your customers. Use SPF flattening tools to manage complex records without breaking authentication.
- Deploy real-time URL rewriting and click-time link scanning. Static blocklists cannot keep up with polymorphic campaigns. Ensure every link in every email is rewritten and checked at the moment of click, not just at delivery.
- Run an AI-specific phishing simulation. Test your employees with AI-generated phishing emails that are grammatically flawless and contextually personalized. If your current simulation vendor still uses obvious red flags, you are testing for yesterday’s threat.
- Establish multi-channel verification for all financial transactions. No wire transfer, invoice payment change, or credential reset should proceed based on email alone. The FBI IC3 data shows BEC costs $2.77 billion annually, and these losses are almost entirely preventable with out-of-band confirmation.
- Monitor for shadow AI data leakage. With 60 percent of IT teams blind to employee GenAI usage (Cisco 2025), outbound email scanning and DLP at the SMTP gateway level can serve as a safety net to catch sensitive data being exfiltrated through AI tool interactions.
Conclusion: The Filter Alone Cannot Save You
The phishing landscape of 2026 bears almost no resemblance to the threat of even two years ago. AI has eliminated the grammatical errors, the awkward formatting, and the suspicious sender addresses that employees were trained to spot. Polymorphic campaigns ensure that no two phishing emails look the same, defeating pattern-based detection. Attackers hijack trusted domains like Google and SharePoint to sail through reputation filters. And social engineering techniques like ClickFix bypass email scanning entirely by manipulating the user into executing malicious code themselves.
The data is unequivocal: traditional email filters are a necessary but no longer sufficient defense. Organizations need a multi-layered approach that combines advanced gateway filtering, real-time link scanning, email authentication (SPF, DKIM, DMARC), AI-powered behavioral detection, and evolved human risk management.
The good news is that these defenses work. Microsoft’s data shows phishing-resistant MFA blocks 99 percent of unauthorized access attempts. IBM’s data shows AI-powered security tools save organizations $1.9 million per breach. And the growing refusal to pay ransoms (64 percent of victims in 2025) demonstrates that organizations that invest in resilience and recovery can change the economics of cybercrime.
The question is not whether your organization will be targeted by AI-generated phishing. It already has been. The question is whether your defenses have evolved as fast as the attack.