Organizations that send large volumes of emails, including software-as-a-service (SaaS) platforms, marketing automation providers, email service providers (ESPs), and major corporations, operate in an environment where deliverability, trust, and security are essential. At the forefront of email authentication is DomainKeys Identified Mail (DKIM), which is vital for confirming that outgoing emails are secure, intact, and consistent with the sender’s identity.
However, for those dispatching millions or even billions of emails daily, a standard DKIM implementation falls short. It’s essential to develop a tailored DKIM framework — one that is scalable, secure, adaptable, and in harmony with your existing infrastructure and organizational objectives.
This guide will walk you through the process of building such a framework from the ground up.
What is DKIM and Why It Matters at Scale
DKIM (DomainKeys Identified Mail) is a technique for authenticating emails, employing cryptographic signatures to confirm that a message remains unchanged in transit and that it has the domain owner’s permission.
For those who send a large volume of emails, DKIM is critical for several reasons:
- It fosters trust with email service providers such as Gmail, Outlook, and Yahoo.
- It safeguards your domain against spoofing and phishing attacks.
- It enhances the likelihood that your emails will land in the inbox.
- It ensures compliance with DMARC protocols.
However, when managing high volumes, DKIM evolves beyond merely a DNS entry and a signature; it presents a significant design challenge for your system.
Core Challenges in High-Volume DKIM Deployment
Before you begin structuring your architecture, it’s crucial to recognize common challenges:
- Complexity of Key Management
Handling numerous DKIM keys across various domains, subdomains, and clients can be quite daunting.
- DNS Constraints
Regularly rotating keys and having multiple selectors can inflate DNS records and lead to lookup issues.
- Requirements for Multi-Tenancy
For ESPs or SaaS platforms, it’s essential to facilitate DKIM signing for numerous clients, each with distinct domains.
- Impact on Performance
DKIM signing for every email can tax CPU resources, particularly during high-volume periods.
- Risks to Security
Improper management of keys can risk the exposure of private keys, resulting in spoofing or misuse of the domain.
Key Components of a Custom DKIM Architecture
A strong DKIM setup for senders with significant output usually comprises these elements:
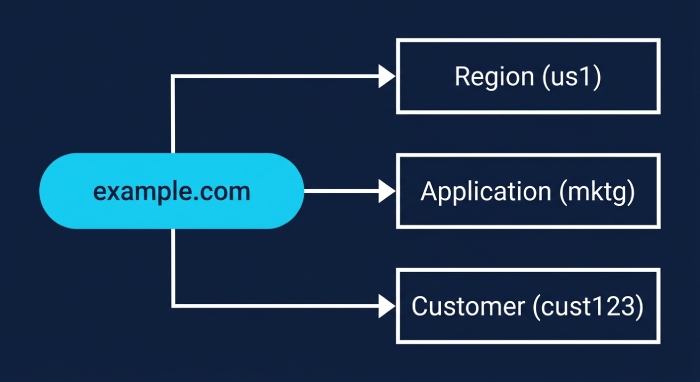
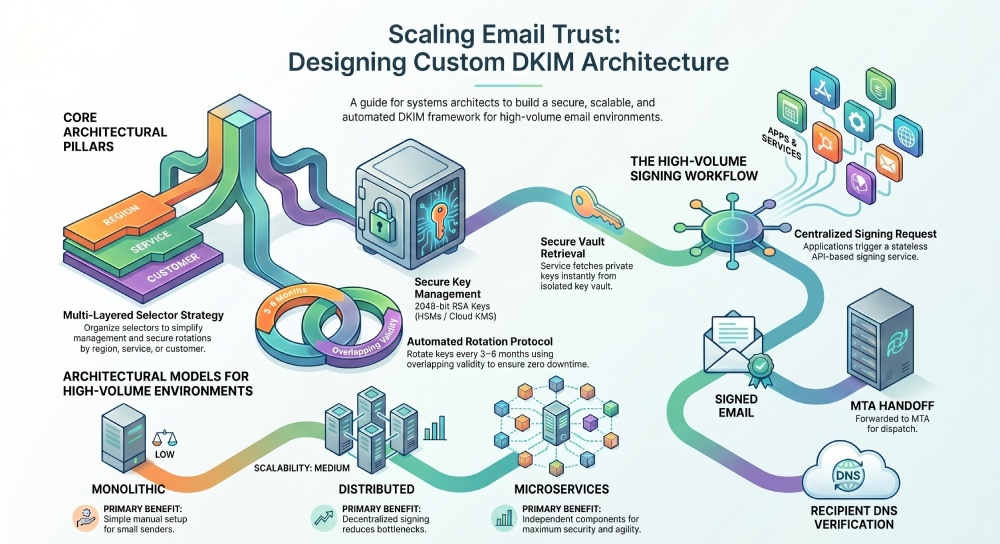
1. Selector Approach
A selector is a string that helps find the DKIM public key in DNS. For systems handling high volumes, it is advisable to:
- Utilize several selectors for each domain
- Organize selectors by:
- Region (e.g., us1, eu1)
- Application or service
- Customer (applicable for multi-tenant scenarios)
For instance:
- selector1._domainkey.example.com
- mktg._domainkey.example.com
- cust123._domainkey.example.com
This organization enhances ease of management and allows for secure key updates.
2. Key Generation and Storage
Recommended Approaches:
- Implement RSA keys with a minimum size of 2048 bits, as this is the current standard.
- Create keys using trusted cryptographic libraries for enhanced security.
Keep private keys protected within:
- Hardware Security Modules (HSMs)
- Secure key management systems (such as cloud KMS)
- Avoid embedding keys directly into application source code.
Additional Suggestion:
If applicable, evaluate the use of elliptic curve cryptography (ECC) to achieve improved performance and reduced key sizes.
3. DNS Configuration Strategy
Every selector is linked to a DNS TXT record that holds the public key. For instance: selector1._domainkey.example.com IN TXT “v=DKIM1; k=rsa; p=MIIBIjANBgkqh…”
Suggestions for Implementation:
- Utilize APIs for automated DNS setup.
- Conduct validation tests for:
- Record propagation
- Correctness of syntax
- Limit the length of TXT records; refrain from splitting them into multiple strings unless absolutely needed.
4. Signing Infrastructure
This is the stage at which emails receive their signatures prior to dispatch.
Options include:
- Signing at the MTA level (like Postfix using OpenDKIM)
- Signing at the application level (integrated within your email service)
- A specialized signing service (utilizing a microservice architecture)
Suggested Method:
- For systems with high traffic, a centralized signing service is most effective:
- Operates as a stateless API-based solution
- Securely retrieves keys
- Signs emails instantly
- Easily scales horizontally
5. Multi-Tenant DKIM Support
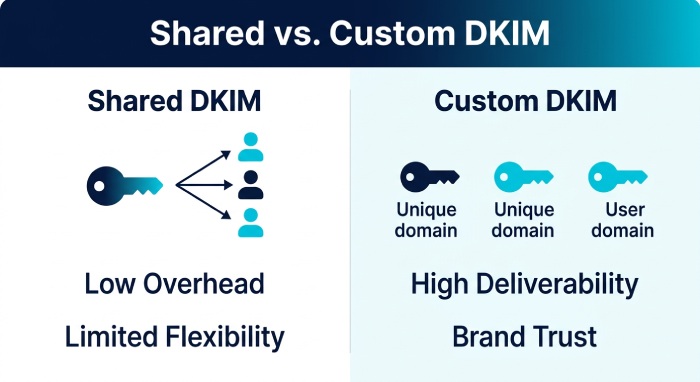
When supporting multiple customers, implementing multi-tenant DKIM becomes an important architectural decision. One common approach is using a shared DKIM setup, where a single domain signs emails on behalf of all customers. This method is simpler to manage and reduces operational overhead, but it limits flexibility and may impact brand identity and deliverability for individual clients.
A more effective approach is to provide custom DKIM for each customer, allowing them to send emails using their own domains and unique cryptographic keys. While this requires a more advanced setup—including a streamlined onboarding process, DNS validation mechanisms, and automated key provisioning—it significantly improves deliverability, strengthens brand trust, and gives customers greater control over their email authentication.
6. Key Rotation Mechanism
- Key Rotation Protocol
- Ensuring security through key rotation is crucial.
Approach:
- Change keys every 3 to 6 months.
Ensure overlapping validity:
- The previous selector stays active while the new one is brought in.
- Gradually decommission old keys once verified.
Automation:
- Plan for automated key creation.
- Update DNS entries automatically.
- Transition to the new signing selector without disruption.
7. Monitoring and Validation
- At scale, visibility is essential. You should continuously monitor DKIM pass/fail rates, signature verification errors, DNS lookup issues, and how keys are being used.
- To support this, rely on DMARC aggregate reports, log analysis systems, and real-time dashboards to quickly detect and troubleshoot any authentication problems.
8. Integration with SPF and DMARC
DKIM doesn’t work alone—it should align with your From domain for DMARC compliance, while both SPF and DKIM must pass authentication checks.
Start your DMARC policy with p=none to monitor results, then gradually move to p=quarantine and p=reject as your DKIM setup becomes stable and reliable.
Architectural Models for High-Volume Senders
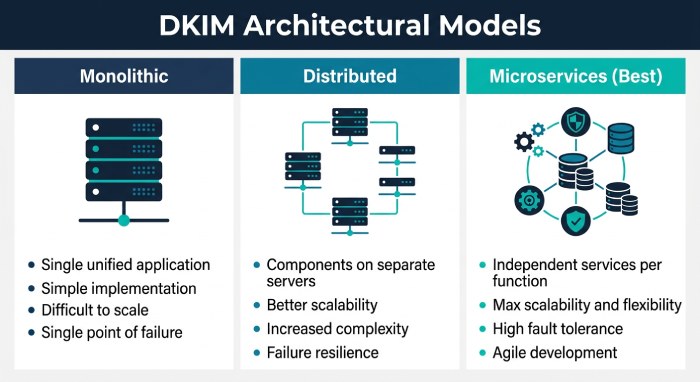
Monolithic DKIM Setup (Not Recommended at Scale)
- A monolithic DKIM setup relies on a single selector with static keys and manual DNS updates, making it simple but rigid. This approach may work for small senders, but it quickly becomes inefficient as email volume grows.
- The biggest drawback is the lack of scalability and flexibility. A single point of failure increases risk—especially if a key is compromised—and managing updates manually becomes time-consuming and error-prone at scale.
Distributed DKIM Architecture
- A distributed DKIM architecture spreads signing responsibilities across multiple selectors, services, or regions. By decentralizing key usage, it enables different systems to handle signing independently while maintaining consistency.
- This model improves performance and reliability by distributing load and reducing bottlenecks. It also enhances fault tolerance, ensuring that if one node fails, others can continue signing without disruption.
Microservices-Based DKIM Architecture (Best Practice)
- A microservices-based DKIM architecture breaks the system into specialized components such as a Key Management Service, Signing API, DNS automation, and monitoring layers. Each service operates independently but works together as part of a cohesive system.
- This design allows for easy scaling, faster updates, and stronger security boundaries. It simplifies maintenance and enables teams to improve or replace individual components without affecting the entire email infrastructure.
Performance Optimization Techniques
To enhance the efficiency of high-volume systems, it is essential to prioritize speed:
- Public Key Caching
Eliminate redundancy in DNS lookups during validation checks.
- Signing Services Load Balancing
Evenly distribute the signing workload among various nodes.
- Batch Signing
Process emails in groups when feasible, based on system design.
- Asynchronous Signing Workflows
Separate the email creation process from the signing to minimize delays.
Example Workflow of a Custom DKIM System
- An application creates an email.
- A request is made to the DKIM signing service.
- The service accesses a secure vault to obtain the private key. The email is then signed using the correct selector.
- This signed email is forwarded to the Mail Transfer Agent (MTA).
- The recipient’s server obtains the public key from DNS to verify the DKIM signature.
Future-Proofing Your DKIM Architecture
To ensure your DKIM framework remains relevant, it’s essential to create it in a way that adapts to shifting email standards. With advancements like BIMI becoming more prevalent, heightened cryptographic demands, and an increasing emphasis on domain reputation, your DKIM configuration needs to be both adaptable and robust.
Emphasize a modular, API-centric structure that prioritizes automation. This strategy allows for straightforward key updates, quick adjustments to new protocols, and efficient scaling, all while maintaining the stability of your email system.
Conclusion
Designing a custom DKIM architecture for high-volume email sending is not just a technical necessity—it’s a strategic investment in deliverability, security, and brand reputation.
A well-designed system should be:
- Scalable to handle massive throughput
- Secure to protect domain integrity
- Flexible to support multiple tenants and use cases
- Automated to reduce operational overhead
By implementing a robust selector strategy, secure key management, automated DNS handling, and a scalable signing infrastructure, you can build a DKIM architecture that strengthens your overall email security posture—ready not just for today’s demands but for tomorrow’s evolving threats.
At scale, DKIM isn’t just a checkbox—it becomes a critical component of your core email security infrastructure. Designing it correctly from the outset makes a measurable difference in deliverability, trust, and long-term resilience.