Microsoft Office Malware, Cooler Master Breach, 911 Botnet Dismantled – Cybersecurity News [May 27, 2024]
Here we are back again with the latest cybersecurity news around the world covering the malware posing as Microsoft Office on torrent websites, the Cooler Master data breach, the takedown of 911 S5 botnet, YouTube causing trouble for ad blockers, and the arrest of an Indian man for creating a fake Coinbase website and stealing crypto. Stay tuned!
Unauthorized Microsoft Office Installs Bring a Mix of Malware to Systems
Threat actors have been distributing malware via pirated versions of Microsoft Office on torrent websites.
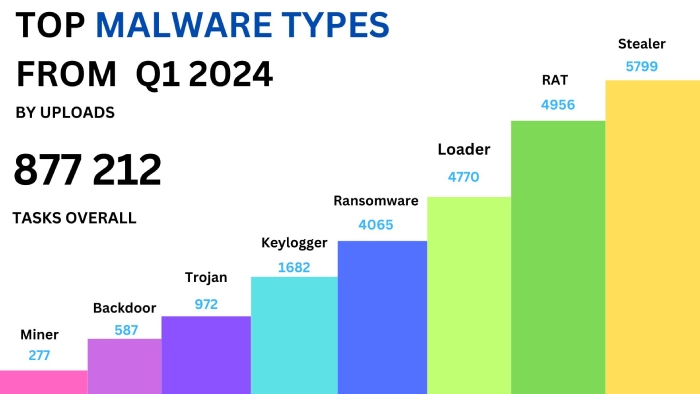
The malware is extremely capable and contains RATs (Remote Access Trojans), crypto miners, proxy tools, and much more. They were first noticed by AhnLab’s Security Intelligence Center, which shared details about the threat actors using multiple lures for Microsoft Office and Windows OS.
The installer of Microsoft Office has an interface mimicking the original and also lets you select the language and the bit variant of the OS. While the window is open, the installer launches a .NET malware that connects to a Telegram channel to receive download URLs (Uniform Resource Locators) pointing to Google Drive or GitHub. From here, the PowerShell introduces multiple malware strains to the victim’s systems that are unpacked using 7Zip.
The campaign is ongoing and is known for downloading Orcus RAT, XMRig, 3Proxy, PureCrypter, and AntiAV malware. Even if you discover or remove any of these, the updater will redownload it to your system upon launch.
It’s best to stick to official channels if you want to download files. But if you do have to install files from different sources, make sure you trust the channel to maintain your malware protection or avoid pirated software altogether.
Cooler Master Announces Data Breach, Customer Info Compromised
This week, the computer hardware manufacturing enterprise Cooler Master confirmed a data breach that happened on 19 May 2024.
During the breach, a threat actor known as Ghostr hacked into the organization’s website and made away with linked databases. The Cooler Master Fanzone website that was breached is used to register product warranties and open support tickets, and it needs the personal information of the customers.
The threat actor says that they were able to steal 103GB of data, including information of nearly half a million customers. The potential information that is at risk includes names, emails, residential addresses, birth dates, and phone numbers of the customers. There are also other samples that include information about products, employees, emails with vendors, and partial credit card data.
The organization says they promptly alerted the authorities and has also hired security experts to address the situation. If you are an affected customer, Cooler Master will send you an email and advise you about the next steps you have to take to make sure that your data is safe.
The size of the data sample is substantial, so there’s a high chance that it could be sold to other threat actors in dark web marketplaces. If you are a Cooler Master user, it’s best to keep an eye out for phishing emails and other social engineering attacks.
US Takes Down 911 S5 Botnet Used for Cyberattacks, Arrests Organizer
The U.S. Justice Department took down and dismantled the 911 S5 proxy botnet with the help of international partners and has arrested the portal’s administrator.
The FBI conducted a joint cyber operation to dismantle the world’s largest botnet ever and arrested its administrator, a Chinese national—Yunhe Wang. They seized infrastructure and assets and levied sanctions. Wang and his conspirators have been pushing malware using multiple malicious VPNs (Virtual Proxy Networks) since 2011 and added all compromised devices to the 911 S5 residential proxy.
You can check if you are a victim of the malware here and take the steps to get rid of it. Between 2014 and 2022, the threat actor created a network of 19 million unique IP addresses worldwide. The threat actors lured potential victims by offering free VPN services to install the proxy malware.
Now that it is finally dismantled, the Justice Department is serving seizure warrants for multiple domains that were used by the threat actor-network. Wang made a profit of $99 million by selling access to IP addresses to threat actors who misused the networks for malicious purposes.
The U.S. Treasury Department arrested Wang (the boss), Jingping Liu (the money launderer), and Yanni Zheng (who had the power of attorney for Yunhe Wang), along with three organizations that were owned by Wang. He faces a maximum penalty of up to 65 years in prison if convicted on all accounts.
Ad Blocker Users Report YouTube Videos Skipping to the End
Many people from around the world have been reporting that the YouTube videos they play using an ad blocker skip to the end directly.
The issue began this week and is not impacting everyone at the moment, but it does affect all YT videos. The behavior is persistent even if you try to reload the same video or click on the beginning of the video to watch it again. You can only fix this by getting rid of the ad blocker.
The issue was first reported by 9to5Google, and as it came to Google’s attention, they started cracking down on the use of ad blockers on YouTube. They have still not made it clear if the issue is an intentional move by them or an issue with third-party ad blocker applications. However, YouTube recently announced that using ad blockers violates its terms of service, and it will soon start taking action against this.
People have found ways to fix it though! Some folks switched their ad blocker to one called uBlock Origin, while others tried watching in incognito mode or signing out of YouTube. There’s also a web browser called Brave that seems to block ads without causing the videos to skip.
Indian Man Defrauds $37 Million in Crypto Through Counterfeit Coinbase Pro Site
In other news, an Indian national pleaded guilty to a wire fraud conspiracy where he stole nearly $37 million via a fake Coinbase website that stole login credentials. This case highlights the importance of phishing protection to prevent such scams.
The Indian, Chirag Tomar, was arrested at the Atlanta airport in December last year and was under investigation by the U.S. Secret Service and the FBI. Tomar and his accomplices made a fake Coinbase website that mimicked the Coinbase Pro portal in 2021 using the domain “Coinbasepro[.]com“.
The site tricked the customers of the official portal into entering their login details and 2FA codes. It was eventually shut down in November 2022, and all of its functionality was then integrated into the official Coinbase platform. Tomar also made phishing Coinbase accounts, took control of crypto wallets, and transferred funds into wallets that were under his control.
He also used social engineering tactics and leveraged a fake login error that encouraged the users to call Coinbase representatives, who were also fake and duped the victims into installing RATs on their devices. The fraudster could go to prison for up to 20 years and be fined $250,000.