A data-driven analysis with 20+ statistics from EasyDMARC, Google, Microsoft, IBM, Verizon, CISA, and the PCI Security Standards Council.
Introduction: The Line Between Best Practice and Requirement Has Been Erased
For over a decade, email authentication protocols — SPF, DKIM, and DMARC — were recommended best practices. Security experts encouraged organizations to implement them. Industry frameworks suggested them. But compliance was voluntary, and enforcement was inconsistent.
That era is over. In 2026, email authentication is a mandatory requirement enforced by the three largest email providers on earth, embedded in global payment card security standards, and integrated into sweeping cybersecurity regulations across multiple jurisdictions. Organizations without DMARC at enforcement level now face rejected emails, regulatory fines, payment processing restrictions, and increased breach exposure.
The EasyDMARC 2026 DMARC Adoption Report found that global DMARC adoption has reached 52.1 percent of the top 1.8 million domains, up from 47.7 percent in 2025 and 27.2 percent in 2023. But here is the critical gap: of the 937,931 domains with valid DMARC records, 525,996 — more than half — remain stuck at p=none, the monitoring-only policy that provides zero protection against spoofing. They have installed the alarm system but left it in test mode.
This article explains the regulatory forces that have made email authentication mandatory, the data on current adoption and enforcement gaps, the specific risks of non-compliance, and the practical steps organizations need to take to move from monitoring to enforcement.
1. The Three Regulatory Forces That Changed Everything
Force 1: Google, Yahoo, and Microsoft’s Sender Requirements
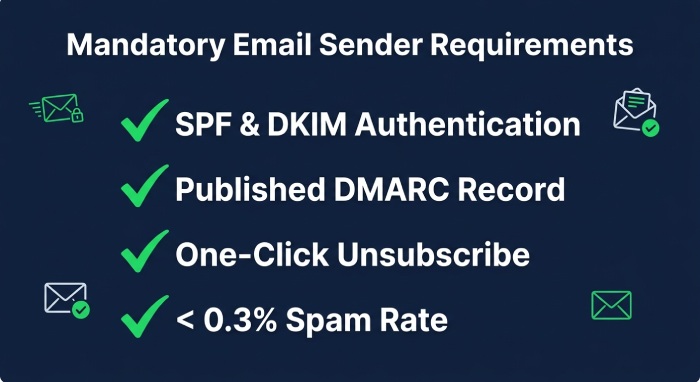
In February 2024, Google and Yahoo introduced mandatory email authentication requirements for bulk senders (those sending more than 5,000 emails per day). The requirements include SPF and DKIM authentication on all outgoing email, a published DMARC record with at least p=none, SPF or DKIM alignment with the From domain, one-click unsubscribe capability, and spam complaint rates below 0.3 percent.
As of November 2025, Google tightened enforcement significantly: non-compliant emails now face temporary and permanent rejections at the SMTP level. Microsoft’s Outlook followed with its own sender requirements starting May 5, 2025, mandating SPF, DKIM, and DMARC alignment for domains sending over 5,000 emails per day. Non-compliant messages are now routed to junk or rejected outright.
The practical consequence is straightforward: if your domain does not have properly configured SPF, DKIM, and DMARC, your emails to Gmail, Yahoo, and Outlook recipients — collectively representing the vast majority of email inboxes worldwide — may not be delivered at all.
Force 2: PCI DSS v4.0 Anti-Phishing Requirements
The Payment Card Industry Data Security Standard version 4.0 introduced a requirement (10.4.1.1) that became mandatory in 2025 and is actively enforced in 2026. It requires organizations handling credit card data to implement anti-phishing mechanisms, which specifically includes DMARC. According to Mimecast’s PCI DSS DMARC analysis, failure to comply with PCI DSS can result in fines ranging from $5,000 to $100,000 per month and, in the worst case, loss of the ability to process credit card payments entirely.
For any organization that processes, stores, or transmits cardholder data, DMARC is no longer a security recommendation. It is a compliance obligation with direct financial penalties for non-compliance.
Force 3: NIS2, DORA, and the Global Regulatory Wave
The European Union’s NIS2 Directive, which covers 18 sectors including banking, energy, healthcare, and digital infrastructure, requires organizations to implement cybersecurity risk management measures that specifically include email security and incident prevention controls. The ENISA Technical Implementation Guidance on NIS2 provides granular guidance on implementation, and email authentication is a recognized component of meeting these requirements.
The Digital Operational Resilience Act (DORA) imposes ICT risk management and incident reporting requirements on the EU’s 22,000 financial entities. The IBM Cost of a Data Breach Report 2025 found that U.S. breach costs surged 9 percent to $10.22 million, driven specifically by higher regulatory fines and detection costs. The message from regulators globally is clear: organizations that fail to implement basic email security controls will pay more when breaches occur.
The CISA phishing infographic specifically recommends DMARC as a cross-sector cybersecurity performance goal, reflecting the U.S. government’s position that email authentication is a foundational security requirement for all organizations.
DMARC adoption grew from 27.2% to 52.1% between 2023 and 2026 — but more than half of DMARC-enabled domains remain at p=none, offering zero spoofing protection. — EasyDMARC 2026 DMARC Adoption Report
2. The Adoption Data: Where Organizations Stand Today
Global Adoption Is Growing, But Enforcement Lags Dangerously Behind
The EasyDMARC 2025 DMARC Adoption Report, which examined the top 1.8 million domains worldwide plus the Fortune 500 and Inc. 5000, found that DMARC adoption surged from 27.2 percent to 47.7 percent between 2023 and 2025, a 75 percent increase. Enforcement policies (quarantine plus reject) grew by 50 percent during this period. The 2026 update shows continued growth to 52.1 percent adoption and 411,935 domains at enforcement level, up from 233,249 in 2023.
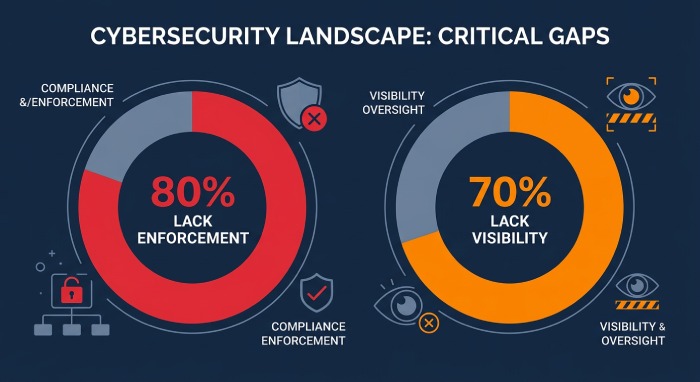
However, over 80 percent of domains globally still have no DMARC record at all or use a non-enforcing policy (p=none). More than 70 percent of DMARC-enabled domains lack reporting (RUA) tags, meaning they have no visibility into who is sending email on their behalf.
The Enterprise vs. SMB Divide
The gap between large enterprises and smaller organizations is stark. According to the EasyDMARC Fortune 500 vs. Inc. 5000 analysis:
- Fortune 500: 95 percent adoption, over 80 percent at enforcement level (quarantine or reject), 62.7 percent at the strictest p=reject policy, and 97.9 percent using RUA reporting.
- Inc. 5000: 76.2 percent adoption, only 15.2 percent at p=reject, and more than half stuck at the monitoring-only p=none policy. Only 67.4 percent use RUA reporting.
The Inc. 5000 still outperforms the global average (where fewer than 20 percent achieve enforcement), but the gap with the Fortune 500 represents a measurable security risk. This is precisely the segment most targeted by attackers: the Verizon 2025 DBIR found that ransomware appeared in 88 percent of SMB breaches and that SMBs are targeted nearly four times more frequently than large organizations.
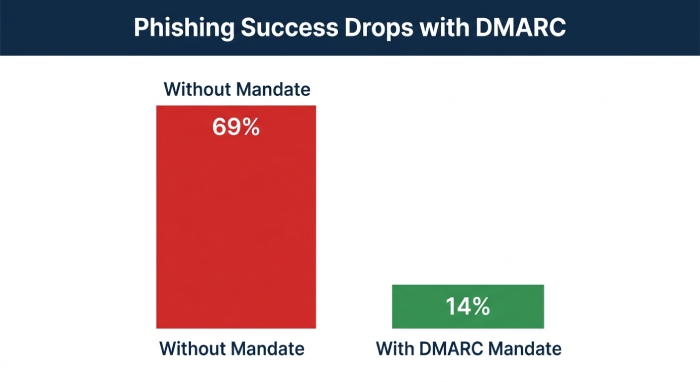
Countries With Mandatory DMARC See Measurably Less Phishing
One of the most compelling findings in the EasyDMARC 2025 report is the direct correlation between national DMARC mandates and phishing outcomes. The United States, which has government DMARC mandates (BOD 18-01 for federal agencies), saw successful phishing email delivery drop from 69 percent to 14 percent. By contrast, the Netherlands, which lacks enforcement mandates, saw phishing vulnerability increase to 97 percent. This data demonstrates that DMARC enforcement is not merely a theoretical protection. It produces measurable, dramatic reductions in phishing success rates at the national level.
3. What Happens When You Don’t Comply
The consequences of non-compliance now span four categories, each with direct financial and operational impact:
- Email deliverability failure. Without DMARC, your marketing emails, transactional notifications, invoices, and customer communications may be rejected by Gmail, Yahoo, and Outlook. For businesses that depend on email for revenue, this is an existential threat to communication.
- Regulatory fines. PCI DSS non-compliance can result in fines of $5,000 to $100,000 per month. NIS2 violations can result in fines up to €10 million or 2 percent of global annual revenue, whichever is higher. DORA non-compliance exposes financial entities to supervisory sanctions.
- Increased breach costs. The IBM Cost of a Data Breach Report 2025 found that phishing-initiated breaches cost an average of $4.8 million each. BEC losses reached $2.77 billion in 2024 according to the FBI IC3. Organizations without email authentication are more vulnerable to both attack vectors.
- Brand and domain spoofing. Without DMARC at enforcement, anyone can send emails that appear to come from your domain. The KnowBe4 Phishing Threat Trends Report found that 57.9 percent of phishing emails were sent from compromised or spoofed accounts. If your domain is being spoofed to phish your customers, your brand reputation and customer trust are directly at risk.
4. The SPF Challenge: Why Implementation Is Harder Than It Sounds
DMARC requires both SPF and DKIM to function correctly. While DKIM is typically configured once per sending service, SPF presents a unique and persistent challenge: the 10 DNS lookup limit.
SPF records specify which servers are authorized to send email on behalf of your domain. Every third-party service you use for email — your CRM, marketing automation platform, helpdesk, billing system, and transactional email service — adds entries to your SPF record. Each ‘include’ statement triggers a DNS lookup, and the SPF specification limits total lookups to 10. When an organization exceeds this limit, SPF authentication silently fails, and DMARC alignment breaks. The result is that legitimate emails may be rejected or sent to spam, even though the organization believes its authentication is configured correctly.
This is a particularly acute problem for growing organizations that continuously add new SaaS tools and email-sending services. SPF flattening solves this by converting nested DNS lookups into direct IP addresses, keeping the record functional regardless of how many services are included. SPF flattening tools automatically monitor for changes in the underlying IP ranges and update records dynamically, preventing the silent authentication failures that can undermine an entire DMARC deployment.
5. From Monitoring to Enforcement: A Practical Roadmap
Moving from p=none to p=reject is the single most impactful step an organization can take for email security. Here is a phased approach:
Phase 1: Deploy and Monitor (p=none)
- Publish a DMARC record at p=none with RUA reporting enabled. This provides visibility into all email sources sending as your domain without affecting delivery. Use a DMARC reporting tool to analyze aggregate reports and identify legitimate senders, unauthorized senders, and authentication failures.
- Configure SPF and DKIM for all legitimate sending services. Audit every third-party service that sends email on your behalf and ensure each is included in your SPF record and has DKIM configured. Use SPF flattening if you are approaching or exceeding the 10-lookup limit.
Phase 2: Tighten (p=quarantine)
- Once your DMARC reports show that all legitimate email sources pass authentication, move to p=quarantine. This directs receiving servers to send emails that fail DMARC to the spam folder rather than the inbox. Monitor for any legitimate email that is incorrectly quarantined and adjust SPF/DKIM records as needed.
Phase 3: Enforce (p=reject)
- Move to p=reject when you are confident that all legitimate email passes authentication. This is the only policy that provides full protection against domain spoofing. Emails that fail DMARC will be rejected entirely, preventing spoofed messages from reaching recipients. The EasyDMARC data shows that 62.7 percent of Fortune 500 companies have achieved p=reject, proving this is achievable even for the most complex email environments.
Phase 4: Maintain and Monitor
- DMARC is not set-and-forget. Continue monitoring RUA reports for new unauthorized senders, update SPF records when adding new services, and review DKIM key rotation schedules. Use DMARC reporting dashboards to detect anomalies that may indicate spoofing attempts or authentication drift.
6. Action Checklist for 2026
- 1. Check your current DMARC status. Use a DMARC lookup tool to verify your record exists, your policy level, and whether RUA reporting is enabled. If you have no DMARC record, this is your highest-priority action.
- 2. Implement SPF flattening if you use more than five email-sending services. The 10-lookup limit silently breaks authentication for complex organizations. SPF flattening tools solve this automatically.
- 3. Set a 90-day target to move from p=none to p=quarantine, and a 180-day target for p=reject. The Fortune 500 data proves that enforcement is achievable. Every day you remain at p=none, your domain can be spoofed without consequence.
- 4. Verify PCI DSS compliance if you handle payment data. DMARC is now a PCI DSS v4.0 requirement. Non-compliance can result in fines up to $100,000 per month and loss of payment processing capability.
- 5. Require DMARC from your vendors. With 30 percent of breaches involving third parties (Verizon DBIR 2025), your vendors’ email authentication posture directly affects your security. Use DMARC reporting to verify vendor domain authentication.
- 6. Set up a backup MX service. If authentication changes cause temporary delivery issues during your DMARC migration, a backup MX ensures no email is lost during the transition.
Conclusion: Authentication Is the New Baseline
The convergence of mailbox provider mandates, PCI DSS requirements, and global regulatory frameworks has definitively moved email authentication from the ‘nice to have’ column to the ‘must have’ column. Organizations without DMARC at enforcement level now face rejected emails, regulatory fines, increased breach exposure, and brand spoofing risk.
The data shows that enforcement works. Countries with DMARC mandates saw phishing success drop from 69 percent to 14 percent. Fortune 500 companies with 95 percent DMARC adoption and over 80 percent enforcement demonstrate that even the most complex email environments can achieve full protection. And the global trajectory is clear: DMARC adoption grew from 27.2 percent to 52.1 percent in just three years, driven by regulatory pressure.
But adoption is not enforcement. With 525,996 domains still at p=none and only 411,935 at enforcement level globally, most organizations remain exposed. The gap between having a DMARC record and having it actually protect you is the difference between compliance theater and genuine security.
The organizations that will thrive in this environment are those that treat email authentication not as a checkbox but as a foundational security control — one that protects deliverability, prevents spoofing, satisfies regulators, and builds the trust that modern business depends on.
References & Sources
All statistics cited in this article are from primary-source reports. Full URLs provided.
[1] EasyDMARC, 2026 DMARC Adoption & Enforcement Report [Web]
https://easydmarc.com/blog/ebook/dmarc-adoption-report-2026
[2] EasyDMARC, 2025 DMARC Adoption Report [PDF]
https://easydmarc.com/blog/ebook/easydmarc-dmarc-adoption-report-2025/
[3] EasyDMARC, DMARC Adoption: Fortune 500 vs. Inc. 5000 (July 2025) [Web]
https://easydmarc.com/blog/dmarc-adoption-across-fortune-500-and-inc-5000-the-growing-divide/
[4] EasyDMARC, 2026 Report Press Release (April 2026) [Web]
https://easydmarc.com/blog/easydmarc-releases-2026-dmarc-adoption-report
[5] Mimecast, Guide to Google DMARC Setup — PCI DSS & Provider Requirements [Web]
https://www.mimecast.com/blog/guide-to-google-dmarc-setup/
[6] IBM / Ponemon Institute, Cost of a Data Breach Report 2025 [PDF]
https://www.bakerdonelson.com/webfiles/Publications/20250822_Cost-of-a-Data-Breach-Report-2025.pdf
[7] Verizon, 2025 Data Breach Investigations Report (DBIR) [PDF]
https://www.verizon.com/business/resources/reports/dbir/
[8] FBI Internet Crime Complaint Center (IC3), 2024 Annual Report [PDF]
https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf
[9] KnowBe4, Phishing Threat Trends Report Vol. 5 (March 2025) [PDF]
https://www.knowbe4.com/hubfs/Phishing-Threat-Trends-2025_Report.pdf
[10] ENISA, Technical Implementation Guidance on NIS2 v1.0 [PDF]
[11] CISA, Phishing Infographic — Cybersecurity Performance Goals [PDF]
https://www.cisa.gov/sites/default/files/2023-02/phishing-infographic-508c.pdf
[12] DuoCircle / DMARC Report, Email Authentication Essentials Guide [PDF]
[13] Microsoft, Digital Defense Report 2025 [PDF]
[14] World Economic Forum, Global Cybersecurity Outlook 2026 [PDF]
https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2026.pdf