The Journey of SPF, DKIM, and DMARC- The Three Fortifiers Against Phishing and Spoofing!
DMARC has already gained the attention it deserves, owing to its efficiency in combatting phishing and spoofing attacks. But the journey wasn’t fast and steady from the beginning. It all started when SPF came into play, followed by the amalgamation of Yahoo’s DomainKeys and Cisco’s Identified Internet Mail (IIM). This blog covers the journey of all three email authentication protocols in detail.
SPF’s Birth
In 2000, experts felt the need for a technology that could identify genuine and authentic senders of emails. However, nobody made any significant efforts toward this. But after two years, Dana Valerie Reese came up with an SPF-like technology while being under the impression that this type of solution had never been discussed before.
This is how the journey unfolded-
The First Phase
Dec 14, 1997- Ideation
Jim Miller proposed the concept of verifying SMTP Mail From address using outbound SMTP DNS records.
March 27, 2000- Public Mention of the Concept
Bill Cole shared the idea of developing mail Sender DNS records on the Usenet newsgroup. These records were intended to capture a domain’s outgoing email servers.
June 1, 2002- David Green’s Mail Transmitter RR Came into Existence
David Greens published a mail transmitter RR draft with a new DNS type, that was, MT DNS RR. His draft was later placed in other IETF drafts.
June 2, 2002- Paul Vixie’s Repudiated Mail-From Draft
Paul Vixie came across David Green’s post and sent a draft called “Repudiating MAIL FROM” to the mailing list of name droppers.
December 2, 2002- Hadmudt Danish Developed the First RMX Draft
Hadmut Danisch brought forth the primary version of RMX. RMX is a DNS RR for simple SMTP sender authentication. His draft revolved around the then-newest DNS RR type RMX to publish IP4 network block or redirection to the APL record.
March 28, 2003- Gordon Fecyk’s First DMP Draft
Gordon Fecyk developed Version 00, followed by Version 01 and Version 02 of the Designated Sender’s protocols. These protocols proposed a DNSBL-like technology and permitted the use of RFC2821 mail-from. A few years later, Version 03 was also introduced and addressed as DMP.
June 10, 2003- SPF-discussion Mail List by Meng Weng Wong
SPF was not a publicly-available technology until 2003. It was Meng Weng Wong who released the first version of SPF in June 2003. At that time, SPF stood for Sender Permitted From and not Sender Policy Framework.
August 18, 2003- Wayne Schlitt’s ‘mx’ Mechanism
Wayne Schlitt proposed the ‘mx’ mechanism, which tells which email servers will be used when an email is relayed.
August 19, 2003- David Saez’s ‘spf include’ Operation
David Saez introduced the ‘include’ mechanism, which allows domain owners to add email-sending sources of third-party vendors that send emails on their behalf.
October 1, 2003- Beginning of the ASRG Mail From
SPF was merged into a single proposal for checking Mail From.
October 8, 2003- Change of DNS Type
It was Paul Wouters who suggested replacing the inefficient TXT record type with the DNS RR type. Parallely, Meng also encouraged the same.
October 10, 2003- Introduction of the v=spf1 Version
Meng Weng Wong published proper SPF rules for open discussions.
The Second Phase
The next important stage was the introduction of Sender ID, which was achieved by combining SPF with Microsoft’s Caller ID for emails. However, the concept faced licensing challenges, resulting in a conflict in the industry. Many organizations chose to support SPF independently, holding a significant juncture in SPF’s journey.
Even after the obstacles, SPF didn’t lose its worth; it was just a matter of time and a few alterations that made SPF a fortifier against phishing and spoofing.
DKIM’s Birth
DKIM came after SPF’s development, as a protocol that could effectively handle forwarded emails and verify the integrity of message content during transit. The DKIM protocol is the amalgamation of Cisco’s Identified Internet Mail (IIM) and Yahoo’s DomainKeys, hence the name DomainKeys Identified Mail.
Cisco’s IIM enhances outgoing emails with cryptographic signatures, ensuring they originate from authorized and legitimate sources. This process serves as a defense against malicious actors attempting to infiltrate a company’s email system and launch phishing attacks. Verification occurs at the receiver’s end and involves Mail Transfer Agents (MTAs) or Mail User Agents (MUAs).
Meanwhile, Yahoo’s DomainKeys focuses on verifying that a message’s content remains unaltered during transit. It employs a rapid binary assessment method, swiftly determining whether emails should be directed to the inbox or spam folder based on signatures and an original pair of public and private keys.
Early adopters of DKIM included Gmail, Fastmail, AOL, and Yahoo, and usage rapidly expanded over time.
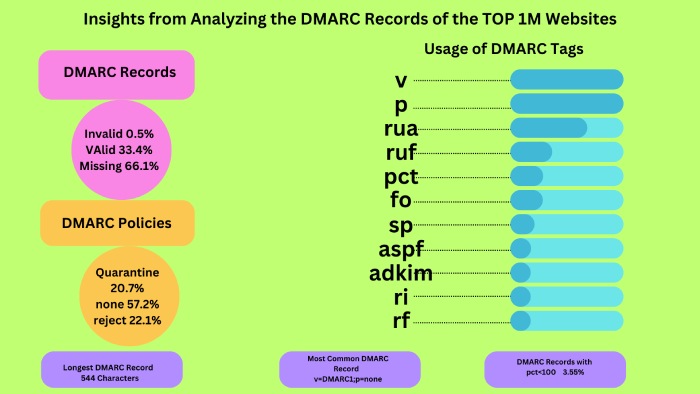
DMARC’s Birth
DMARC’s development was first discussed in 2010 as the users and industry experts came across the shortcomings of SPF and DKIM. So, 15 prominent tech companies came together and collaboratively addressed the problem by pooling their expertise and resources toward the creation of an email authentication protocol that could overcome the shortcomings of SPF and DKIM. In fact, tech giants like PayPal, Microsoft, Yahoo, and Google were also involved.
The main aim was to give recipients’ mail servers the power to provide feedback to senders’ domains regarding the authentication status of received messages. This feedback mechanism now enables senders to refine and enhance their email security practices. The initial specification of DMARC was released on January 30th, 2012.
There was never a doubt about DMARC’s effectiveness; however, its adoption was a bit slow at the start. It wasn’t propagated properly, which is why many IT and cybersecurity professionals remained unaware of its existence, contributing to its limited uptake.
However, notable developments occurred in 2015 and 2016 when tech giants like Google and Yahoo implemented stringent email security policies, including the incorporation of DMARC. These actions were intended to incentivize businesses to deploy comprehensive email authentication protocols.
After 2018, private companies were ahead of government bodies in DMARC adoption. However, significant progress has been made in recent years. Notably, in the UK, it has become mandatory for all government services to adhere to DMARC compliance.
Starting in February 2024, Google and Yahoo have mandated DMARC for bulk and regular senders under different specifications and conditions. This requirement is expected to revolutionize the email authentication journey.