What is the Difference Between DomainKeys and DKIM?
Both these terms sound alike, so some people get confused and use them interchangeably. However, doing so isn’t right. DKIM, which stands for DomainKeys Identified Mail, is a successor to Yahoo’s DomainKey or DK.
To understand this better, we’ll have to rewind a little to the past.
In the early 2000s, industry experts recognized the need to improve email security to combat email-based frauds and spam while fostering trust and reliability in email communication. To achieve this goal, a proposal was made in 2004 to combine Yahoo’s DomainKeys and Cisco’s Identified Internet Mail (IIM) to form the DKIM standard.
While the protocols serve similar purposes, they have some key differences. DomainKeys is now obsolete and has been replaced by DKIM.
What is DomainKeys?
DomainKeys is a deprecated email authentication protocol developed by Yahoo. It worked by adding a digital signature to the email message header using public-key cryptography. This signature was generated using a private key that corresponded to a public key stored in the openly accessible DNS records of the sender.
What is DomainKeys Identified Mail or DKIM?
DKIM also resolves the same purpose but uses an open standard, making it simpler for email service providers to interpret and interoperate efficiently. DKIM also attaches a digital signature to the email header using public key cryptography.
The Key Differences
Both technologies had similar objectives of verifying the senders’ authenticity but involved different approaches and implementations. By merging these technologies, the developers could leverage the strengths of each approach and create a more comprehensive solution. So, let’s see what differences they have.
1. History and Development
DomainKeys
It was created by Yahoo in 2004 in collaboration with Cisco and was one of the earliest attempts to secure email through sender authentication.
DKIM
DKIM was the successor and evolved version of DomainKeys, which was developed by a consortium of tech giants, including Yahoo, Cisco, Microsoft, etc. It was made public in 2007.
2. Keys
DomainKeys
This method involved the use of a single private key that the sender uses to add a digital signature to an outgoing email. The corresponding public key was published in the DNS records of the sending domain.
DKIM
DKIM uses a pair of keys – a private key for signing outgoing emails and a public key published in the DNS records of the sending domain.
3. Signature Placement
DomainKeys
The digital signature was added to the entire message body and selected headers.
DKIM
DKIM offers the flexibility in selecting which parts of an email to sign. It can sign specific headers, the body, or both.
4. Compatibility
DomainKeys
DomainKeys had limited adoption and is largely deprecated in favor of DKIM.
DKIM
DKIM is widely adopted and supported by major email providers and servers, becoming the de facto standard for email authentication.
5. Security Features
DomainKeys
DomainKeys prevented email-based spamming, spoofing, and phishing attempts.
DKIM
In addition to preventing email-based spamming, spoofing, and phishing attempts, DKIM has the ability to include a hash of the message body in the signature. This allows verification of the integrity of the email’s content.
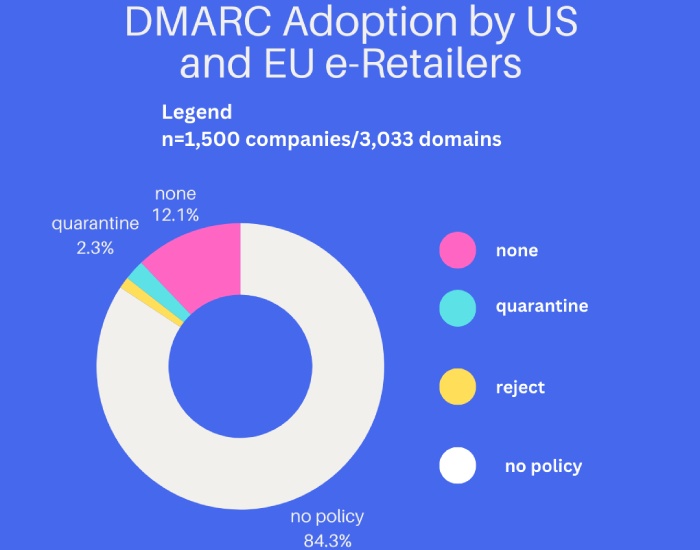
SPF, DKIM, and DMARC combat email-based menaces and largely compensate for each other’s shortcomings, becoming a wholesome combination.