Gmail 550-5.7.26 Error For Emails Failing DMARC Checks

Quick Answer
Gmail's `550-5.7.26` error means the message failed both SPF and DKIM and was rejected for failing DMARC. Starting February 1, 2024, Gmail enforces sender requirements with two tiers. For senders sending under 5,000 emails/day: SPF or DKIM, spam rate under 0.3%, no impersonating gmail.com From headers, TLS in transit, ARC for forwarded mail, and valid forward and reverse DNS. For senders over 5,000/day, all of the above plus SPF, DKIM, and DMARC published, no use of gmail.com to send via external platforms like Mailchimp, and a one-click unsubscribe link in marketing mail. SPF authorizes sending IPs via a TXT record (use ~all for softfail or -all for hardfail). DKIM signs outgoing mail with a private key; the public key in DNS lets recipients verify. DMARC builds on SPF and DKIM alignment, with policies p=none, p=quarantine, or p=reject.
Gmail 550-5.7.26 Error For Emails Failing DMARC Checks

“Unable to send email to Gmail: This message does not pass authentication checks (SPF and DKIM both 550-5.7.26 do not pass).”
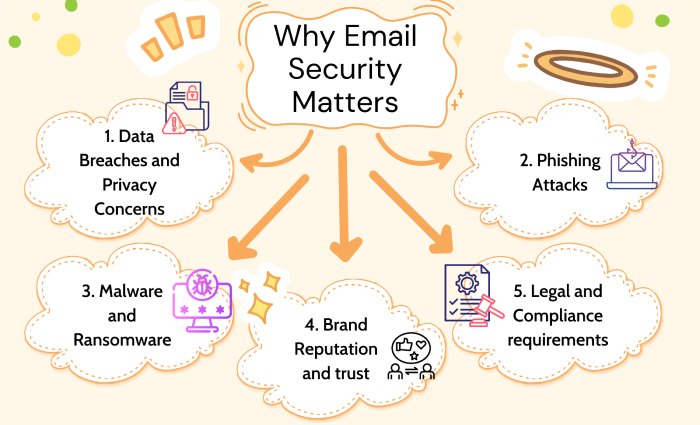
If you are sending out emails to Gmail subscribers and receiving this error message, then it means Gmail has rejected the entry of your messages as they failed DMARC authentication checks. In short, Gmail has now mandated the deployment of SPF, DKIM, and DMARC to combat phishing, spamming, and spoofing.
Let’s see how the lack of email authentication protocols can harm your business and how you can fix it.
Why Is Gmail Returning the “550 5.7.26: This Mail is Unauthenticated” Error?
Gmail rejects the entry of messages to its users’ inboxes if senders don’t comply with its requirements and policies. Moreover, it can also permanently block your email accounts or domains if this practice continues for long or is too frequent.
Here are some possible reasons why Gmail can block your emails starting February 1, 2024:
For email senders sending less than 5,000 emails every day:
- Your domain lacks SPF and DKIM protection.
- Your email spam rate is over the acceptable limit of 0.3%.
- You are impersonating the Gmail From: Headers.
- The TLS connection is missing.
- ARC is not enabled for forwarded emails.
- Your forward and reverse DNS records are invalid.
For email senders sending more than 5,000 emails every day:
- You have not implemented SPF, DKIM, and DMARC for your domain.
- Your domain’s email spam rate is more than 0.3%.
- You use the gmail.com domain to send emails from an external platform like Mailchimp.
- The TLS connection is missing.
- ARC is not enabled for forwarded emails.
- Your forward and reverse DNS records are invalid.
- There is no easy-to-unsubscribe button in your emails.
Understanding Email Authentication
You need to start complying your domains with Google’s new policy to stop receiving the “550 5.7.26: This Mail is Unauthenticated” error.
There are three email authentication protocols, namely SPF, DKIM, and DMARC, that check if the sender is genuinely allowed to send emails on behalf of the business and domain owner. Any email failing these authentication checks doesn’t appear in recipients’ inboxes.
The idea behind this concept is to minimize the likelihood of recipients opening a fraudulent email and engaging with it in any manner. So, if a phishing email doesn’t show in the inbox, the target won’t open it.
Here’s a more detailed explanation of these protocols and how they work-
SPF- Sender Policy Framework
SPF works on the principle of allowlisting or whitelisting. So, a domain owner starts by creating a list of email servers and IP addresses used by senders authorized to send messages from their domain.
Then, they create an SPF record, which is a TXT-type record, and include the above-gathered email servers and IP addresses in it, followed by SPF syntaxes. SPF syntaxes instruct recipients’ mailboxes on treating unauthorized emails sent from your domain.
You can include a SPF softfail or hardfail mechanism. As per a softfail, recipients mark illegitimate emails as spam. On the other hand, by choosing a hardfail, domain owners instruct recipients’ email servers to reject the entry of illegitimate emails.
DKIM- DomainKeys Identified Mail
DKIM is based on the concept of matching cryptographically secured pair of keys for checking an email sender’s authenticity and ensuring that nobody altered the email content in transit.
The sender’s mail server uses a private key to sign outgoing emails, and the public key is published in the domain’s DNS records. When an email is sent, the DKIM signature is added to the email header, serving as a unique identifier.
Upon receiving the email, the recipient’s mail server retrieves the public key from the DNS records and uses it to verify the DKIM signature. If the signature is valid, it confirms that the email originated from the claimed domain and has not been altered in transit.
DMARC- DomainBased Message Authentication, Reporting, and Conformance
DMARC is based on the authentication results of SPF and DKIM. The primary intention behind deploying DMARC is to instruct recipients’ mailboxes on how they should deal with emails that fail SPF and/or DKIM checks.
Domain owners have the choice to set one of the three policies in their DMARC records to give instructions-
- p=none: Take no action against emails failing SPF and/or DKIM checks.
- p=quarantine: Place emails failing SPF and/or DKIM checks in the spam folder.
- p=reject: Bounce back emails failing SPF and/or DKIM checks.
Adding an Easy Unsubscribe Option is a Must
Apart from staying compliant with email authentication protocols, Gmail also wants senders to include a clear and easy unsubscribe link on top of every message so that recipients can opt out whenever they want, thus filtering out spam and non-useful emails.
This also works in the favour of senders- how? Well, with the easy unsubscribe option, there will be fewer instances of blocking a particular sender. So, your senders’ reputation will not take a toll.
Still Confused?
It’s already February 2024, and if you are still confused and unsure about implementing SPF, DKIM, and DMARC, then let us help you. The process can be a bit overwhelming, especially for tech noobs, but our team can take all the worries from you, ensuring top-notch email security and guaranteeing that your emails successfully reach Gmail inboxes. So, should we get on a call?
Topics

General Manager
General Manager at DuoCircle. Product strategy and commercial lead across the email security portfolio.
Secure your email infrastructure
Protect, authenticate, and deliver. Contact our team to find the right solution.