Google and Yahoo are Making it Mandatory to Deploy DMARC For Anyone Sending More Than 5,000 Emails Per Day

Quick Answer
Effective February 2024, Google and Yahoo require all senders to authenticate email and keep spam complaint rates under 0.3%, with stricter rules for senders sending more than 5,000 messages per day. All senders need SPF (TXT record listing authorized IPs and mail servers, with `~all` softfail or `-all` hardfail) and DKIM (cryptographic public/private key signing). Bulk senders (>5,000/day) also need DMARC (p=none, p=quarantine, or p=reject), one-click unsubscribe, and From-header alignment with the SPF or DKIM domain. As of 2021 there were over 5 million unique DMARC records, but adoption of p=reject remains low: only 152 of 1,930 U.S. .edu domains, and 3.3% of .edu domains worldwide, were at reject. Domains without DMARC by the deadline risk delivery problems with Gmail and Yahoo.
Google and Yahoo are Making it Mandatory to Deploy DMARC For Anyone Sending More Than 5,000 Emails Per Day

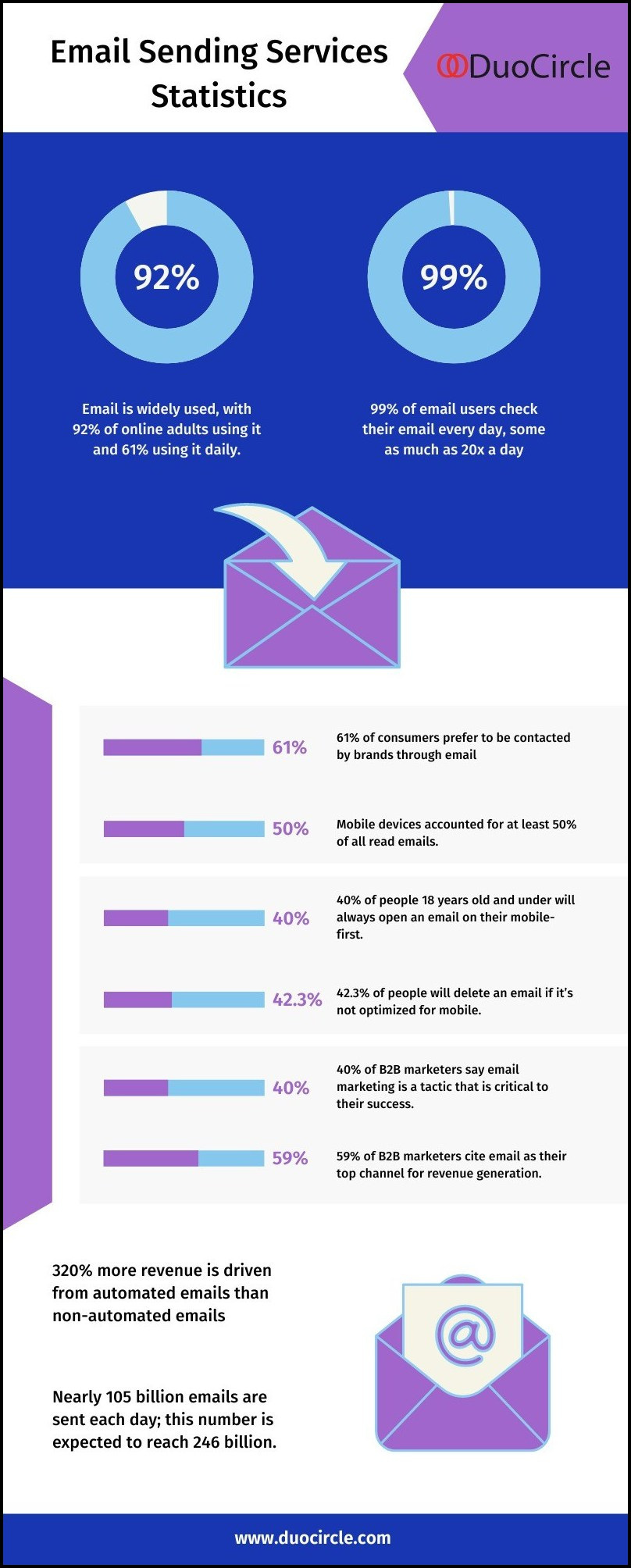
Email service providers have been constantly trying to cut off all possible ways hackers exploit to send phishing and spoofing emails. Recently, Google has made another announcement according to which any company sending more than 5,000 emails per day is required to deploy DMARC to minimize the likelihood of recipients receiving fraudulent and phish-y messages. Moreover, incorporating the one-click unsubscribing feature has also become mandatory to ensure receivers aren’t bombarded with hundreds of unwanted marketing emails.
Yahoo has also announced the requirement of similar mechanisms in place to send emails using its mailing services. Senders will be required to have strong email authentication protocols to be in place by February 2024 to prevent phishing and spoofing.
Google and Yahoo’s Requisites for All Senders
Anyone using Google and/or Yahoo’s email services is now obligated to abide by these two rules:
1. Email Authentication
Email authentication is the practice of verifying the sender’s identity to ensure they are actually who they are claiming to be. SPF, DKIM, and DMARC are three common email authentication protocols that help recipients’ mail servers filter legitimate and illegitimate senders.
SPF
SPF is short for Sender Policy Framework. SPF involves the creation of an SPF record that compiles a comprehensive list of IP addresses and mail servers authorized to send emails on behalf of your company or brand. This compilation encompasses sending sources such as employees, CXOs, third-party vendors, and others.
In addition to enumerating sending sources, SPF employs specific syntaxes to convey details and guide recipients’ mail servers on handling unauthorized emails originating from your domain. The SPF ‘all’ mechanism is particularly instrumental in this process; ‘~all’ (soft fail) instructs a recipient’s server to categorize suspicious messages into the spam folder, while ‘-all’ (hard fail) mandates the rejection of such messages.
This methodology aims to reduce the risk of recipients, potential targets of phishing attacks, opening potentially deceitful messages, and falling prey to cyber exploitation.
DKIM
DKIM, short for DomainKeys Identified Mail, utilizes cryptographic methods to perform authentication checks and ascertain whether the content of a message has been altered during transit. A DKIM signature is affixed to the header of an outgoing email, and this signature is validated at the recipient’s end.
To initiate DKIM, an administrator generates a pair of cryptographically protected public and private keys. The domain owner securely retains the private key, while the public key is made accessible in the DNS for retrieval by recipients’ servers for verification purposes.
Upon receipt of an email from your domain, the recipient’s server retrieves the public key to decrypt the DKIM signature attached to the email header. If the decrypted signature aligns with the calculated hash of the email content, the email is deemed authentic and is confirmed to have remained unaltered during its journey.
DMARC
DMARC, which stands for Domain-Based Message Authentication, Reporting & Conformance, operates in conjunction with SPF and DKIM outcomes to verify the authenticity of an email. Its primary role is to prevent email spoofing and phishing by providing guidelines on how recipients’ mail servers should handle unauthorized messages originating from your domain.
DMARC grants domain owners the authority to specify how mailbox providers should treat unauthorized emails originating from their domain. The DMARC record allows you to define the following policies:
- None (p=none): Also known as the monitoring policy, this option involves no action against unauthorized emails. It serves as a monitoring mechanism.
- Quarantine (p=quarantine): In this policy, unauthorized emails are directed to recipients’ spam folders, acting as a precautionary measure.
- Reject (p=reject): With this policy, unauthorized emails are outrightly returned, providing a more stringent approach to preventing their delivery.
As per DMARC.org, there are over 5 million unique DMARC records as of 2021. The adoption of these protocols has increased over the years; however, not many domain owners have been able to reach the highest level of email security, which is the p=reject policy.
A Campus Technology report states an alarming statistic: only 152 out of the US’ 1,930 .edu domains and 3.3% of worldwide .edu domains have implemented a “reject.” We hope efforts made by Google and Yahoo escalate the adoption and switch to the strictest DMARC policy.
2. Low Spam Rates
Spam messages or unsolicited junk marketing emails serve no purpose other than just cluttering recipients’ mailboxes and irritating them. To reduce this, Google and Yahoo are now going to report your emails as spam or block them if they exceed the new .3% spam rate.
Google and Yahoo’s Requisites for Senders Dispatching 5000+ Emails Per Day
For senders sending more than 5000 emails each day, Google and Yahoo have announced to follow the above-mentioned criteria along with something more. More includes a one-click unsubscribe feature, and alignment of the From: header with either the SPF or DKIM domain.
DuoCircle is Your Saviour Here
So, if you don’t have DMARC in place, then missing the deadline can be detrimental to your domain’s email deliverability, which can consequently impact communication at multiple levels. DuoCircle helps in DMARC deployment, management, and reporting which makes the game against malicious actors easier and more effective.
DuoCircle is awarded as the G2 Momentum Leader Winter 2023 and G2 High Performer Winter 2023. We feel proud of achieving global deployments of 25,000 with an impressive inbox delivery rate of 99% and 99.99% uptime. So, join us in our mission to make the cyber world a safer place and stay compliant with Google and Yahoo’s requirements.
Topics

General Manager
General Manager at DuoCircle. Product strategy and commercial lead across the email security portfolio.
Secure your email infrastructure
Protect, authenticate, and deliver. Contact our team to find the right solution.