by Brad Slavin | Mar 28, 2024 | Data Privacy
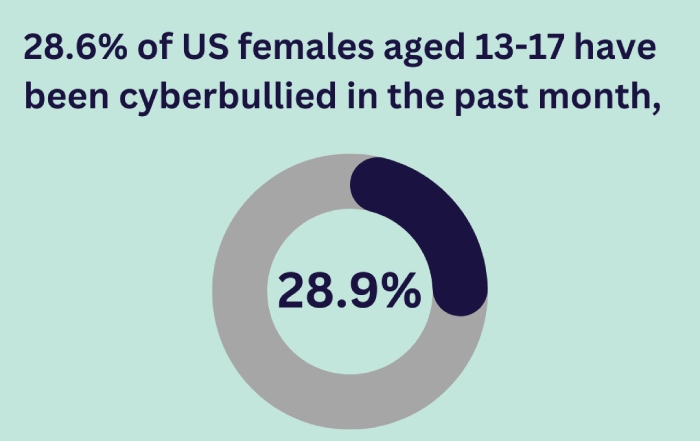
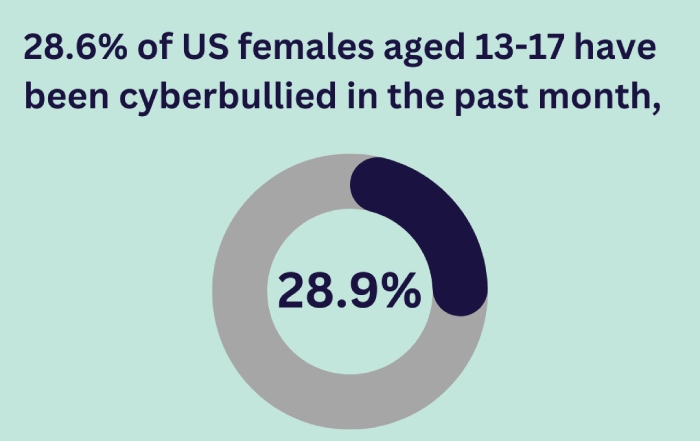
Do your children take lessons or play games online? Do they spend significant time on the internet downloading songs or simply browsing through the treasure trove of information available online?
(more…)

by Brad Slavin | Mar 27, 2024 | Data Privacy
National security is generally associated with protecting the borders, but in this hyperconnected digital world, there’s more to ensuring a nation’s safety than just safeguarding the borders from external threats.
(more…)
![Spa Email Compromised, X Malicious Redirect, CISA China Cyber – Cybersecurity News [March 18, 2024]](https://www.duocircle.com/wp-content/uploads/2024/03/email-sending-services-1.jpg)
by Brad Slavin | Mar 26, 2024 | Announcements
This week, we bring you the latest in cybersecurity that will help you stay a step ahead of the latest threats. From the phishing scam of the Spa Grand Prix and the malicious telegram links on X (Twitter) to the latest releases by CISA and the FTC on Chinese threats and impersonation scams. Plus, the details of the ‘Earth Krahang’ threat actor group that has compromised 70 organizations in 45 countries. Stay tuned!
(more…)

by Brad Slavin | Mar 21, 2024 | Phishing Protection
Phishing is an umbrella term for several kinds of tricks and scams attempted online. For example, there’s ‘credential phishing,’ which is when threat actors steal your passwords or login information. Then, there’s ‘spear phishing,’ which is more targeted and personalized. They might use information about you to make their scams seem more believable. Another type is ‘vishing,’ which involves phone calls instead of emails, where they try to get personal information from you over the phone.
(more…)
![Another Instance of Nissan Data Breach: 100K People Affected Across New Zealand and Australia]()
by Brad Slavin | Mar 20, 2024 | Data Privacy
Nissan, the Japanese car manufacturing company, experienced a mind-boggling ransomware attack on December 5, 2024, resulting in a complete frenzy across Australia and New Zealand. This is not the first time that Nissan has come under the radar of cybercriminals. Earlier, this automobile company faced attacks such as proof of concept exploitation, source code leak issues, and data breach cases. Apparently, the notorious Akira ransomware gang is the mastermind behind this cyber scam. They have claimed to have scraped a whopping 100GB of data.
(more…)
by Brad Slavin | Mar 19, 2024 | Email Security
We are in 2024, and it’s officially the era of email authentication, especially after Google and Yahoo made it mandatory for organizations to protect their email ecosystem with SPF, DKIM, and DMARC. Now that email authentication has become the new norm; enterprises have no other choice but to level up their cybersecurity game by implementing robust email authentication protocols.
(more…)
![French Agency Breach, PixPirate’s Stealth Technique, Fake Wallet Scam – Cybersecurity News [March 11, 2024]](https://www.duocircle.com/wp-content/uploads/2024/03/dkim-selector.jpg)
by Brad Slavin | Mar 18, 2024 | Announcements
Here we are again with the latest inside scoop on the cybersecurity highlights of the week. We’ll share details of the data leak in France’s job-seeking portal, the latest advancements of PixPirate Android malware, the fake “Leather” wallet crypto drainer application on the App Store, the Russian attack on Microsoft, and the arrest of a former Google employee who stole cutting-edge AI tech from the organization. Stay tuned!
(more…)

by Brad Slavin | Mar 14, 2024 | DMARC
DMARC isn’t a new regime; however, regulations and email service providers have now made it mandatory. This exercise is meant to reduce phishing and spoofing by filtering genuine and fraudulent emails. DMARC works in accordance with SPF and DKIM to instruct recipients’ servers to either reject or mark illegitimate emails as spam, reducing the likelihood of victims engaging with such emails and getting manipulated.
(more…)
by Brad Slavin | Mar 13, 2024 | Phishing Protection
Clop Ransomware was first discovered by Michael Gillespie in 2019. It’s a developing family of ransomware that encrypts all data in a company’s digital ecosystem, and hackers demand money to decrypt and give back access. The malware is packed covertly and smartly to hide its inner workings.
(more…)

by Brad Slavin | Mar 12, 2024 | Email Security
If you have a website’s IP address and don’t know its domain name, you would need to perform a PTR lookup. A PTR record, which is short for a Pointer Record, is the opposite of an A record; an A record translates domain names into their corresponding IP addresses, and a PTR record translates IP addresses into their corresponding domain names.
(more…)

![Spa Email Compromised, X Malicious Redirect, CISA China Cyber – Cybersecurity News [March 18, 2024]](https://www.duocircle.com/wp-content/uploads/2024/03/email-sending-services-1.jpg)

![French Agency Breach, PixPirate’s Stealth Technique, Fake Wallet Scam – Cybersecurity News [March 11, 2024]](https://www.duocircle.com/wp-content/uploads/2024/03/dkim-selector.jpg)