FTC Boosts Blackbaud, Teams DarkGate Spreads, FBI Disrupts Chinese Botnet – Cybersecurity News [January 29, 2024]
We’re back with the latest cybersecurity news of the week to deliver a concise overview of all the new threats and attacks you need to stay safe from. We’ll take a look at the FTC’s mandate on Blackbaud, the disruption of the Chinese botnet by the FBI, the new phishing attacks on Microsoft Team chats, USB malware that turns your devices into crypto miners, and the ransomware attack on Kansas City area transportation. Let us get into it.
FTC Mandates Blackbaud to Improve Security Following Data Leak
Blackbaud has settled with the FTC on the charge of poor security and reckless data retention following the ransomware and data breach of May 2020.
The US-based organization has operations in multiple countries and provides cloud-based donor data management software. The FTC issued a complaint, sharing that the organization failed to monitor hacking attempts on its networks, did not segment its data, or even deleted the data that was no longer needed. They also said that Blackbaud did not implement MFA properly or test its security controls, which led to weak passwords in employee accounts.
The FTC has ordered a settlement that also states that Blackbaud has to improve its security measures and make sure it deletes customer data that is no longer needed. Apart from this, the organization has been barred from portraying its data security inaccurately and will have to create an information security program.
The FTC shared details of the shortcomings, highlighting that Blackbaud paid the ransomware gang that stole 24 bitcoins and the personal data of millions from its systems but never verified or checked if the hacker deleted the stolen data.
Phishing Attacks on Microsoft Teams Spread DarkGate Malware Through Group Conversations
New phishing attacks have been making use of the group chat in Microsoft Teams to push malicious attachments for malware.
The threat actors use a compromised Teams user and send thousands of group chat invites. The attack was analyzed by AT&T research, who shared that once the person accepts the chat request, the threat actors trick them into downloading files with double extensions as “.pdf.msi” – which is a common tactic of DarkGate. It installs the DarkGate malware on their devices and connects to the Command and Control (C2) server.
MS Teams has nearly 280 million monthly users, which makes it an attractive target for threat actors. DarkGate is a huge threat as it has concealed VNC, Windows Defender bypasses, and browser history theft tools, along with data token stealers.
AT&T has warned that you should disable External Access in MS Teams unless it is absolutely necessary and should provide phishing awareness training to employees so they can identify where unsolicited messages come from and keep phishing attempts at bay.
FBI Intervenes to Dismantle Chinese Botnet, Removing Malware From Compromised Routers
The FBI was able to disrupt the KV Botnet being used by Chinese Volt Typhoon threat actors.
The KV Botnet was used by the threat actors to evade detection while targeting US critical infrastructure. The capable tool could allow malicious actors to evade detection in DrayTek Vigor routers, Cisco RV320s, Axis IP cameras, and even the Netgear ProSAFE. The VoltTyphoon malware allowed the Chinese to hide network exploitation and pre-operation reconnaissance, which makes this a huge win for the FBI.
They began the operation on 6 December 2023, hacked into the C2 server, and sent commands to compromised devices to cut them off from the Chinese botnet. The FBI and CISA have issued guidance for manufacturers of SOHO routers so they can secure against Volt Typhoon’s ongoing campaign.
They also provided recommendations to include automatic updates, remove all security flaws in design and development phases, and allow web management interface access only from the LAN by default.
Cybercriminals Distribute USB Malware Through News and Media Websites
A threat actor has been using USB devices to infect other devices with hidden payloads.
The payloads are hidden with the help of benign content such as forum user profiles or video descriptions. When a victim opens a malicious LNK shortcut file on the USD, it starts a PowerShell script that downloads payloads that decode to a URL, which the threat actors use to download and install malware on victim devices. The threat actors behind the attack are being tracked by Mandiant as UNC4990 and have been using multiple approaches to host intermediary payloads.
The attacks do not exploit any vulnerabilities in the sites but use regular site features like an About page or a video description to host the payload without raising any concerns. Once the malware EMPTYSPACE is installed, it downloads a backdoor called QUIETBOARD from the C2 server and crypto coin miners, showing that the threat actor is financially motivated.
The prevention is pretty straightforward – not to trust any USB devices, but people often ignore this and become victims of such attacks. Implementing effective malware protection solutions can significantly reduce the risk associated with using USB devices.
Kansas City’s Public Transport System Targeted by Ransomware Attack
The Kansas City Area Transportation Authority (KCATA) has shared news of a ransomware attack that hit them on 23 January 2024.
The bi-state public transit agency has a fleet of 300 buses that operate on 78 bus routes, serving nearly 10.5 million customers a year. KCATA shared that they were the victim of a ransomware attack that affected its communication systems. All of its regional RideKC call centers and KCATA landlines were unable to receive calls but all of its other services were operating normally.
KCATA shared alternate phone numbers for people who need to schedule trips and has also contacted all the authorities, including the FBI. A major concern was data theft, which came true when the Medusa ransomware gang claimed responsibility for the KCATA attack and posted a data sample from KCATA on their extortion page.
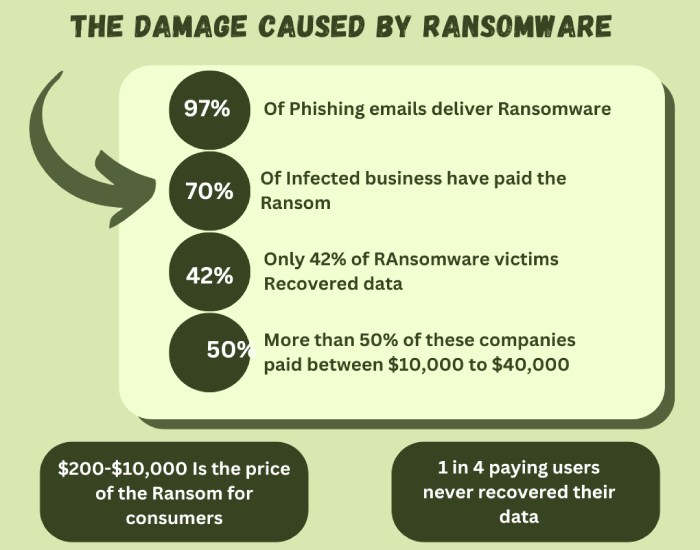
As of now, the threat actors have given the organization 10 days to come to common terms and settle with the ransom of $2 million. Medusa has also given a $100,000/ day to extend the deadline and keep them from posting the stolen data. A robust ransomware protection solution can safeguard businesses from the devastating impacts of ransomware attacks.